If you are a developer, you may have heard the word "OAuth" used to talk about how to keep your apps safe. However, what exactly is OAuth, and why does it matter? This post will talk about the best ways to use OAuth to keep your apps safe from people who don't have permission to use them. So, let us learn how to use OAuth to protect your apps.
Understanding OAuth
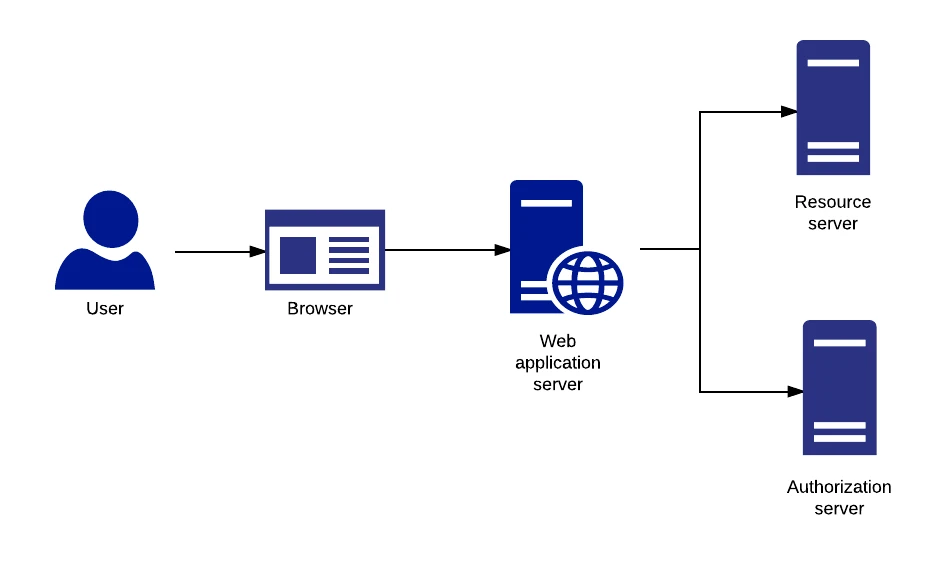
OAuth stands for Open Authorization. A widely used authorization system lets one application access the resources of another application on behalf of a user without sharing the user's passwords. It is like giving someone a key to your house without telling them the code.
Best Practices for Implementing OAuth
Use Secure and Up-to-Date Libraries
Using safe, up-to-date tools or SDKs (Software Development Kits) from trusted sources is important when putting OAuth into your app. These tools have been tested for security thoroughly and are updated often to fix any known problems. Ensure your tools and SDKs are always on the most recent versions to stay safe from security risks.
Implement Secure Redirect URIs
Redirect URIs are where users are sent after giving an application permission to use their resources. It is important to ensure these URIs are safe and controlled so no one can use them without permission. Do not use wildcards in your redirect URIs. Instead, only accept sites that you know and trust.
Use Strong and Secure Client Secrets
When an app requests the OAuth server, the client secret is a hidden key that verifies the app's identity. To avoid unwanted entry, making and keeping these codes safe is important. Avoid putting client secrets in your application's source code, as this can make them easy to find.
Enable Scope-Based Authorization
Through groups, OAuth lets developers tell what amount of access or rights a service needs. Scopes tell the program what tools or tasks it can do on behalf of the user. Scope-based permission is very important, and you should only ask for the bare scope of your service needs.
Implement Secure Token Management
In OAuth, calls between the program, the user, and the OAuth server are authenticated and given permission using tokens. To avoid token leaks and illegal entry, it's important to use safe token-handling techniques. Store tokens in a safe place, like a protected file or a secure token vault, and use access tokens that only work for a short time.
Strategies for OAuth Implementation
Follow the Principle of Least Privilege
Least Privilege is a security concept that says a person or service should only have the access rights it needs to do its job. When adopting OAuth, you should follow this concept by giving the app the least access it needs to do its job. Don't give people access to private resources or rights they don't need. This can increase the risk of data breaches or illegal access.
You can also improve your applications' security by following the Principle of Least Privilege, doing regular security audits, watching for and stopping suspicious activities, educating users, and regularly reviewing and updating your OAuth implementation. Using these best practices and strategies, you can safely add OAuth to your apps and give your users a safe and reliable experience.






Sign in to leave a comment.