
As UCaaS platforms replace traditional PBX systems, security expectations change along with them. What used to be a network-level concern now sits squarely inside application logic, APIs, and cloud infrastructure. For engineering teams, this shift often becomes obvious only after the first real security incident or audit.
Secure UCaaS development is rarely about adding more tools. It’s about understanding where communication systems usually fail once they scale.
Security starts showing cracks at the architecture level
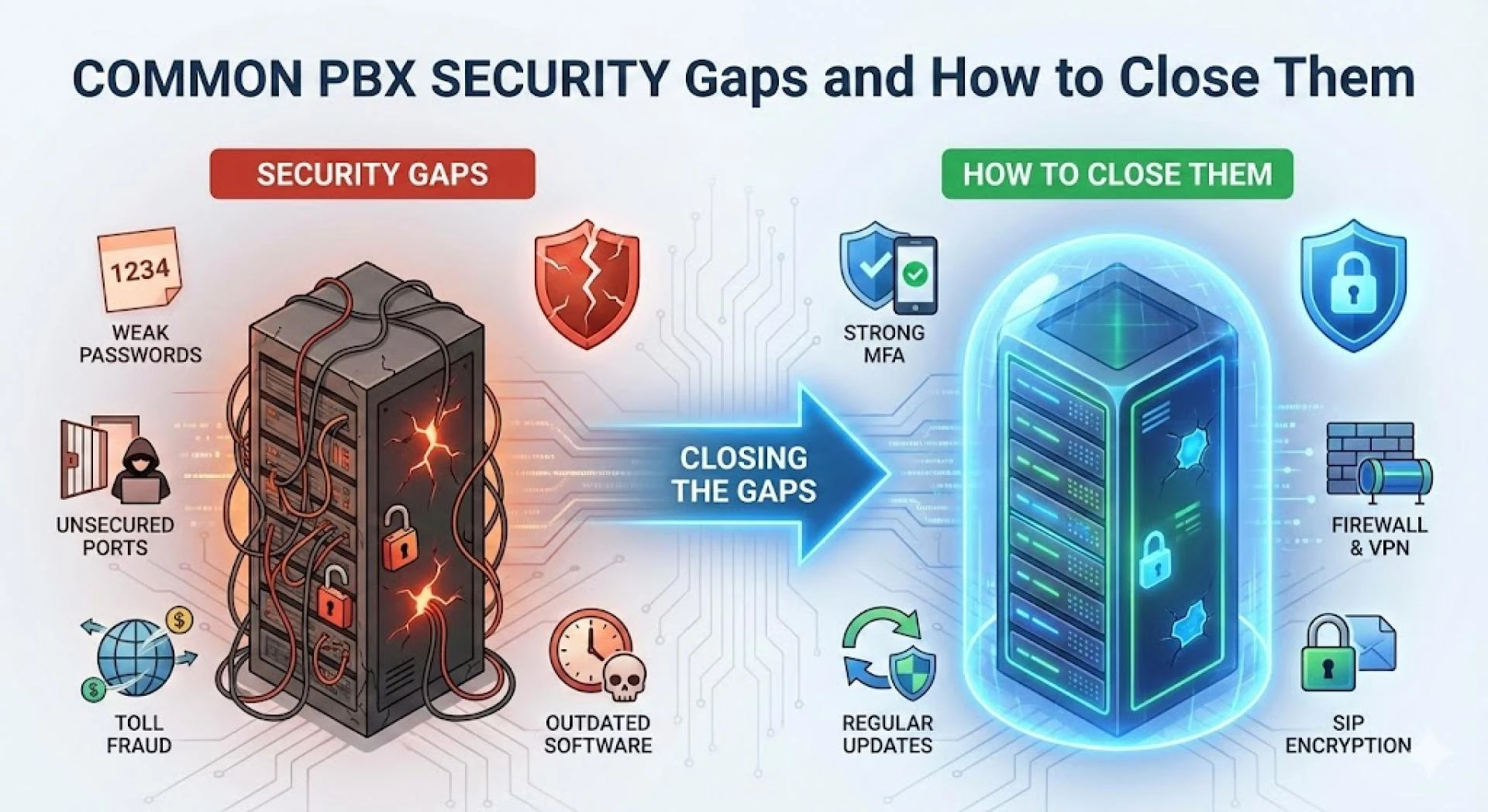
Most UCaaS security issues don’t originate from encryption algorithms or SIP stacks. They appear earlier, during architectural decisions. Monolithic PBX designs, tightly coupled services, and shared trust boundaries tend to magnify small mistakes.
Teams that isolate signaling, media, and application logic early usually experience fewer downstream issues. This separation limits blast radius when something goes wrong and makes security controls easier to reason about later.
Access control becomes harder than expected
As platforms grow, access management quickly becomes one of the most fragile parts of UCaaS Security. Admin roles multiply, integrations expand, and temporary permissions quietly become permanent.
What looks manageable at small scale often turns risky in production. Role-based access control and least-privilege policies aren’t just best practices; they are damage-control mechanisms when systems evolve faster than documentation.
Encryption solves problems but creates new ones
End-to-end encryption is non-negotiable, yet it introduces operational trade-offs. Teams discover that encrypted media streams complicate monitoring, lawful interception, and debugging.
Balancing encryption with observability is where ucaas security and compliance requirements start influencing engineering decisions. This is also the point where security stops being theoretical and becomes operational.
SBCs quietly define your security posture
Session Border Controllers tend to be underestimated. In practice, they end up handling far more than SIP normalization. Traffic anomalies, malformed requests, and abuse patterns often surface at the SBC layer first.
When SBCs are treated as core security components rather than routing utilities, UCaaS platforms gain a much stronger defensive foundation.
Integrations introduce the most unpredictable risks
CRM systems, analytics tools, billing engines, and AI services all expand the attack surface. Most breaches don’t occur because an integration exists but because its permissions were never revisited.
Secure UCaaS development best practices increasingly emphasize treating integrations as untrusted by default, even when they are business-critical.
Monitoring reveals what design reviews miss
Even well-designed platforms behave differently under real traffic. Unexpected call patterns, abnormal retries, and subtle signaling loops only appear once systems are live.
Teams that invest in continuous monitoring tend to detect issues early, before they affect customers or compliance obligations.
Compliance is shaped by engineering choices
Compliance requirements are often addressed late, but they are rooted in early technical decisions. Data storage locations, recording workflows, and access logs all trace back to how the platform was built.
A closer look at secure UCaaS development best practices shows that compliance becomes far easier when engineering teams plan for it from the start rather than retrofitting controls later.
Final thoughts
Secure UCaaS platforms don’t emerge from checklists. They evolve through deliberate trade-offs, careful architecture, and a willingness to revisit earlier decisions.
For engineering teams, security is less about perfection and more about resilience building systems that can absorb change without exposing customers or data along the way.


















Sign in to leave a comment.