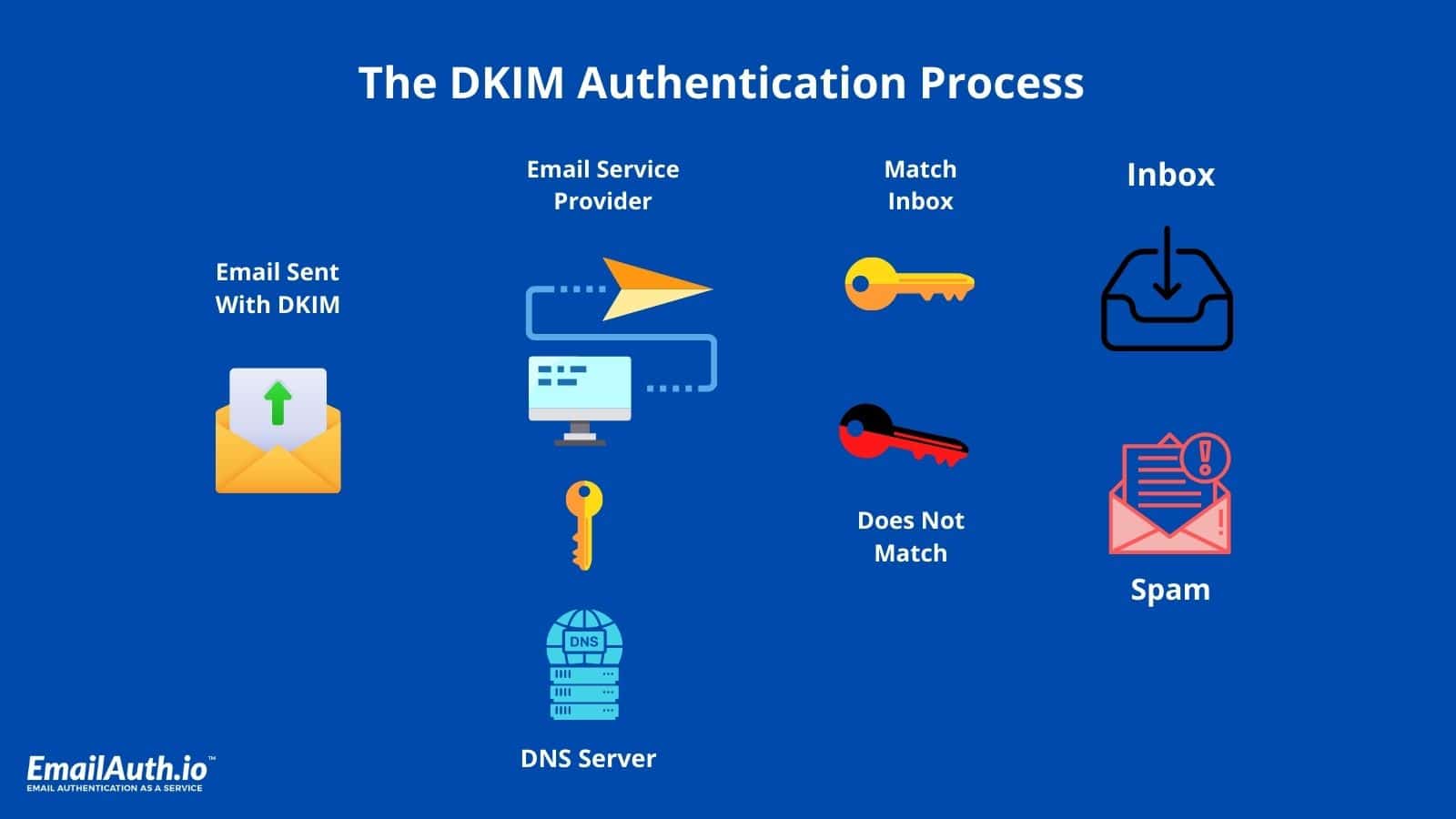
DomainKeys Identified Mail (DKIM) is an anti-tamper protocol that secures your emails while in transit. It uses digital signatures to confirm whether the email was sent by an authentic domain.
The first DKIM action occurs on the server that sends a DKIM signed email, while the second takes place on the recipient server that checks DKIM signatures on incoming emails. The entire process is made possible by a pair of private and public keys.
The private key is kept secret and safe either on your own server or with your ESP. The public key, on the other hand, is added to the DNS records of your domain to broadcast to the world and help verify your emails. This is done by providing a digital signature for the email. Once the receiver verifies that an email is signed with a valid DKIM signature, it’s clear that the integrity of the email is preserved.
Usually, DKIM signatures are not visible to end-users and the validation occurs at the server level.
Benefits of DKIM
For email receivers, the key benefit of DKIM is that it allows the signing domain to accurately identify a stream of legitimate emails, making domain-based blacklists and whitelists more effective. It also helps counter email-based cyber attacks by offering the following advantages:
1. Spam filtering
DKIM can help identify mail that isn't known to be spam and does not need to be filtered. If a receiving system maintains a whitelist of authentic sending domains that can be kept locally or obtained from third-party certifiers, it can skip the filtering of signed emails from those domains and filter the remaining emails more aggressively.
2. Compatibility
DKIM is compatible with the existing email infrastructure because it is implemented using DNS records and an extra RFC 5322 header field. It is especially apparent to existing email systems that do not support DKIM.
3. Anti-phishing
DKIM can be used to defend against phishing attacks. Mailers in intensively phished domains can sign their emails to prove their authenticity. The absence of a valid signature on an email from these domains can be interpreted by recipients as a clue that the email is most likely forged.
4. Non-repudiation
The non-repudiation feature of DKIM does not let senders deny that they have sent an email. This has been essential to news organizations as they have been able to use DKIM body signatures to confirm that leaked emails were authentic and untampered with.
DKIM's email identity authentication also aids in the global management of cyberattacks. The DMARC (Domain-based Message Authentication, Reporting, and Conformance) protocol was created in 2015. To combat email fraud such as phishing and spoofing, it uses SPF and DKIM. The basic concept is to protect a brand's domain. This is how DKIM protects brands from getting phished or spoofed.
Only by being honest about domain verification and the integrity of their own procedures can brands be completely secure. Email Service Providers must provide specialized branded DKIM authentication to segregate reputation on each individual transmitting brand and prevent reputation mixing.
Despite the benefits, the DKIM protocol has a few drawbacks that could be exploited by attackers. They are as follows:
A. The message envelope that contains the return path and message recipients is not covered by DKIM signatures.
B. Because DKIM does not sign all sections of the message and only authorizes certain headers, malicious actors can forge the email by adding more header fields.
C. The information validated by DKIM is only on the server-side. End-users do not benefit much from the fact that an email is validated by DKIM.
DKIM limitations such as not encrypting emails, not signing all sections of the email message and only authorizing certain headers saw an increase in demand for a more secure and holistic email authentication protocol. DMARC was developed looking at these limitations.
DMARC works in alignment with DKIM and SPF to fight email fraud and fend off cyberattacks. A domain that is DMARC compliant is much more reputed; hence, every brand should ensure proper email authentication setup. Read more about DMARC here. If you’re already familiar with DMARC and want to check your existing DMARC record, use our free DMARC record checker tool.
These limitations have led to the development of subsequent protocols like BIMI, which does a great deal to fill the gap. However, BIMI should be used as a tool to make brands understand the importance of email authentication and encourage them to adopt DMARC, DKIM, and SPF.
Original Source:- https://www.idg.com.au/mediareleases/204971/protecting-brand-identity-and-reputation-using/