Ethical Hacking:
When we talk about Ethical Hacking, it's explicitly inferred that we're talking about playing that's grounded on ethical or moral values, without any ill intent. Ethical Hacking is defined as any form of hacking that's authorized by the proprietor of the target system. It can also relate to the process of taking active security measures to defend systems from hackers with vicious intentions on data sequestration.
From a specialized viewpoint, Ethical Hacking is the process of bypassing or cracking security measures enforced by a system to find out vulnerabilities, data breaches, and implicit pitfalls. It's only supposed ethical if the indigenous or organizational cyber laws/ rules are followed. This job is formally known as penetration testing. As the name suggests, this practice involves trying to insinuate the system and establishing the way involved in it.
To add it up, an Ethical Hacker hacks the target system before any dangerous hacker can. This allows the security platoon of the association to apply a security patch in the system and effectively exclude an opening for the bushwhacker to enter the system or execute a hack.
Want to learn Ethical Hacking, Join Online Ethical Hacking Course by WsCube Tech helps you learn all aspects of ethical hacking from scratch. You don’t need to have any prior experience in cybersecurity to acquire these skills.
Types of Ethical Hacking
Web Application Hacking: Web hacking is the process of exploiting software over HTTP by exploiting the software’s visual chrome cybersurfer, poking with the URI, or scheming with HTTP aspects not stored in the URI.
System Hacking: Hacktivists gain access to particular computers over a network through system hacking. word busting, honor escalation, vicious software construction, and packet smelling are the protective measures that IT security experts can use to combat these pitfalls.
Web Server Hacking: An operation software database garçon generates web information in real-time. So bushwhackers use Unsticking, clunk deluge, harborage checkup, smelling attacks, and social engineering ways to snare credentials, passcodes, and company information from the web operation.
Hacking Wireless Networks: Because wireless networks use radio swells to transmit, a hacker can fluently gush the system from either a position hard. To discover the Identifier and bodge a wireless network, frequently these assaulters use network snorting.
Social Engineering The art of manipulating the millions so that they discover sensitive information is known as social engineering. Eugenics is used by culprits since it's generally easier to attack your organic hard time trusting than it's to figure out how to imitate your device.
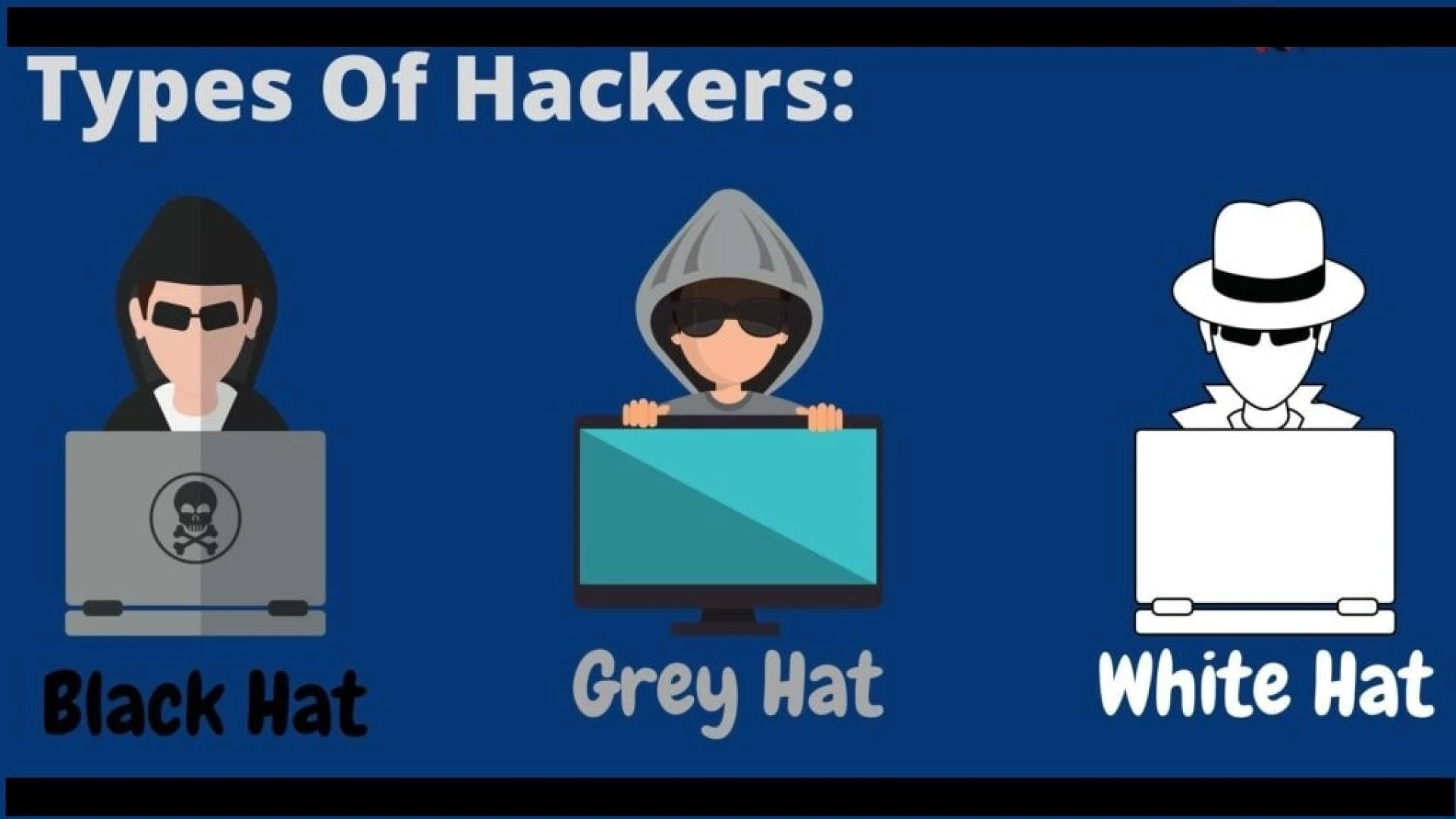
Types of Hackers
A hacker is a person who solves a specialized issue by using a computer, networking, or indeed other capacities. Anyone who uses their chops to gain access to a system or networks in operation to break laws is appertained to as a hacker.
There are different types of hackers
1. White Hat Hackers
On the dark web, these are the right people who come to our aid. White chapeau hackers, also known as ethical hackers, are cybersecurity experts who help the government and businesses by performing penetration testing and relating security excrescencies. Ethical hackers use a variety of ways to cover themselves from black chapeau hackers and other cybercriminals. They break into our system with the good intention of chancing vulnerabilities and aiding you in removing contagions and malware.
2. Black Hat Hackers
These days, black chapeau hackers are the main perpetrators of cybercrime. The maturity of the time, the docket of a black chapeau hacker is financial. These hackers look for excrescencies in individual computers in businesses and banking systems. They can hack into your network and gain access to your particular, business, and fiscal information by exploiting any loopholes they find.
3. Grey Hat Hackers
Grey Hat Hackers fall in between white and black chapeau hackers. Grey chapeau hackers may not use their chops for particular gain, they can still have both good and bad intentions. For case, a hacker who hacks into an association and finds some vulnerability may blunder it over the internet or inform the association about it. nonetheless, as soon as hackers use their hacking chops for the particular gain they come black chapeau hackers.
Our Ethical Hacking Certification Course contains professional certification and job assistance, helping you to find high-paying career opportunities.











Sign in to leave a comment.