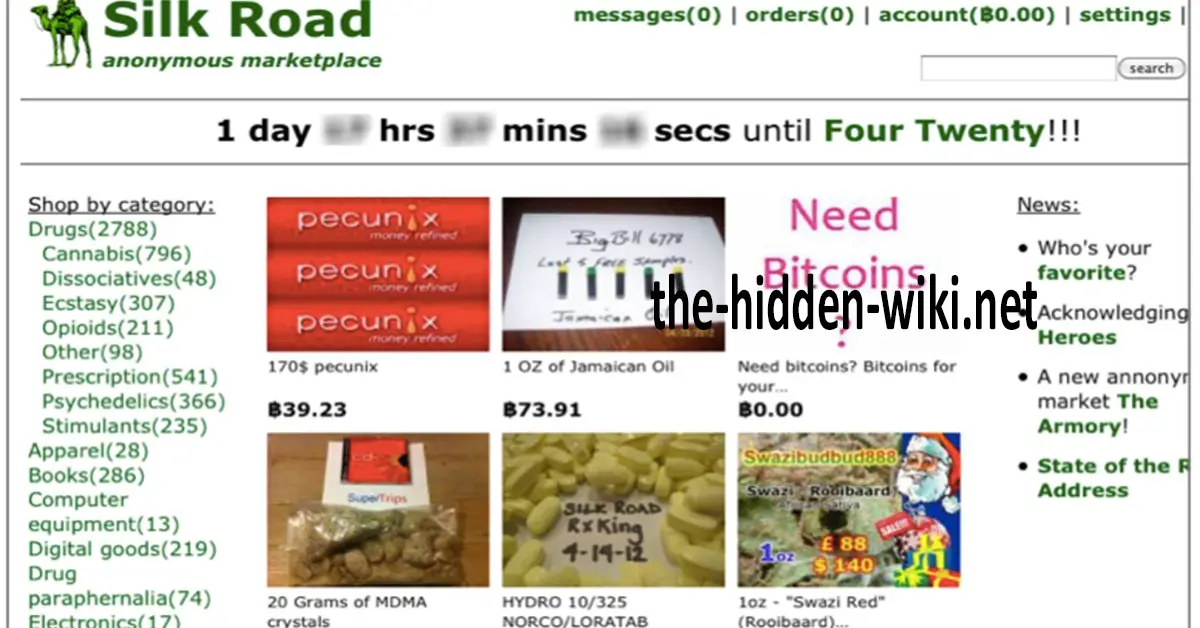
The “dark web” is an expression that broadcasts a foreboding vibe, passing on an impression of a commercial center where anything is available to be purchased: hacking devices, weapons, drugs, kid sexual entertainment, even independent death administrations. Furthermore, as per the specialists we addressed, the entirety of that is still obvious. In any case, something has changed in the manner in which the dull web works together. On the off chance that some time ago wandering on the web to purchase these illicit things resembled taking your life in your grasp in a dim rear entryway, today the experience is very unique.
Consume medications, similarly as an illustration class. “The best similarity I can give for the span of dull web drug contributions is that it would resemble strolling into a significant general store interestingly having just at any point shopped at a corner store,” says Emily Wilson, head of the investigation at Terbium Labs. “Nearly anything you need is accessible from a gigantic host of sellers—every one of whom is contending to guarantee purchasers that their item is the freshest, most flawless, most secure, most promptly guaranteed high accessible. Individuals like to thoroughly analyze their encounters indefinite reviews, and the merchants are boosted to create dedication: ‘Look at this gift of my new item,' or ‘Hello, sorry about the lethargic transportation—I tossed in some extra for you.'”
What's more, it's not simply tranquilizing where the dim web has gone corporate. It's occurring in all cases—and what a large portion of the specialists we addressed needed to discuss was particularly the different hacking and shadowy innovation administrations accessible. In hearing the subtleties, it's difficult to dodge the acknowledgment that the different crooks on the dim web are following the acts of corporate IT.
Furthermore, similarly likewise with corporate IT, the unlawful contributions from the dull web range from code that purchasers need to execute themselves to turnkey arrangements and counseling administrations.
Items: Malicious code available to be purchased, with directions
Adventures and assault code can be insidiously intricate to find or work without any preparation. The dim web furnishes a commercial center that interfaces developers with the required abilities with those with inspirations to release them. Ido Wulkan, insight leader at IntSights, focuses on a few malware bundles available to be purchased on the dull web, including Dr0p1t-Framework, a trojan that downloads other malware, and the Silent Word abuse, which changes over a malignant. EXE record into an honest appearance. DOC.
Purchasers of these endeavors shouldn't be ace programmers themselves. “In the event that you have generally minimal specialized information,” says John Shier, a senior security master at Sophos, “there are guides on the best way to spread your malware, and furthermore phishing and checking instructional exercises.”
Administrations: No compelling reason to do it without anyone's help
However, similarly, as numerous ventures at this point don't assemble or even convey their own in-house apparatuses, so too do numerous crooks re-appropriate the organization of their offenses. Regardless of whether you're tired of the unending “- as-a-administration” abbreviations in IT (Software-, Infrastructure-, Platform-), you'll have to add another: RaaS, or ransomware-as-a-administration.
[ Prepare to turn into a Certified Information Security Systems Professional with this extensive online course from PluralSight. Presently offering a 10-day free preliminary! ]
“RaaS suppliers give their clients completely useful ransomware with a dashboard to follow casualties and backing administrations should they need it,” says Shier. “In return, the creators of the RaaS gateway request either a level of the payment or a level charge. The solitary thing left is for the client to circulate the ransomware, potentially utilizing the administrations of a spammer bought independently or by doing it without anyone else's help utilizing the information they acquired from the instructional exercises.” And in the event that you need more proof of this, in reality, specialists are presently starting to see the Petya ransomware as a RaaS assault. What Zombies Can Teach You About hidden wiki
Ransomware is just one of an assortment of assault choices, obviously. Nathan Wentzler, the central security specialist at AsTech, says that on the dull web you can pay for “more focused on game plans that can go too far from wicked or ‘simply one more assault' to unlawful assaults to acquire explicitly licensed innovation, public guard or military data, and other touchy (and significant) information.”
Foundation: Why purchase on the off chance that you can lease
There are a lot of more commonplace IT benefits that cybercriminals need, and normally, these are likewise accessible on the dim web. Email workers, for example: “The capacity to send and get your mail in an unknown manner is vital for some, for great and for awful,” says Chris Roberts, boss security modeler at Acalvio. You can likewise purchase PC time on different sorts of workers. “Consider them AWS for the darknet,” says Roberts. “Some consideration what content you have and some don't.”
Furthermore, in case you're hoping to set yourself up as the following Dread Pirate Roberts—indeed, you will require a foundation to sell things, and once more, the dim web can give. “A gathering calling itself ‘TeamZero' is selling a bootleg market system, which permits ‘traders' to sell pretty much anything on the dull web,” says Wulkan. “They give a turnkey framework, much the same as eBay or Shopify—however for illicit merchandise and ventures.”
Outlines, counseling and that's only the tip of the iceberg
In case you're hoping to dodge work (and try not to get your hands messy), the dim web will associate you with programmers willing to counsel on explicit errands at a particular cost. Let's assume you're hoping to break a specific association. “While you may not discover association explicit assault outlines, similar to the cliché clique test document, you can discover things like IP addresses, worker areas, or gadget passwords just as for directions for executing explicit assault types on the deep web,” says Stu Bradley, VP of online protection arrangements at SAS. “These are sufficient for the gifted foe to start an effective mission. Or then again, in case you're excessively occupied or maybe do not have the expertise to execute an assault yourself, why not subcontract it out to a programmer? You can without much of a stretch discover a programmer to lead the assault with an ensured administration level and cashback in case no doubt about it.”
Visit Our Website: the-hidden-wiki.net