Introduction: AI and Machine Learning Revolutionizing Cybersecurity
The digital paradigm forces cyber threats to evolve rapidly, which creates significant security concerns for companies and personal users. Threats are becoming more frequent and increasingly diverse. As the attackers' sophistication rises, conventional security architectures are often inadequate. This is where Artificial Intelligence (AI) and Machine Learning (ML) come in, as they offer sophisticated means to quickly identify, avert, and respond to cyber threats.
The machine learning courses in Hyderabad provide students the opportunity to study AI transformations in cybersecurity for aspiring professionals. Learners who take these courses gain expertise in developing AI-based security solutions to defend digital assets securely.
The Role of AI and Machine Learning in Cybersecurity
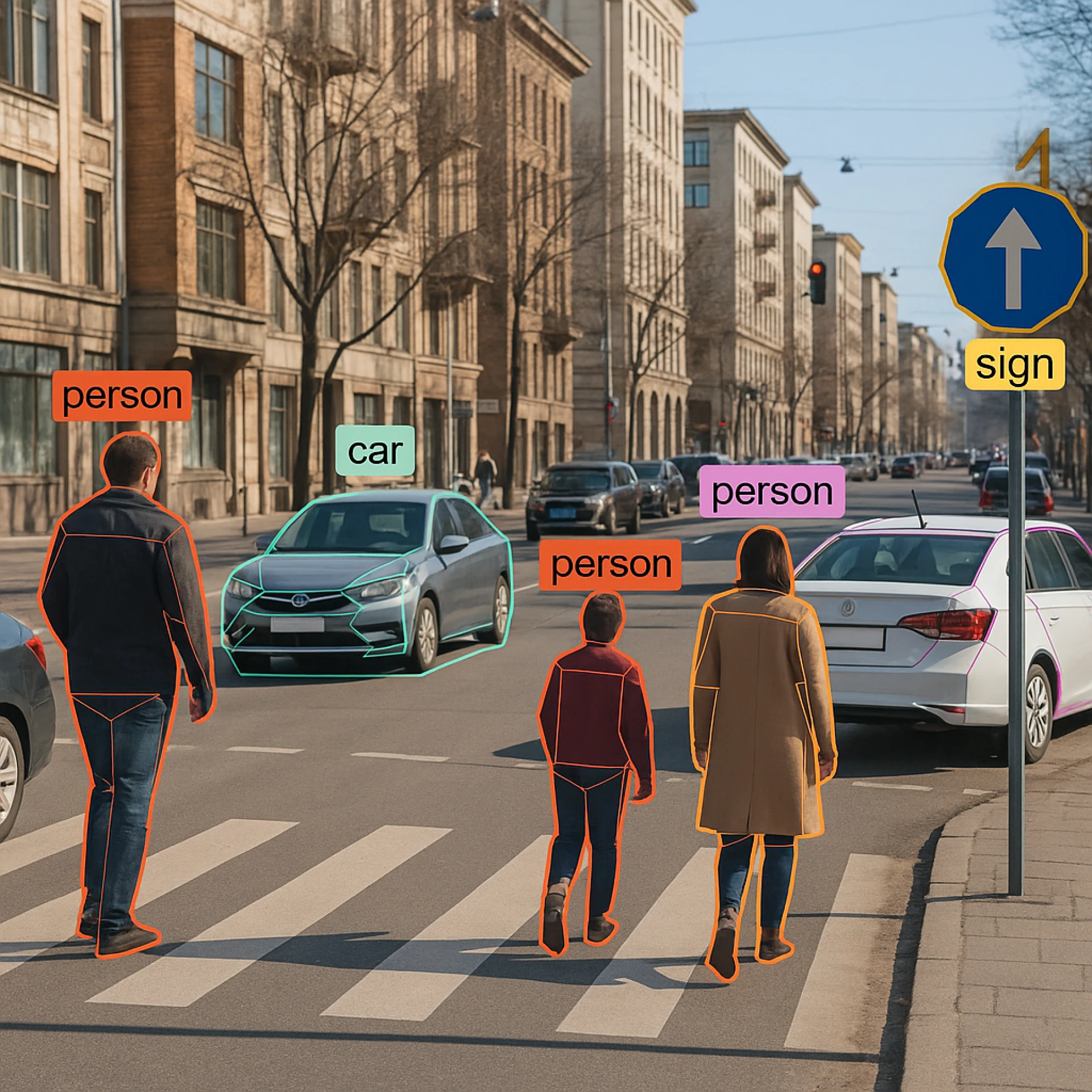
Cybersecurity platforms use AI and ML technologies to increase their real-time predictive capabilities for locating and responding to security threats. AI models detect malicious activities through data analysis and pattern-learning procedures. AI, together with machine learning, provides key support for cybersecurity through the following contributions:
1. Threat Detection and Prevention
Network traffic monitoring by AI-powered security allows continuous threat recognition through pattern-based analysis. Machine learning models using supervised and unsupervised learning algorithms help security systems identify anomalous system behavior and attempted phishing attacks, as well as malware and other potential threats.
Machine learning models under Supervised Learning gain knowledge from labeled data before recognizing established attack patterns.
Unsupervised Learning analyzes network behavior to detect deviations from standard patterns for detecting zero-day security breaches.
2. Automating Incident Response
When AI detects threats, it automatically follows pre-defined actions to execute incident response tasks. Machine learning models detect attack severity automatically to activate emergency response sequences, which function without human involvement, thus accelerating incident management and decreasing security threats.
3. Behavioral Analytics for User Authentication
Behavior analytics powered by AI enables secure user authentication, which automatically detects genuine users and reports unusual system behaviors. Machine learning algorithms inspect user behavioral data, including typing speed and login activities to spot potential cyber threats in user accounts.
4. Phishing and Email Security
Phishing attacks serve as one of the leading cyber threats that Internet users face today. AI systems detect phishing attempts by analyzing messages while tracking sender behaviors together with URL links to automatically stop unauthorized emails from entering users' inboxes.
5. Predictive Threat Intelligence
AI systems collect intelligence from various sources to examine new attack patterns while forecasting probable security risks. The proactive implementation enables organizations to remain ahead of cyber criminals during their activities.
How Machine Learning Enhances AI in Cybersecurity
Through machine learning, AI systems gain the ability to learn from data while achieving better accuracy levels throughout their operation. To succeed in the cybersecurity, professionals need a thorough understanding of ML algorithms and their cybersecurity applications. A machine learning course in Hyderabad equips students with essential knowledge to build cybersecurity protection systems models.
1. Anomaly Detection with Machine Learning
Machine learning algorithms, through clustering and classification techniques perform anomaly detection work by identifying irregular behavior in network systems. The system detects both insider threats and unusual login attempts, along with other suspicious network behaviors, through its monitoring capabilities.
2. Network Traffic Analysis
ML models ' real-time analysis of network data detects unusual patterns that signal potential cyber threats. The analysis tools, including SVM and Random Forest, work together to track deviations from typical network traffic patterns.
3. Malware Detection and Classification
AI models using ML technologies examine file characteristics and behavior patterns to detect malware. The accurate classification of malware is possible through deep learning models, which include convolutional neural networks (CNN) and recurrent neural networks (RNN).
4. Fraud Detection and Prevention
ML models examine transaction records to identify fraudulent activities by detecting irregular patterns that deviate from standard behaviors. ML models acquire knowledge from records to recognize and avert upcoming fraudulent activities.
5. Adaptive Security Systems
AI systems that use adaptive security operate through constant learning processes, transforming into evolved systems by examining fresh information. The systems use real-time threat assessment to determine modifications in security protocols, which protects the effectiveness of cybersecurity measures.
Applications of AI in Cybersecurity
AI, together with ML technology, transforms cybersecurity aspects and results in better proactive security performance. The following list shows actual applications of Artificial Intelligence within cybersecurity:
1. Endpoint Security
Artificial Intelligence through endpoint security solutions tracks network-connected devices for protection functions. Security solutions equipped with ML models help stop attacks while preventing unauthorized system access and maintaining compliance with security standards.
2. Cloud Security
The implementation of AI systems enables better cloud protection through effective detection and prevention of potential threats that affect cloud systems. There are machine learning models that observe cloud activity to secure data protection through the prevention of data breaches.
3. Identity and Access Management (IAM)
AI-powered Identity and Access Management systems authenticate user identities to enforce control measures that protect sensitive information from unauthorized users. Identifying user behavior through ML algorithms, together with behavioral analytics improves verification methods for user identities.
4. Security Information and Event Management (SIEM)
AI-based Security Information and Event Management systems receive security data from many sources for real-time threat investigation through analytical processes. The implementation of ML algorithms leads to more precise threat recognition and response capabilities.
5. Automated Vulnerability Management
AI identifies the system vulnerabilities in an organization to help security teams address issues before attackers can take advantage. ML models leverage historical security data to forecast upcoming security vulnerabilities.
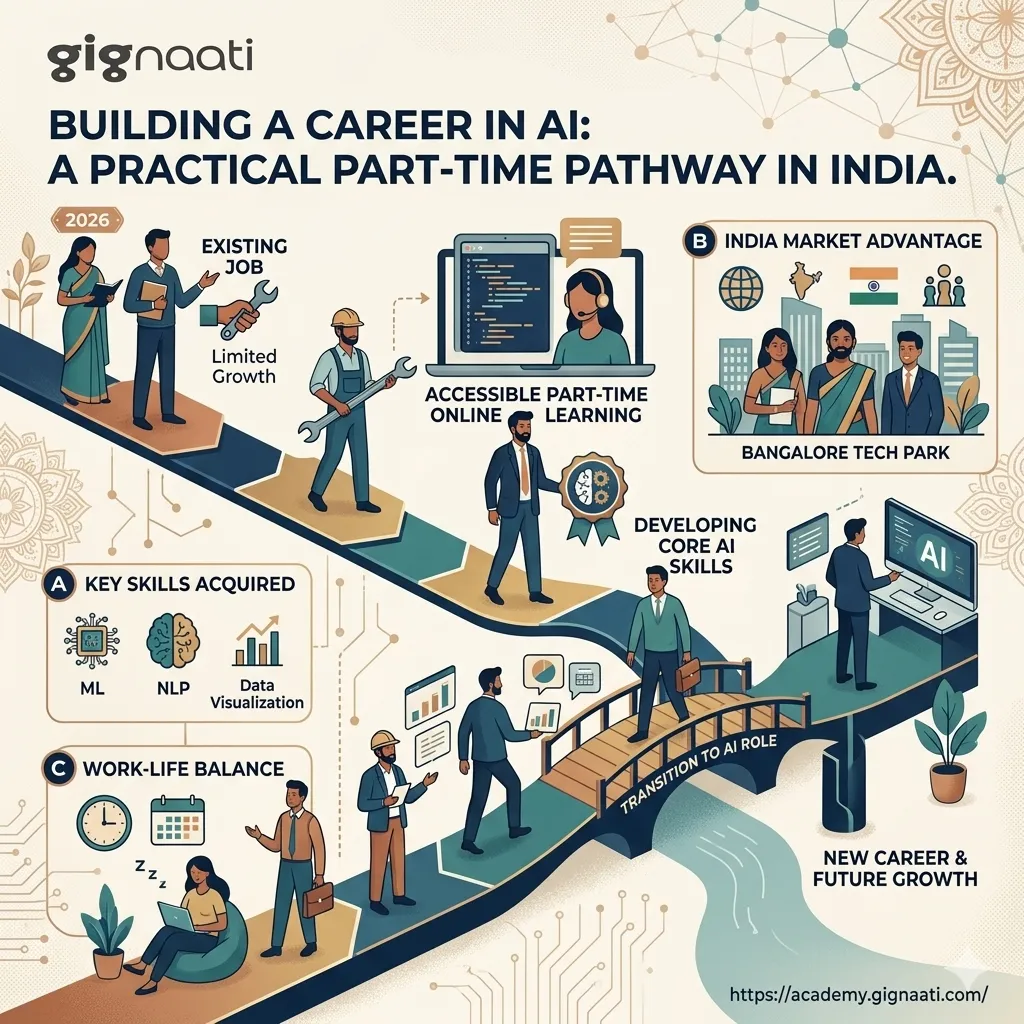
Learn AI and Cybersecurity: Enroll in a Machine Learning Course in Hyderabad
The growing technology and innovation center of Hyderabad has excellent learning opportunities for AI and cybersecurity through specialized machine learning courses. Taking machine learning courses in Hyderabad enables students to build real-world security systems that leverage artificial intelligence.
What to Expect from a Machine Learning Course in Hyderabad
Fundamentals of Machine Learning: Learn the basics of supervised, unsupervised, and reinforcement learning.
Data Preprocessing and Feature Engineering: Master the essential data cleaning and transformation methods, which prepare AI models for improved performance.
Anomaly Detection and Network Security: The analysis introduces Machine Learning detection of anomalous activities alongside its application in protecting network security from cyber threats.
Deep Learning for Malware Classification: Deep Learning techniques enable students to develop skills for detecting malware through threat classification.
Hands-On Projects and Case Studies: Through hands-on projects and case studies, students gain practical experience by applying AI and ML concepts to solve real cybersecurity problems.
The Selection of an Ideal Machine Learning Educational Institution in Hyderabad
To choose the best machine learning institute in Hyderabad, it is required to evaluate the course curriculum with their faculty expertise, industry partnerships and placement assistance programs. The following list represents leading educational institutions throughout Hyderabad that provide machine-learning programs:
Learnbay: Provides both industry-related content and practical project work in its educational programs.
IIIT Hyderabad: Delivers advanced AI and ML programs through a dedicated research-focused curriculum.
360DigiTMG: Provides practical training in AI, ML, and cybersecurity.
ExcelR: Covers a wide range of ML algorithms and security applications.
Great Learning: Offers AI and ML certifications with placement support.
Career Opportunities in AI and Cybersecurity
The increasing usage of AI technology in cybersecurity creates expanding opportunities for experts who can handle AI-based security systems. Career opportunities include:
Cybersecurity Analyst
AI Security Specialist
Machine Learning Engineer
Threat Intelligence Analyst
Incident Response Engineer
Conclusion: Build a Future in AI-Powered Cybersecurity
Cybersecurity receives transformative intelligence-based solutions from artificial intelligence and machine learning as they redefine how cyber threats are addressed. Through a machine learning course in Hyderabad, students learn the skills necessary to use AI properly in cybersecurity practices. Selecting a leading machine learning institute in Hyderabad guarantees students real-world exposure and specialized training that aligns with today's dynamic AI and cybersecurity industry standards.













Sign in to leave a comment.