Modern cyber threats don’t appear out of nowhere. Attackers follow a predictable series of stages—from initial reconnaissance to full system compromise. Understanding these stages is the key to stopping intrusions early, which is where Attacker Lifecycle Protection becomes an essential strategy for every organization seeking stronger, proactive defense.
This guide breaks down how attackers operate, why traditional security often falls short, and how a lifecycle-based defense model empowers security teams to block and disrupt attacks before damage occurs. Whether you're a business owner, IT manager, or security enthusiast, this beginner-friendly breakdown will help you understand the full picture.
Understanding the Attack Lifecycle
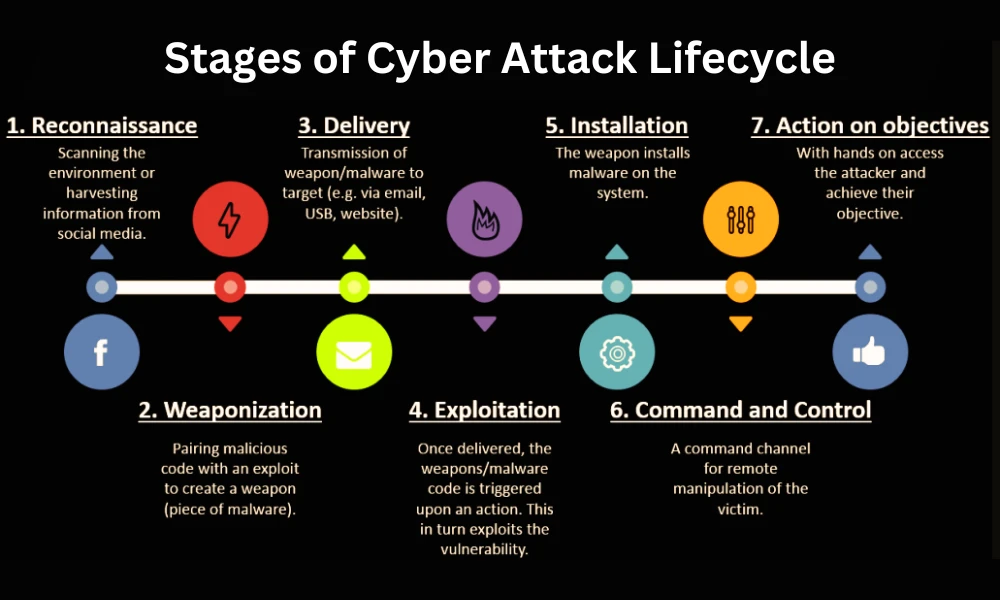
Before you can defend against attackers, you need to understand their playbook. Almost every cyberattack—no matter the technique or target-moves through a series of recognizable stages. These steps form the basis of what security teams call the attack lifecycle.
Below is a simplified breakdown.
1. Reconnaissance
In this stage, attackers gather information about their target. They look for weak points such as outdated software, exposed credentials, and misconfigured systems. The attacker’s goal is to stay hidden while identifying the easiest way in.
2. Initial Access
This occurs when attackers gain their first foothold. Methods include phishing emails, exploiting vulnerabilities, or using stolen login information.
3. Privilege Escalation
Once inside, attackers aim to elevate their access-often by compromising admin accounts or exploiting internal weaknesses.
4. Lateral Movement
Here, attackers move through your environment, searching for high-value assets such as sensitive data, financial systems, or critical infrastructure.
5. Action on Objectives
This is the final stage, where attackers execute their end goal: data theft, ransomware deployment, or system disruption.
Understanding these phases is the foundation upon which modern defense strategies-including Attacker Lifecycle Protection are built.
Why Traditional Security Tools Fall Short
Most older security technologies work reactively. They detect threats after they’ve breached your defenses or already taken action. This creates several problems:
- Security teams drown in alerts.
- Attackers spend weeks or even months inside systems unnoticed.
- Organizations don’t have full visibility into what’s happening across their environments.
Legacy solutions focus on “point-in-time” detection, but attackers operate continuously. This mismatch is why organizations are shifting toward holistic, attacker-focused defense approaches supported by leading platforms like LMNTRIX Active Defense.
The Shift Toward Holistic Defense Strategies
As attackers become more coordinated and sophisticated, security teams need a model that tracks the entire attack path-not just isolated events. This new model is designed to detect intrusions earlier, respond faster, and eliminate blind spots.
Attacker Lifecycle Protection plays a major role in this modern defense philosophy by focusing on disrupting attackers at every stage of their progression.
Solutions like LMNTRIX Active Defense embody this shift with capabilities that monitor, analyze, and intercept threats across networks, endpoints, and cloud environments in real time.
Key Components of Effective Lifecycle-Based Defense
To build a strong lifecycle-focused security posture, organizations should adopt layered, multi-vector defenses that work together. Here are the essential components.
Continuous Monitoring
Identifying unusual or suspicious activity early is critical. Continuous monitoring ensures no network behavior goes unnoticed.
Threat Hunting
Rather than waiting for alerts, proactive threat hunters search for indicators of compromise across your environment. This approach is at the core of how LMNTRIX Active Defense operates.
Behavioral Analytics
Advanced analytics detect patterns of behavior that suggest malicious activity-even if the threat is new or unknown.
Rapid Response and Containment
Stopping an attacker mid-lifecycle can prevent data theft, ransomware execution, or service outages. The faster your response, the less damage occurs.
How Attacker Lifecycle Protection Works in Practice
Here’s a simple breakdown showing how lifecycle protection disrupts attackers at every step.
Early Detection During Reconnaissance
Lifecycle-based defense tools monitor for scanning, probing, and suspicious discovery attempts. These early red flags trigger alerts long before attackers gain a foothold.
Blocking and Isolating Initial Access
Advanced endpoint and network controls prevent unauthorized entry. When access is attempted, automated responses quarantine affected devices or accounts.
Stopping Lateral Movement
By monitoring internal traffic and user behavior, lifecycle-aware systems identify when attackers try to move deeper into the network. This is a stage where Attacker Lifecycle Protection really excels.
Preventing Attack Completion
When attackers attempt to execute their end goal, defense systems use deception, isolation, and automated remediation to prevent damage.
This real-time multi-stage defense is precisely what makes LMNTRIX Active Defense such a powerful platform for modern organizations facing sophisticated threats.
Benefits of Lifecycle-Based Protection
Organizations that adopt lifecycle-focused security models gain significant advantages:
- Earlier threat detection
- Reduced dwell time
- Enhanced visibility across all systems and assets
- A more proactive security posture
- Lower risk of data loss and operational downtime
- Better alignment with modern threat landscapes
By focusing on the entire attacker journey, organizations drastically reduce the chances of a successful breach.
Is This Approach Right for All Organizations?
Nearly every organization-large, small, or mid-size-can benefit from lifecycle-based defense. Cyberattacks are no longer limited to large enterprises; small and midsize businesses are increasingly targeted due to weaker defenses.
Lifecycle protection is a scalable model, and platforms like LMNTRIX Active Defense make advanced security accessible to organizations at any maturity level.
Conclusion: Strengthen Your Security with a Lifecycle Approach
Today’s attackers are fast, coordinated, and persistent. Relying on outdated methods leaves organizations vulnerable at multiple stages of the attack chain. Implementing Attacker Lifecycle Protection is one of the most effective ways to stop adversaries before they cause damage.
If you want a proven, modern, and proactive solution that protects every phase of the attack lifecycle, LMNTRIX Active Defense delivers exactly that.
Ready to enhance your security posture, reduce risk, and outsmart attackers at every step? Contact LMNTRIX Active Defense today to take the first step toward continuous, real-time protection.
FAQs
1. Is lifecycle-based protection the same as the cyber kill chain?
They are related concepts, but not identical. The cyber kill chain is a traditional model describing attacker steps. Lifecycle protection builds on this model by applying real-time defenses at each stage.
2. Can small businesses benefit from lifecycle protection?
Absolutely. Small businesses are increasingly targeted because attackers assume they have weaker defenses. A lifecycle approach provides visibility and security that fits organizations of all sizes.
3. Does this model replace antivirus software?
Not directly. Antivirus is one layer of protection, but lifecycle-based defense focuses on detecting and disrupting attackers across multiple stages—far beyond what antivirus alone can provide.





Sign in to leave a comment.