Cyber threats are no longer random or opportunistic. Modern attackers follow structured paths, carefully planning each move to gain access, maintain persistence, and achieve their objectives. Understanding how these threats evolve is the first step toward stopping them. Attacker Lifecycle Protection focuses on disrupting adversaries at every phase of their journey, rather than reacting only after damage is done.
Understanding the Attacker Lifecycle
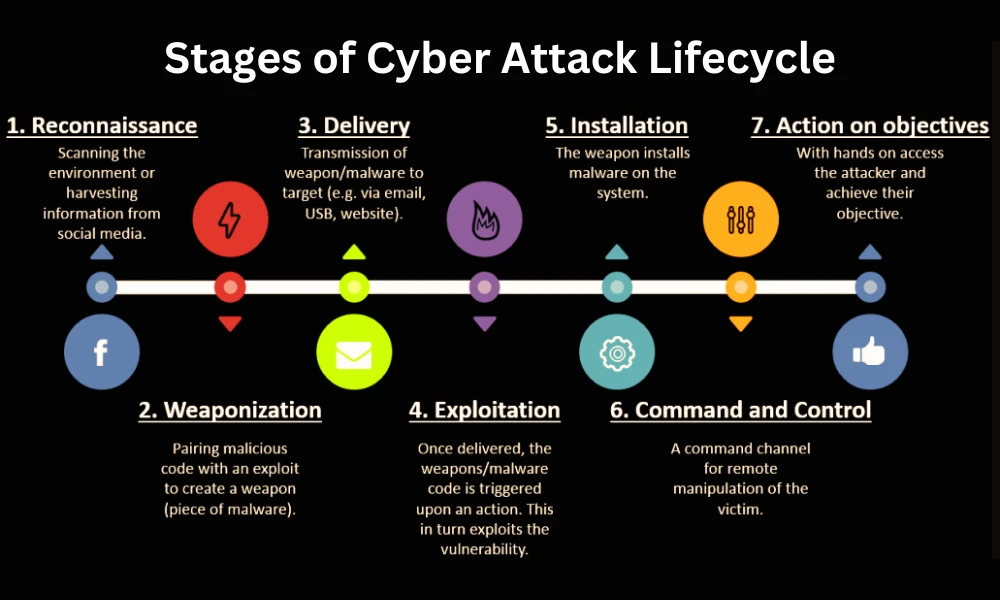
Attackers typically operate through a predictable sequence of actions. While tools and techniques may vary, the underlying lifecycle remains consistent across most cyber incidents.
Common Stages of an Attack
- Reconnaissance and information gathering
- Initial access through phishing, vulnerabilities, or stolen credentials
- Lateral movement across systems
- Privilege escalation and persistence
- Data exfiltration, disruption, or sabotage
Traditional security tools often focus on one or two stages, leaving gaps attackers can exploit.
What Is Attacker Lifecycle Protection?
Attacker Lifecycle Protection is a proactive security approach designed to identify, monitor, and disrupt threats across every phase of an attack. Instead of relying solely on perimeter defenses or post-breach detection, this strategy emphasizes continuous visibility and control.
By mapping attacker behavior and intent, organizations can detect threats earlier and reduce the time adversaries spend inside their environments.
Key Principles Behind the Approach
- Continuous monitoring of user and system behavior
- Detection of anomalies rather than known signatures
- Correlation of events across endpoints, networks, and cloud systems
- Rapid response to prevent progression to the next stage
Why Traditional Security Models Fall Short
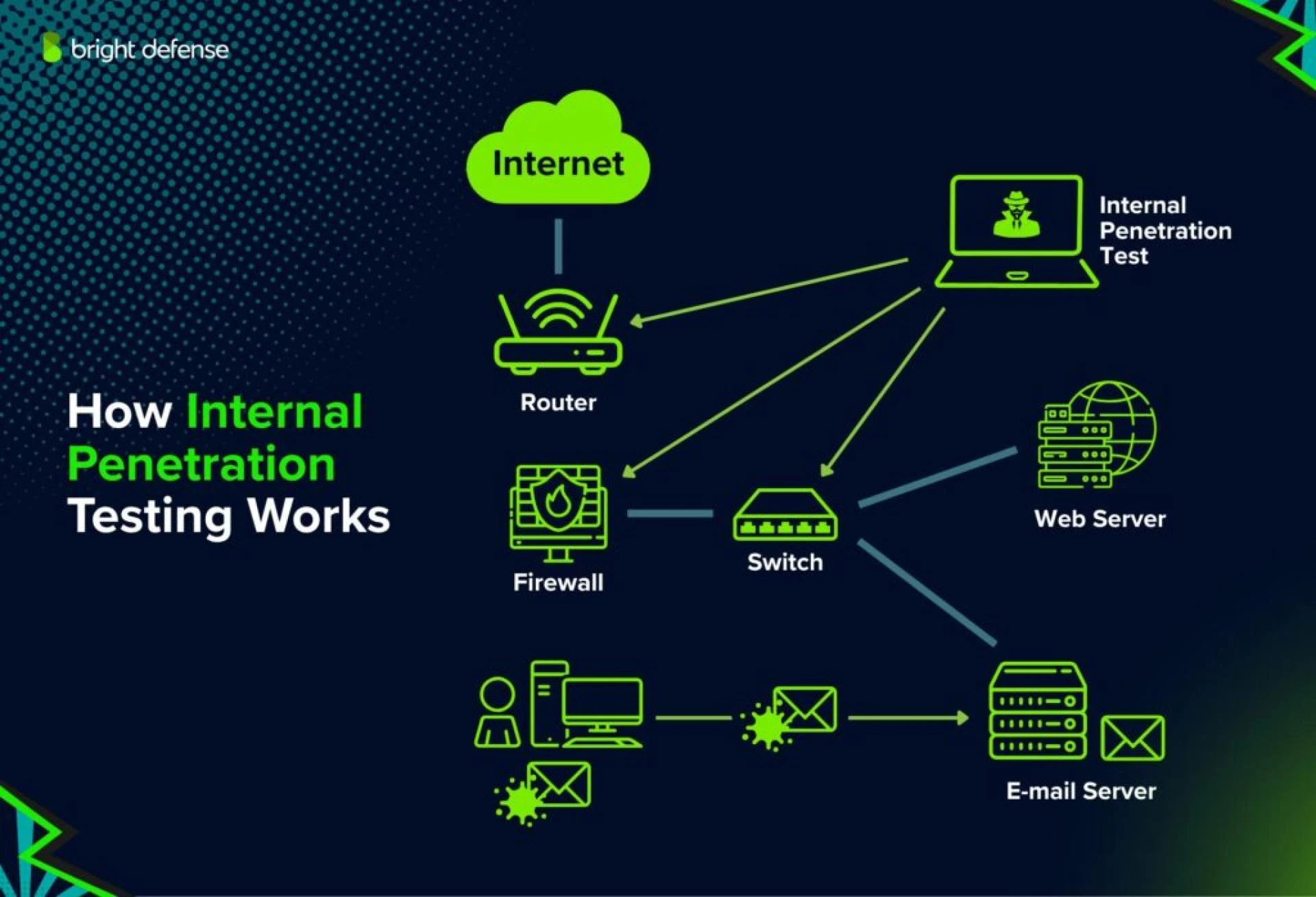
Many organizations rely on isolated security controls such as firewalls, antivirus software, or intrusion detection systems. While these tools are important, they often operate independently.
Limitations of Reactive Security
- Alerts occur after compromise
- Siloed tools lack contextual awareness
- Slow response increases attacker dwell time
Attacker Lifecycle Protection addresses these gaps by providing end-to-end threat coverage and actionable intelligence that supports faster decision-making.
How Attacker Lifecycle Protection Works in Practice
Early Detection and Disruption
The earlier a threat is detected, the less damage it can cause. Behavioral analytics and threat intelligence help identify suspicious activity during reconnaissance or initial access.
Containment and Response
Once malicious activity is identified, automated and manual response actions isolate affected systems and users before attackers can move laterally.
Continuous Improvement
Security teams refine controls and detection rules based on real-world attack patterns, strengthening defenses over time. Implementing Attacker Lifecycle Protection as an ongoing process ensures adaptability to evolving threats.
Business Benefits Beyond Security
Reduced Risk and Downtime
By interrupting attacks early, organizations minimize operational disruption and financial losses.
Improved Incident Response
Security teams gain better context, enabling faster and more effective response actions.
Stronger Compliance Posture
Many regulatory frameworks require proactive threat management. Lifecycle-based protection supports audit readiness and risk management objectives.
Adopting Attacker Lifecycle Protection also helps align security initiatives with broader business goals.
Best Practices for Getting Started
Focus on Visibility First
Understand what assets, users, and data exist in your environment before attempting to protect them.
Integrate Security Tools
Ensure endpoints, networks, and cloud platforms share intelligence and insights.
Prioritize Threat-Based Detection
Shift from alert-driven responses to behavior-driven analysis that highlights real risks.
A well-planned Attacker Lifecycle Protection strategy emphasizes coordination, automation, and continuous learning.
How LMNTRIX Active defense Helps Organizations Stay Ahead
LMNTRIX Active defense delivers advanced threat detection and response solutions built around real-world attacker behavior. Their expertise enables organizations to identify threats early, contain incidents faster, and reduce long-term risk.
By leveraging LMNTRIX Active defense, security teams gain deeper visibility across environments and actionable insights that improve defensive decision-making. Their approach focuses on stopping attacks before they reach critical impact stages.
Conclusion: Take Control of the Attacker’s Journey
Cyber attackers thrive on time, complexity, and blind spots. Breaking their momentum requires a strategy that sees the full picture. Attacker Lifecycle Protection empowers organizations to detect, disrupt, and defeat threats at every stage.
Partnering with LMNTRIX Active defense provides the tools and expertise needed to implement this approach effectively. Don’t wait for a breach to reveal weaknesses.
Contact Us today to learn how LMNTRIX Active defense can help you protect your environment, reduce risk, and stay ahead of modern attackers.
FAQs
1. Is attacker lifecycle protection suitable for small organizations?
Yes. While often associated with large enterprises, smaller organizations also benefit from lifecycle-based security by improving visibility and reducing response times.
2. How does this approach differ from traditional threat detection?
Traditional detection focuses on individual alerts, while lifecycle protection correlates behavior across multiple stages to identify real threats earlier.
3. Does implementing this strategy replace existing security tools?
No. It enhances existing tools by integrating them into a unified, behavior-driven defense strategy.
















Sign in to leave a comment.