From phishing to ransomware, cyber threats are evolving faster than ever. Discover how cybersecurity stays one step ahead in safeguarding your data.
In today's interconnected world, where digital technologies play a central role in both our personal and professional lives, the importance of cybersecurity cannot be overstated. As technology advances, so do the methods and sophistication of cyber threats.
Evolution of Cyber Threats
1. The Rise of Malware Attacks
Malware attacks have become increasingly prevalent and diverse over the years. From traditional viruses and worms to more sophisticated forms like Trojans, ransomware, and spyware, cybercriminals constantly find new ways to exploit vulnerabilities in systems and networks. Malware attacks can lead to data breaches, financial losses, and significant disruptions to businesses and individuals.
2. Advanced Persistent Threats (APTs)
Advanced Persistent Threats (APTs) are highly targeted cyber attacks carried out by skilled adversaries. These attacks involve a prolonged and stealthy intrusion into a network, aiming to gain unauthorized access to sensitive information or disrupt critical systems. APTs often employ sophisticated techniques, such as zero-day exploits and social engineering, making them difficult to detect and mitigate.
3. Social Engineering Techniques
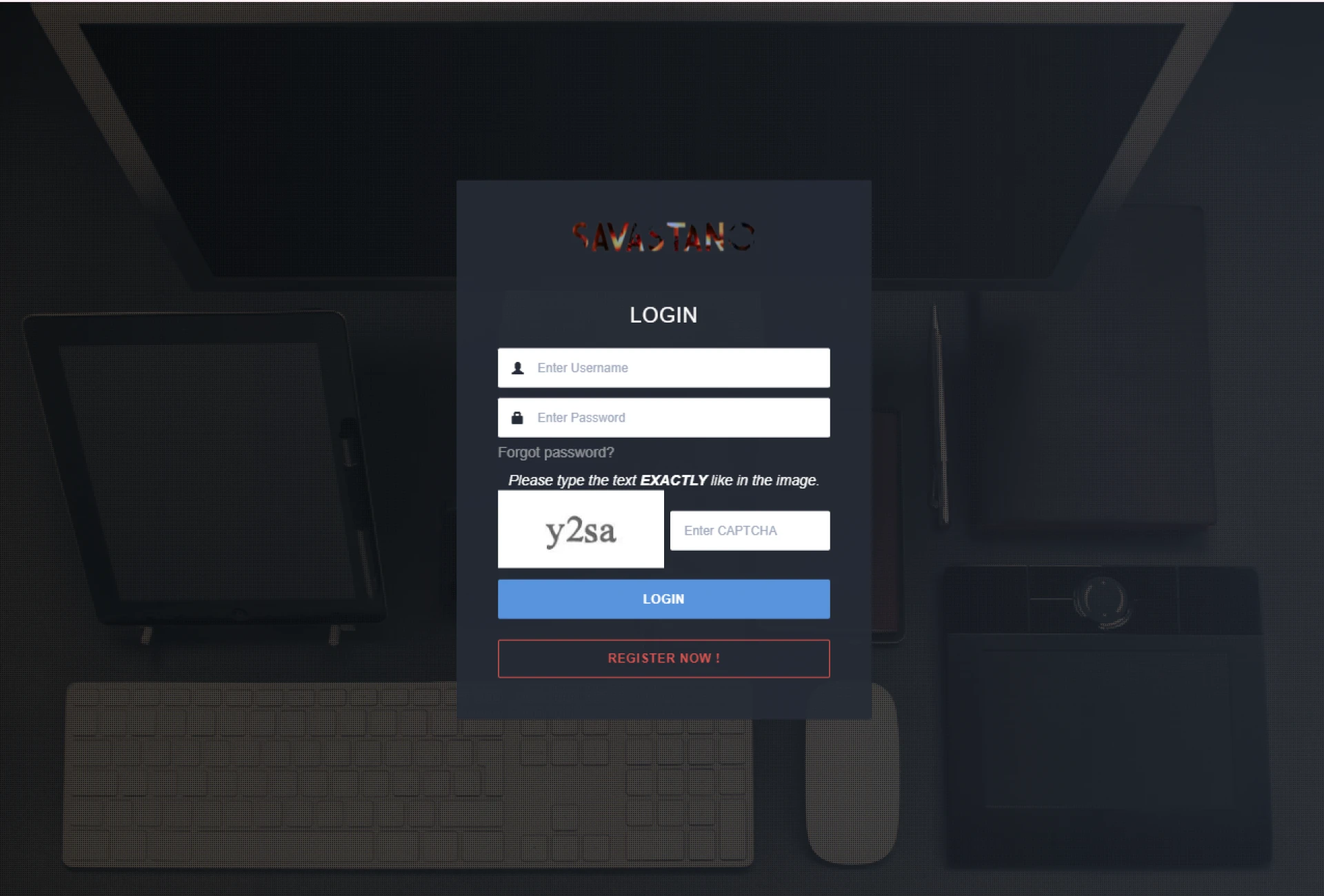
Social engineering techniques leverage human psychology to manipulate individuals into revealing sensitive information or performing certain actions. Phishing, spear phishing, and pretexting are common social engineering techniques used by cybercriminals to deceive unsuspecting users. By impersonating trusted entities or creating a sense of urgency, attackers trick individuals into sharing passwords, financial details, or downloading malicious software.
4. Internet of Things (IoT) Vulnerabilities
The proliferation of Internet of Things (IoT) devices presents new challenges for cybersecurity. IoT devices, such as smart home appliances, wearables, and industrial sensors, often have limited security measures in place, making them attractive targets for hackers. Compromised IoT devices can be exploited to gain unauthorized access to networks or launch large-scale distributed denial-of-service (DDoS) attacks.
Cybersecurity Measures and Technologies
To counter the evolving cyber threats, various measures and technologies have been developed to safeguard digital systems and networks.
1. Antivirus Software and Firewalls
Antivirus software and firewalls are fundamental tools in the cybersecurity arsenal. Antivirus software scans files and programs for known malware signatures, while firewalls act as a barrier between internal networks and external threats, monitoring and controlling network traffic.
2. Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) help detect and prevent unauthorized access and malicious activities within networks. IDS monitors network traffic and alerts administrators of suspicious behavior, while IPS goes a step further by actively blocking or mitigating threats.
3. Encryption and Secure Communication Protocols
Encryption is a crucial technique for securing sensitive data. By converting information into an unreadable form, encryption ensures that even if intercepted, the data remains protected. Secure communication protocols, such as Transport Layer Security (TLS), provide an additional layer of security by establishing encrypted connections between users and websites.
4. Security Awareness Training
Human error is often a weak link in cybersecurity defenses. Security awareness training educates individuals about common threats, best practices for data protection, and how to identify and report potential security incidents. By raising awareness and promoting a security-conscious culture, organizations can significantly reduce the risk of successful cyber attacks.
The Role of Artificial Intelligence (AI) in Cybersecurity
Artificial Intelligence (AI) plays a vital role in modern cybersecurity. AI-powered systems can analyze vast amounts of data, identify patterns, and detect anomalies that may indicate potential threats. Machine learning algorithms can learn from past incidents and continuously improve their ability to detect and respond to emerging cyber attacks. AI also enables automation in threat detection and response, helping organizations defend against cyber threats more effectively.
Emerging Trends in Cybersecurity
As technology continues to advance, new trends and challenges emerge in the field of cybersecurity. Here are some key areas to watch:
1. Cloud Security
As organizations increasingly adopt cloud computing services, securing cloud environments becomes paramount. Cloud security involves protecting data, applications, and infrastructure in cloud-based systems from unauthorized access, data breaches, and other cyber threats. Techniques such as data encryption, identity and access management, and cloud workload protection platforms are essential for ensuring robust cloud security.
2. Mobile Device Security
With the widespread use of smartphones and tablets, mobile device security is critical. Mobile devices often contain sensitive information and have access to various networks and applications. Protecting these devices from malware, unauthorized access, and data leakage is essential to maintain data privacy and prevent financial losses.
3. Blockchain Technology
Blockchain technology offers a decentralized and tamper-proof way to store and verify data. Its immutability and transparency make it a promising solution for enhancing cybersecurity. Blockchain can be used for secure authentication, decentralized identity management, and securing transactions, making it increasingly relevant in various sectors, including finance, supply chain management, and healthcare.
4. Biometric Authentication
Biometric authentication uses unique physical or behavioral characteristics, such as fingerprints, facial recognition, or voice patterns, to verify an individual's identity. Biometrics provide a higher level of security than traditional passwords or PINs since they are inherently linked to the individual.
Frequently Asked Questions (FAQs)
Q1. What is the role of artificial intelligence in cybersecurity?
A1. Artificial intelligence plays a crucial role in cybersecurity by analyzing data, detecting anomalies, and improving threat detection and response capabilities.
Q2. What are some emerging trends in cybersecurity?
A2. Emerging trends in cybersecurity include cloud security, mobile device security, blockchain technology, biometric authentication, and post-quantum cryptography.
Q3. How can individuals protect themselves from cyber threats?
A3. Individuals can protect themselves from cyber threats by using strong and unique passwords, keeping software and devices up to date, being cautious of suspicious emails and links, and using security features such as multi-factor authentication.
Q4. What is the future of cybersecurity?
A4. The future of cybersecurity will involve continuous innovation, collaboration, and the adoption of new technologies and practices to stay ahead of evolving threats. Public-private partnerships and information sharing will play a vital role in combating cyber attacks.




Sign in to leave a comment.