When we talk about ethical hacking or penetration testing, most people immediately think about flashy exploits, brute-force attacks, or phishing traps. But before any of that can happen, there’s a quieter, more analytical phase that determines the success of every cyber operation — Enumeration.
In the world of cyber security, enumeration is often considered the gateway to exploitation. It’s the process where hackers — ethical or otherwise — systematically extract detailed information from a target system. This phase can reveal usernames, device names, system resources, and even hidden vulnerabilities. Understanding how enumeration works gives professionals a powerful edge in both offense and defense.

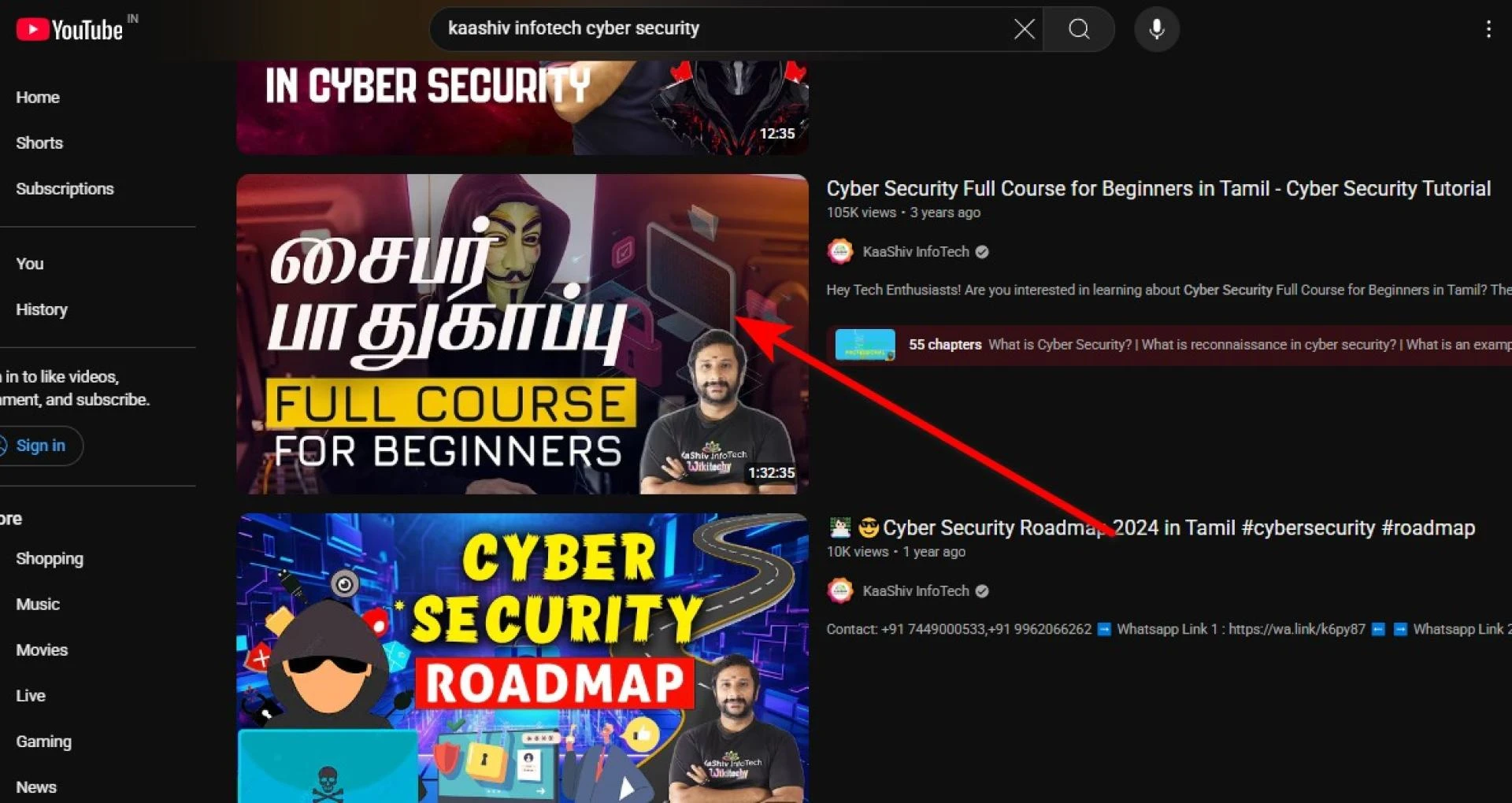
Enumeration in Cyber Security - Kaashiv Infotech Cyber Security
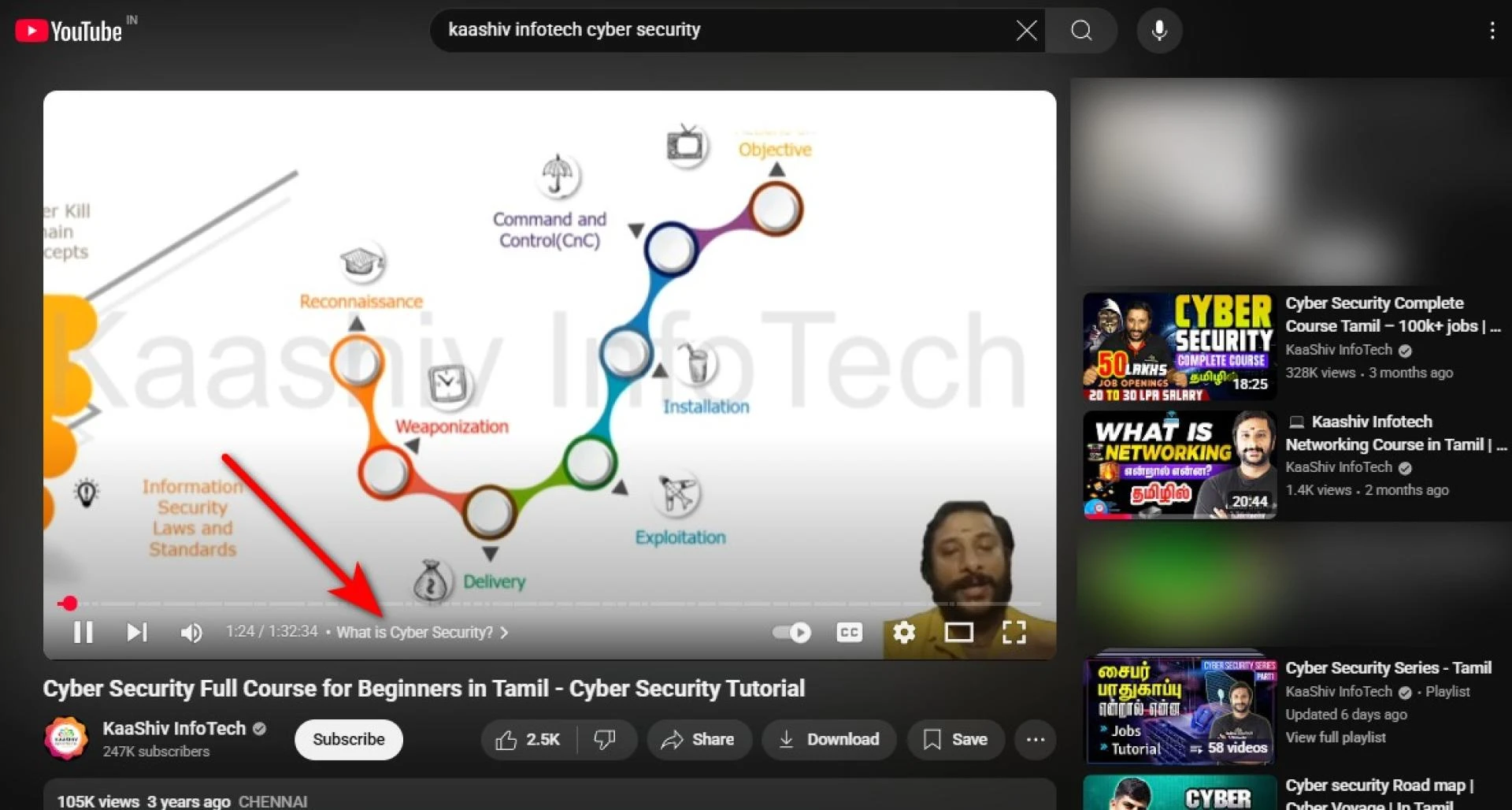
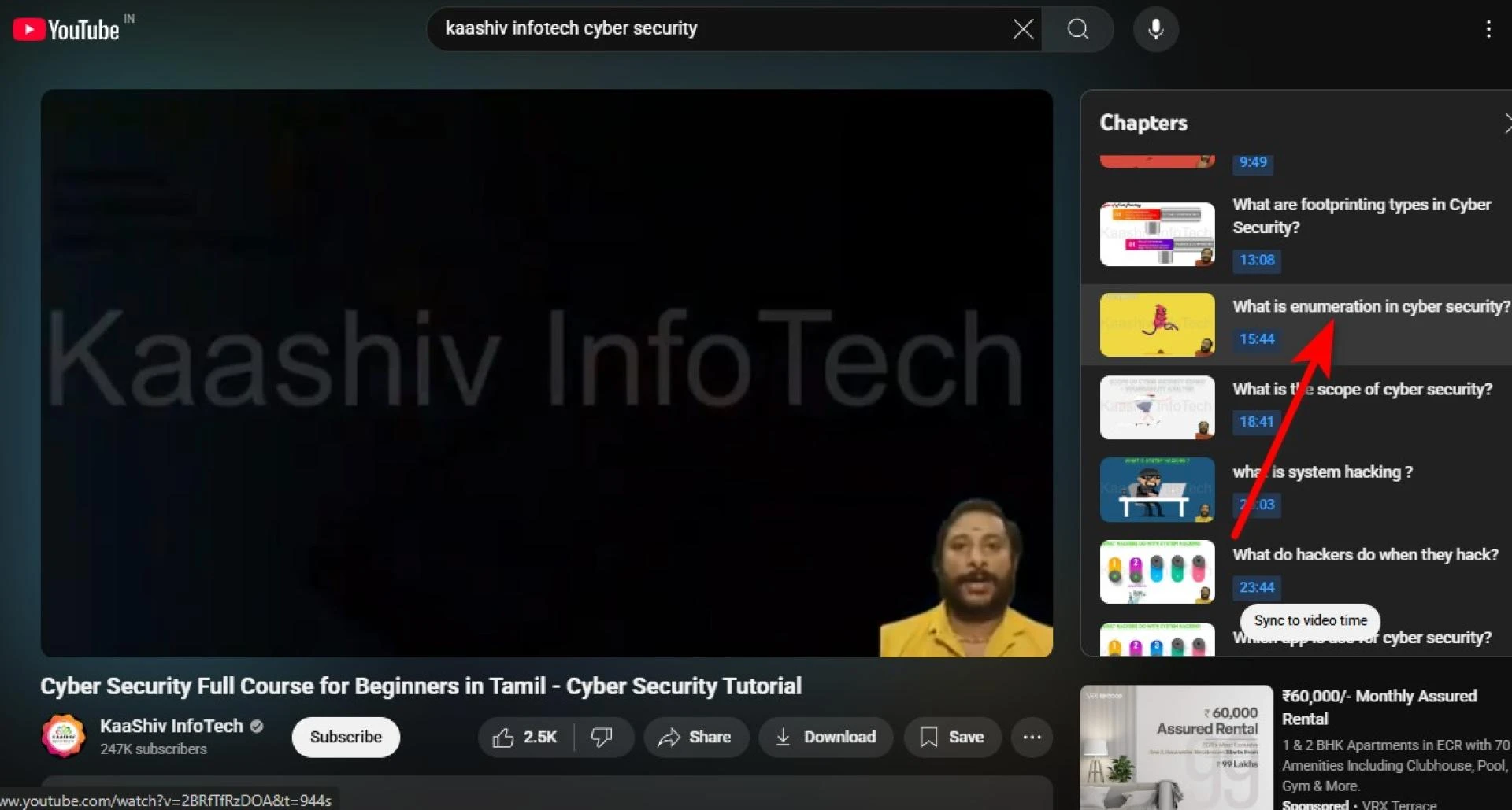
Steps For PC:
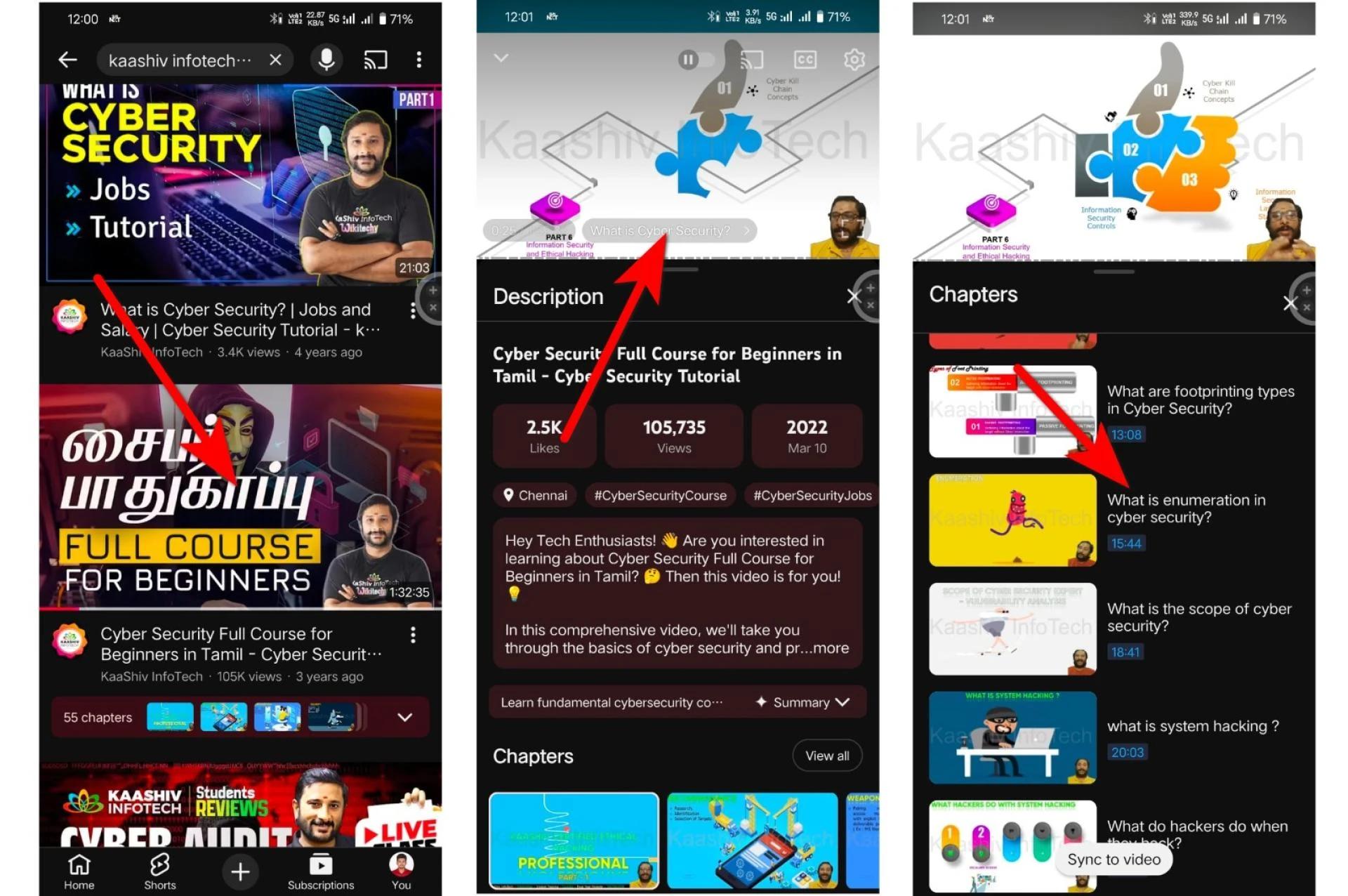
Steps For Mobile:
🔍 What Is Enumeration in Cyber Security?
Enumeration is the process of gathering more detailed and structured data from a system or network after the initial reconnaissance. While reconnaissance (or footprinting) collects publicly available information, enumeration digs deeper — often interacting directly with services and protocols to pull sensitive details.
Think of it like going from looking at a house from the outside (reconnaissance) to peeking through the windows and identifying the exact locks and alarm systems (enumeration).
The data extracted during enumeration can include:
- Usernames and group memberships
- Network resources and shared directories
- System banners and version information
- Running services and open ports
- Email addresses or contact points
- System policies and configurations
This information can be gold for ethical hackers during penetration testing — or a weapon for attackers if misused.
⚙️ The Techniques Used in Enumeration
Different network services and protocols allow enumeration in different ways. Some of the most common methods include:
1. NetBIOS Enumeration
Used to extract information from Windows systems, such as computer names, shared resources, and user lists. Tools like nbtstat or Hyena can reveal valuable data from poorly secured networks.
2. SNMP Enumeration
The Simple Network Management Protocol (SNMP) is used for monitoring and managing network devices. Misconfigured SNMP services can leak sensitive details like device configurations and routing information.
3. DNS Enumeration
By querying the Domain Name System, attackers can map out subdomains, mail servers, and internal IP addresses. Tools such as nslookup, dig, and DNSRecon are commonly used for this.
4. LDAP Enumeration
The Lightweight Directory Access Protocol is used in enterprise networks to store user credentials and permissions. Improperly secured LDAP servers can expose organizational hierarchies and login information.
5. NTP and SMTP Enumeration
These protocols can reveal time synchronization data and valid email addresses respectively — both of which are useful for social engineering or phishing attacks.
🧩 Why Enumeration Matters
Enumeration bridges the gap between passive information gathering and active exploitation. It provides the attacker (or ethical hacker) with a roadmap of the system’s internal structure. Without this step, launching a precise attack would be like throwing darts blindfolded.
From a defensive standpoint, understanding enumeration helps organizations secure their systems. Security experts and learners in Kaashiv Infotech Cyber Security Courses in Chennai practice both sides — how to perform enumeration ethically and how to detect or prevent it through monitoring tools and security configurations.
For instance, firewalls, intrusion detection systems (IDS), and log analysis can help detect enumeration attempts early, preventing a breach before it escalates.
🧠 Real-World Example of Enumeration
Imagine a hacker targets an organization’s email server. During the reconnaissance phase, they discover the mail domain (e.g., mail.company.com). In the enumeration phase, they connect to the SMTP service and issue the VRFY command — a simple way to check if certain usernames exist.
By systematically testing usernames (like admin, hr, support), the attacker builds a list of valid accounts. Later, this list can be used for password attacks or phishing campaigns.
This same technique, when used ethically, helps organizations find such weaknesses and patch them before real attackers exploit them.
🧰 Tools Commonly Used in Enumeration
Cybersecurity professionals rely on several tools for effective enumeration:
- Nmap – Identifies open ports and running services.
- Netcat – Used for banner grabbing and simple service enumeration.
- Enum4linux – Gathers SMB and Windows information.
- SNMPwalk – Extracts SNMP data from network devices.
- Nikto – Scans for web vulnerabilities and outdated software.
These tools are standard components in every ethical hacker’s toolkit and are widely covered in cybersecurity training programs.
🔒 How to Defend Against Enumeration
Defending against enumeration isn’t about blocking access completely — it’s about minimizing information leakage. Here are some preventive steps:
- Disable Unused Services: Fewer active services mean fewer attack surfaces.
- Apply Strong Authentication: Prevents anonymous access to network resources.
- Patch and Update Regularly: Fixes vulnerabilities in outdated software.
- Limit Error Messages: Generic error messages reduce information disclosure.
- Use Firewalls and IDS Tools: Detect unusual probing or enumeration attempts.
Learners pursuing Kaashiv Infotech Cyber Security Internship in Chennai get hands-on exposure to these configurations, learning to implement real-world defense strategies through simulated attack-and-defense exercises.
Additionally, students often pair this with Networking internship or Ethical Hacking internship to gain a deeper understanding of system architecture and threat modeling — two essential skills for anyone aspiring to work in penetration testing or digital forensics.
🚀 Final Thoughts
Enumeration might not be the most glamorous part of cybersecurity, but it’s one of the most crucial. It reveals how much information your system is giving away — often without you even realizing it.
For ethical hackers, enumeration is like putting together the pieces of a puzzle before making the next move. For defenders, it’s a reminder that every open port, service, or configuration could be revealing more than intended.
Building this awareness is what separates a good security analyst from a great one. With structured programs like those offered by Kaashiv Infotech Cyber Security, learners move beyond theory — they practice enumeration, mitigation, and incident response hands-on, preparing for real-world security challenges.
In the ever-evolving cyber battlefield, knowledge is your strongest firewall.
Tags:
kaashiv infotech cyber security, kaashiv infotech enumeration, kaashiv infotech ethical hacking, kaashiv infotech penetration testing, kaashiv infotech information gathering, kaashiv infotech cybersecurity training, kaashiv infotech ethical hacking course, kaashiv infotech network security, kaashiv infotech cyber defense, kaashiv infotech ethical hacker, kaashiv infotech reconnaissance, kaashiv infotech linux security, kaashiv infotech security analysis, kaashiv infotech cyber awareness, kaashiv infotech it security, kaashiv infotech write cafe, kaashiv infotech system hacking, kaashiv infotech technology training, kaashiv infotech cyber forensics, kaashiv infotech web security

















Sign in to leave a comment.