

Cloud Security Assessment is one of the most effective ways to protect sensitive business data from modern cyber threats. As organizations move more w

Digital threats are no longer limited to large corporations. Small businesses, startups, and even personal websites are now frequent targets for cyber
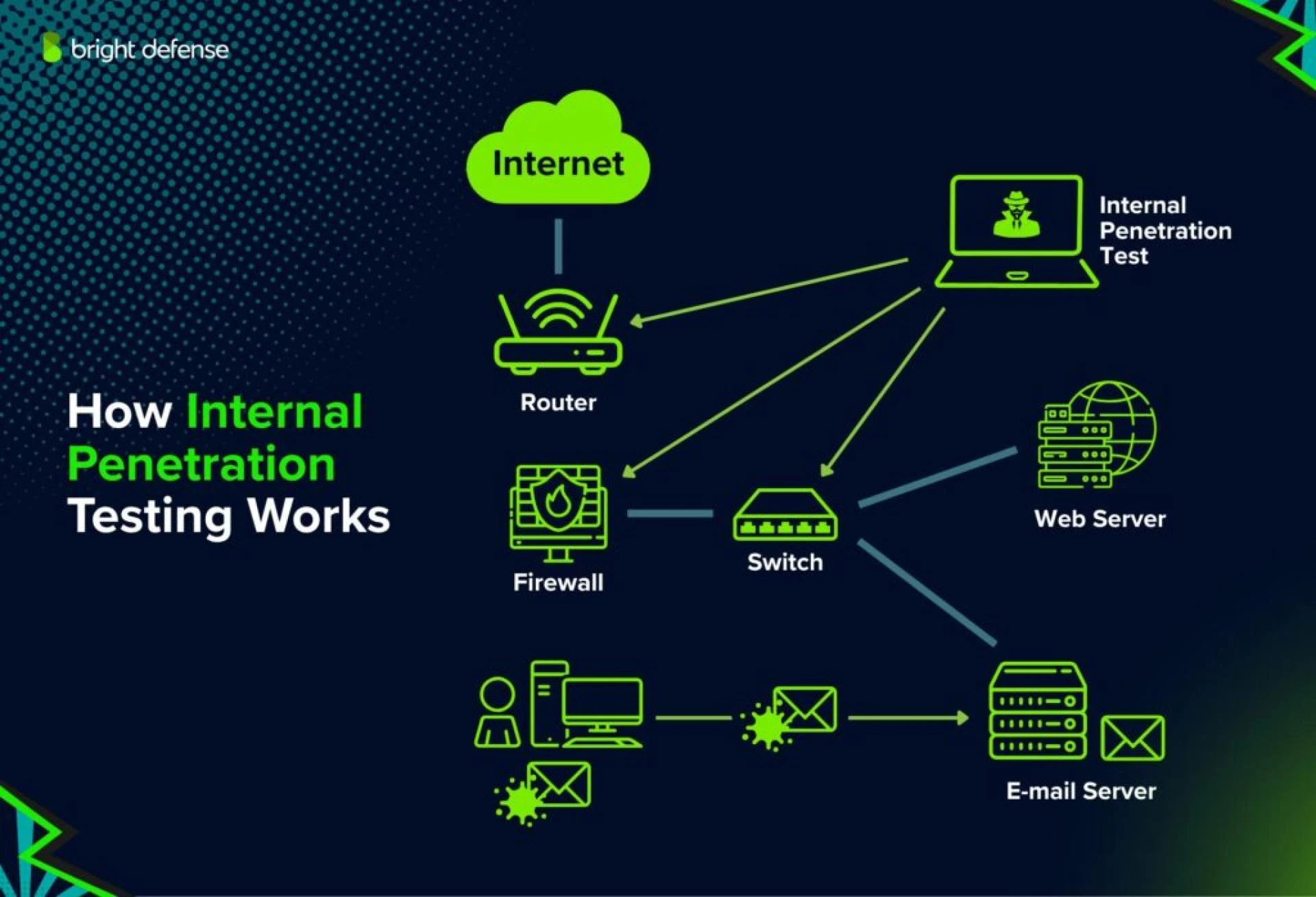
In today’s digital-first world, cyber threats are no longer limited to external hackers. Many security breaches start inside the organization, wheth

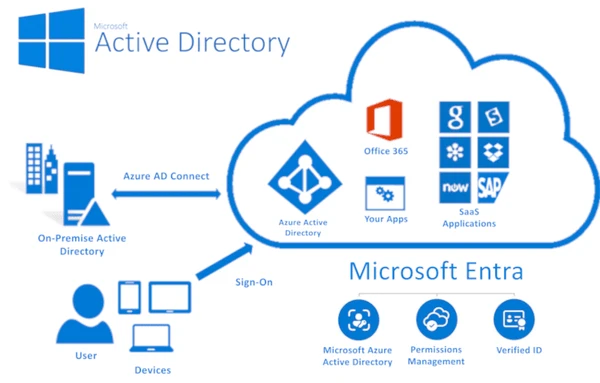
Active Directory is the backbone of identity and access management for most organisations. It controls who can log in, what systems they can access, a
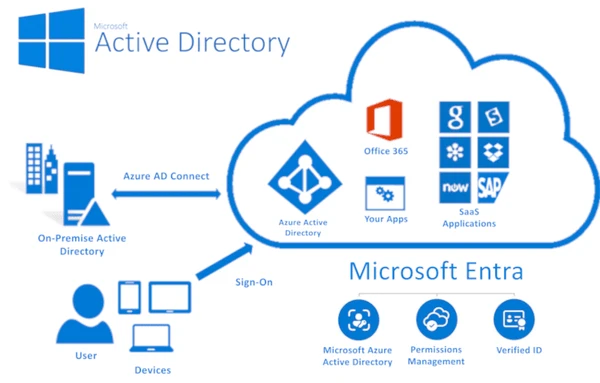
Active Directory (AD) remains the backbone of identity and access management for most organizations. As cyber threats grow more advanced in 2026, atta

Cyber threats in 2026 are more advanced, automated, and targeted than ever before. Traditional security testing is no longer enough. This is why organ
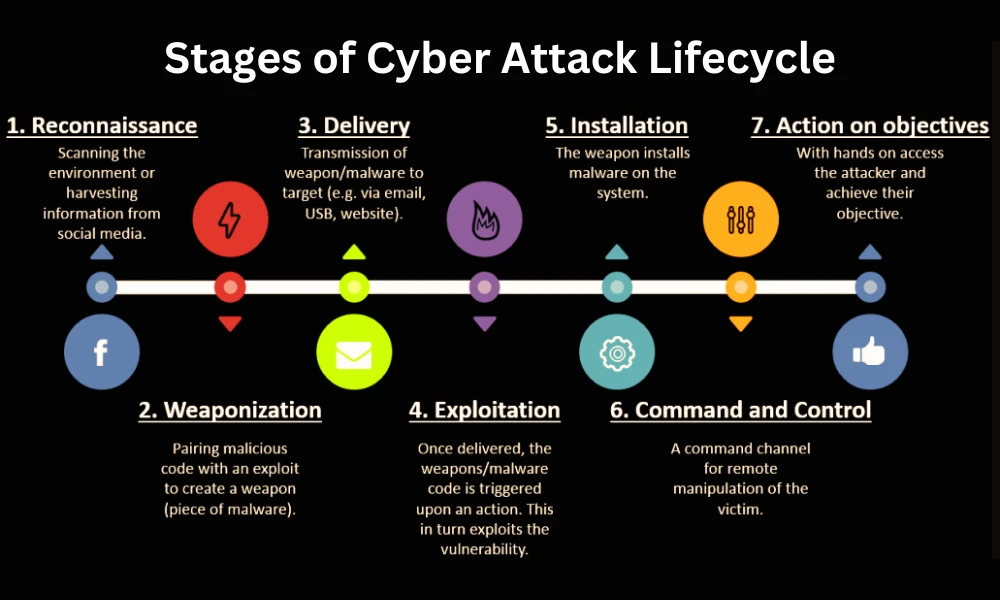
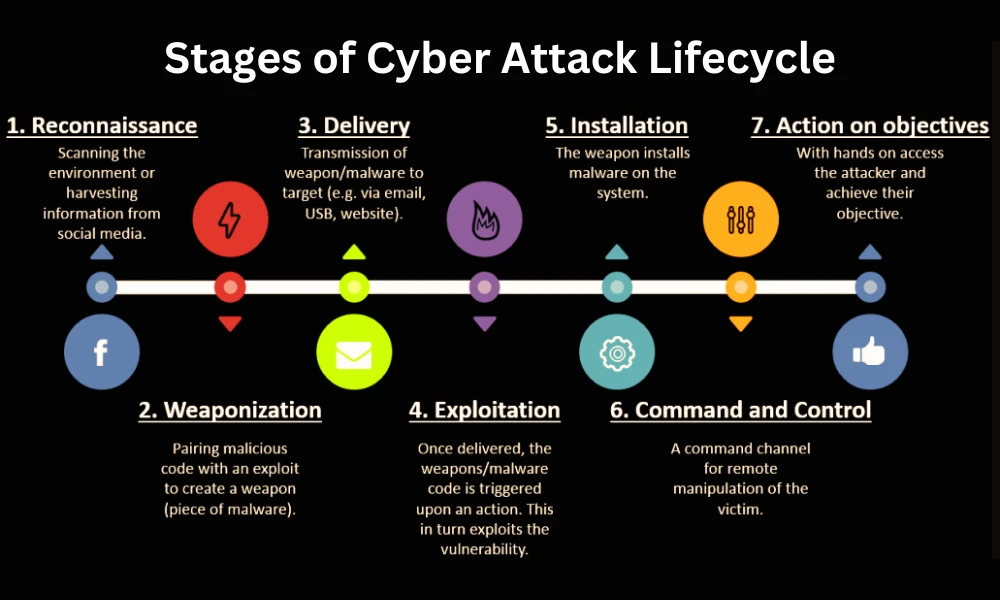
Cyber threats are no longer random or opportunistic. Modern attackers follow structured paths, carefully planning each move to gain access, maintain p
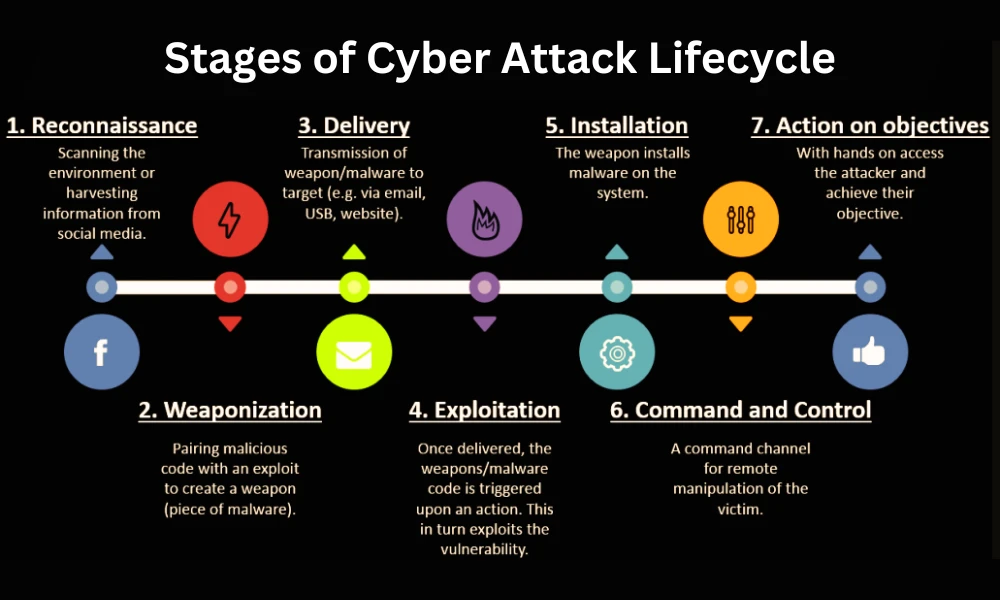
Modern cyber threats don’t appear out of nowhere. Attackers follow a predictable series of stages—from initial reconnaissance to full system compr
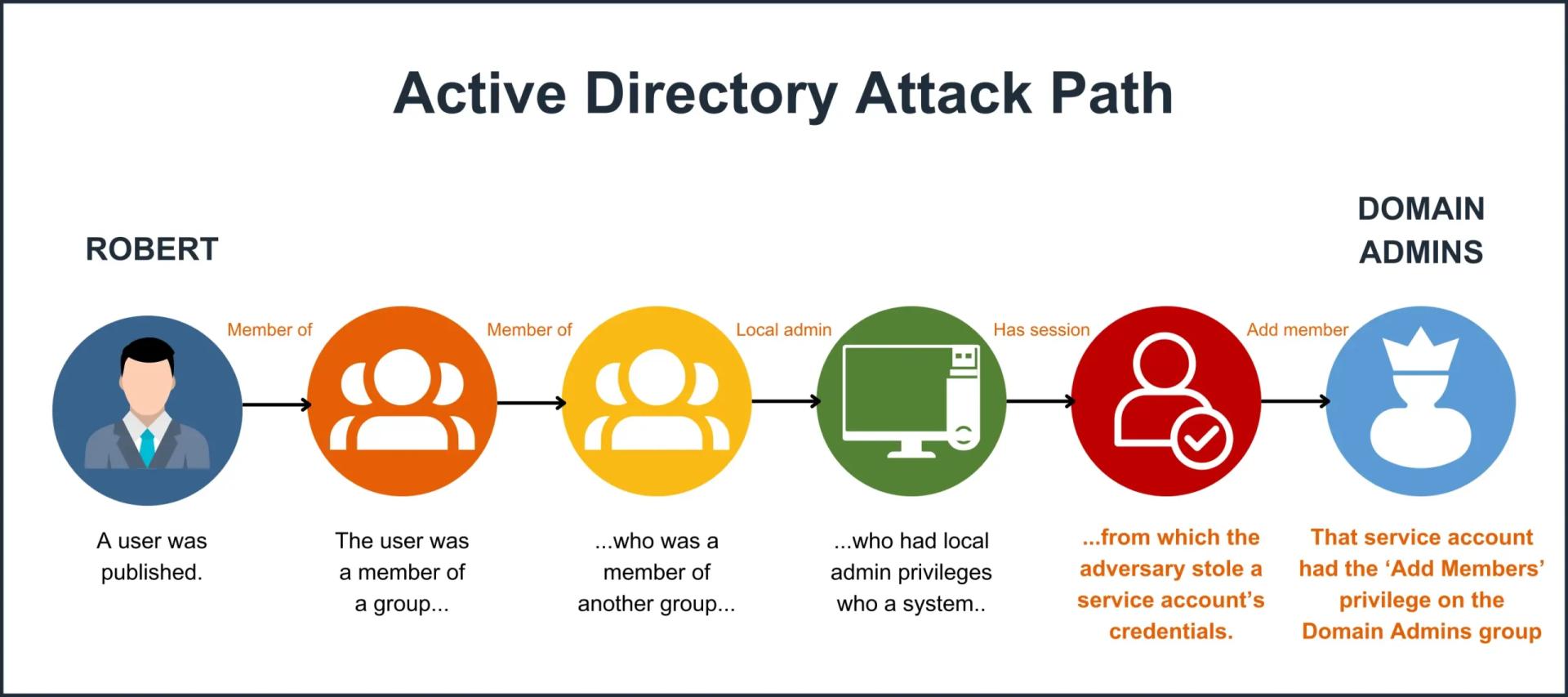
Active Directory (AD) remains the backbone of identity and access management for most organizations. Yet in an era of rising cyber threats, cloud expa

In today’s fast-paced digital world, cyber threats evolve faster than ever. As businesses adopt cloud services, remote work, and interconnected syst