Theintersection of email best practices and technical knowledge can be tricky, sowe’re going to break down a few things you need to know about DKIM. Then, togive you some extra hands-on experience, we’ll walk you through DKIM from endto end: we’ll explain how it works, why it matters, and how you can start usingit.
DKIM’s Role in Deliverability
Here’s how DKIM works to boost inbox deliverability. When an email arrives in a recipient’s inbox, they open it and decide whether to trust the message. Their decision largely comes down to one question: from the sender’s email address, is this a trustworthy message? More simply, does the sender look like a spammer? To answer that question, the recipient (or their mail server) needs to be able to determine if the sender has a valid domain associated with their message.
If so, then there is increased trust in the message’s senders. Basic email deliverability tips: To give a simple explanation with no technical details included, the idea is that DKIM can help your emails appear more reputable -- you are claiming authorship of all email sent from your domain. This helps prevent consumers who receive multiple email messages from the same domain but with different names from becoming confused.
If you’ve ever received an email from your bank or another organization that looks much different than other emails you receive from them, it may be because they don’t have DKIM set up on their server and With email deliverability becoming more and more of a challenge, DKIM is a new way that can make your email identifiable as coming from you.
With email deliverability becoming more and more of a challenge, DKIM is a new way that can make your email identifiable as coming from you. No matter what kind of business you have, email is a critical tool for building your brand. Since inbox deliverability is never a guarantee, understanding how DKIM affects email deliverability can improve your chances of landing in the inbox rather than the spam folder.
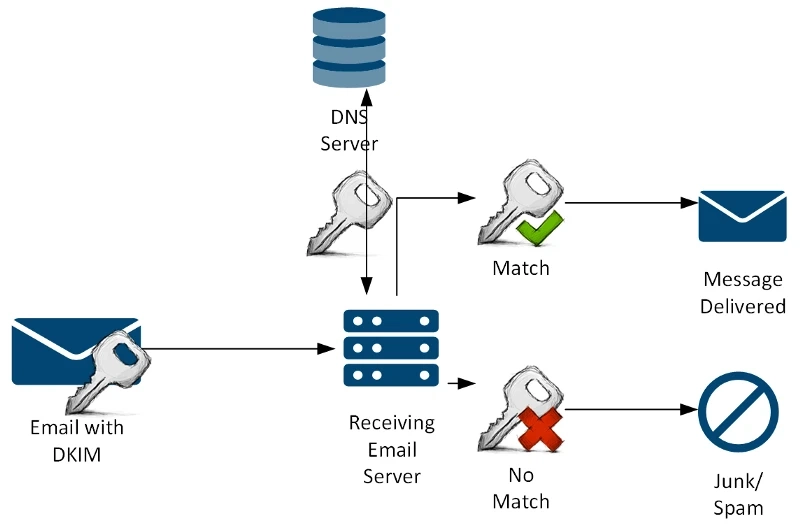
DKIM is an email authentication system designed to detect email spoofing. The basics of how DKIM works are fairly straightforward: a DKIM-enabled domain publishes a public key as part of its DNS records.
The public key is used to digitally sign outgoing messages sent from the domain. Receivers can then use the published public key in order to validate whether a message has been modified or not since it was signed. Properly configured DKIM allows receivers to take appropriate action if a signed message fails its validation check.
DKIM was created to add a digital signature to your emails so that receivers could more easily trust that the email had not been altered between sending and receipt. Now, DKIM is essential in helping deliverability professionals and recipients distinguish spam from legitimate email. Any email you send from your domain will have a DKIM signature appended to it. This signed email shows the receiver that the email actually came from you and hasn’t been modified since it left your server.
This added security is critical to inbox placement, and verified deliverability for your business. DKIM is one of several tools in the email marketing toolbox. Just like a domain name, it’s just one way to prove to your recipients that an email actually came from you. It also adds a measure of security, preventing forged emails that look like they are from your business.
DKIM is a method of assuring the recipient that the message was sent by an authorized source. It also assures that the message didn’t get tampered with in transit. This association is particularly important if you’re using a marketing automation platform or email service provider to send your messages—which you should always have in place if you’re doing any form of email marketing and hope to be CAN-SPAM compliant.
While there are several steps in creating a successful email marketing campaign, this article focuses on the Domain Keys Identified Mail (DKIM) protocol and what it means to your deliverability in the eyes of email recipients. It also discusses how it's crucial to use email service providers with DKIM best practices for your deliverability.
Understanding DKIM is key to message delivery and consumer trust. It's also a necessity for protection against spam and phishing activities. The following is an overview of what DKIM is, why it's important, how it works in tandem with SPF, and how to implement it in your email marketing initiatives.
Why Does DKIM Matter?
DKIM ties directly into your deliverability. If someone believes you are not who you say you are, they will mark you as spam or block your emails and Dkim Mailbox providers (Gmail, Yahoo etc) use a variety of clues to determine if a message is spam or not. One of the biggest indicators is identifying the source of the email.
That’s where DKIM comes in— DKIM is an email authentication system that gives Senders a way to identify themselves to Receivers within messages—and allows Receivers to verify that Claimed Identity. DKIM also provides a mechanism for associating verified identities with messages, so that Receivers can differentiate between valid and invalid sources.
Why, you may ask?
Mail users receive tons of email every day, but there will always be those who use email in a way you don’t want it to be used. Your spam filter combats those people, and is on the lookout for spoofed emails. If your email isn’t properly authenticated, your spam filter might mistake it for a spoofed email. If your email isn’t properly authenticated, the spam filter may see your email as a potentially spoofed email.
If you receive a message that your email was sent by a server other than the one listed in your DKIM record, that domain can also be marked as potentially spoofed. Spoofed emails are filtered into junk folders because they can present a phishing or social engineering risk to your customers and users.
Email authentication is the process of proving your identity by entering your email address and password to a website. This proves to the receiving server that the email really came from you, not from someone trying to impersonate you. While all email systems provide some form of authentication, it’s usually very weak. This is done for simplicity, but also because spoofed emails would pass any stronger authentication test. If you’re using a marketing automation solution or an email service provider, they will block your campaign if they see that it doesn’t have authentication on it.
The way to stop fraudulent senders from imitating your domain is by using DKIM. With DKIM, you can guarantee that messages sent from a particular domain really did come from the domain owner’s email server. Achieving full email authentication is a commitment. If you’re in a line of business—like finance or online payments—where would-be hackers have an incentive to spoof your domain, it’s worth the effort.
source by:-https://atozcybersecurity.blogspot.com/2021/08/how-dkim-affects-email-deliverability.html