Active Directory (AD) remains the backbone of identity and access management for most organizations. Yet in an era of rising cyber threats, cloud expansion, hybrid identity models, and increasingly sophisticated attack techniques, AD environments have become one of the most heavily targeted components in enterprise networks.
As we move into 2026, cyber adversaries are leveraging automation, generative AI-enabled attacks, and identity-based exploitation techniques to break into organizations—not by brute force, but by abusing misconfigurations, privilege escalation paths, and insecure identity controls.
This is why an Active Directory Risk Assessment is no longer optional. It’s a business necessity.
What Is an Active Directory Risk Assessment?
An Active Directory Risk Assessment is a structured evaluation of your AD environment to identify:
- Security gaps
- Misconfigurations
- Excessive privileges
- Vulnerable trust relationships
- Weak authentication practices
- Indicators of compromise
- Exposure points for identity-based attacks
The goal is to understand your current security posture, uncover hidden risks, and create a roadmap for improving AD security.
Why AD Risk Assessments Are Critical in 2026
1. Attackers Are Exploiting Identity More Than Ever
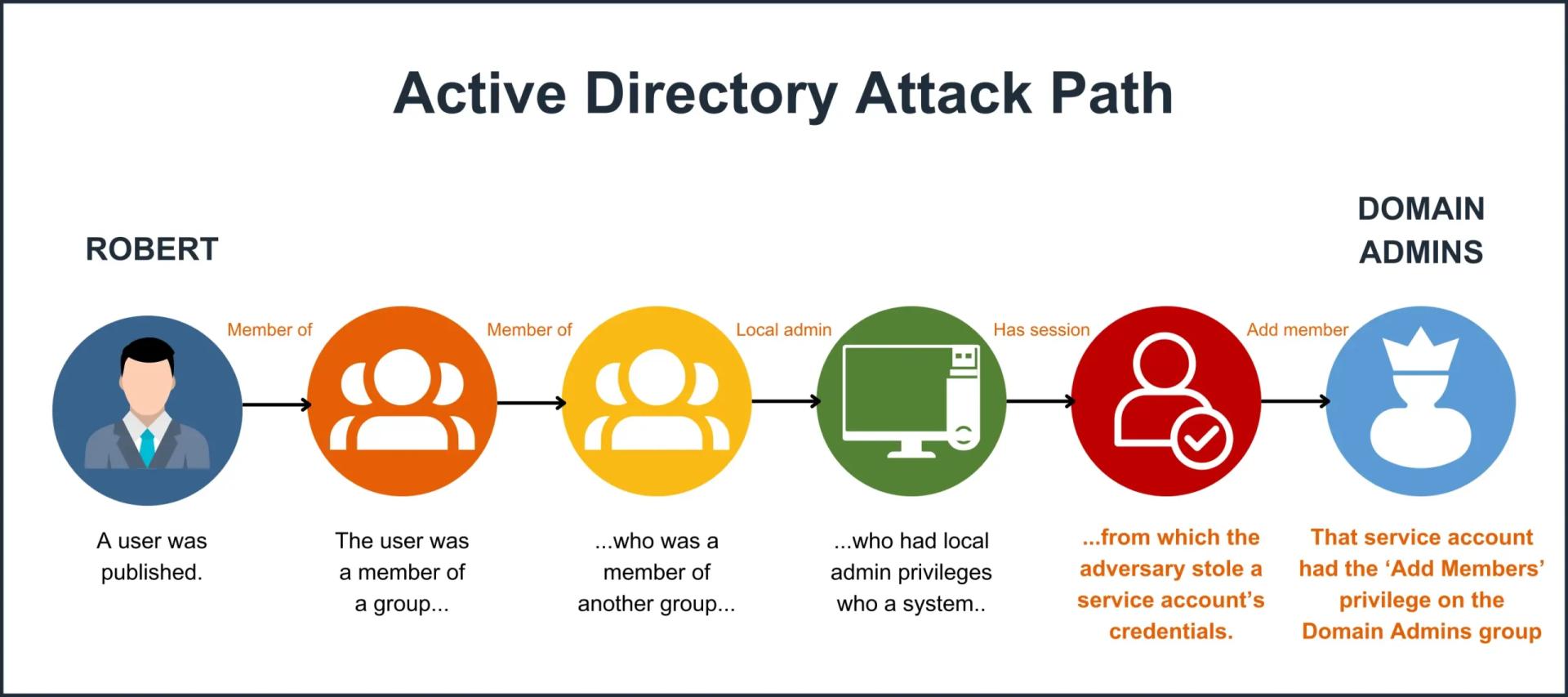
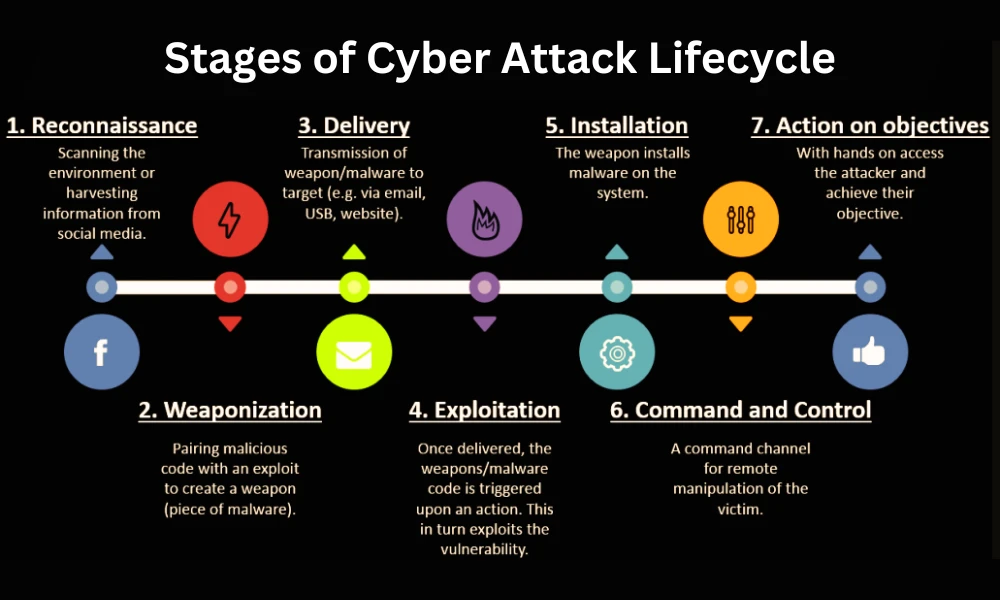
Ransomware and APT groups have shifted to identity-driven attacks, using techniques such as:
- Kerberoasting
- Pass-the-Hash
- Golden & Silver Ticket attacks
- Credential dumping
- Lateral movement via weak permissions
These attacks don’t need malware—just access to an unprotected identity system. An Active Directory Risk Assessment helps organizations identify exactly where these exploits are possible.
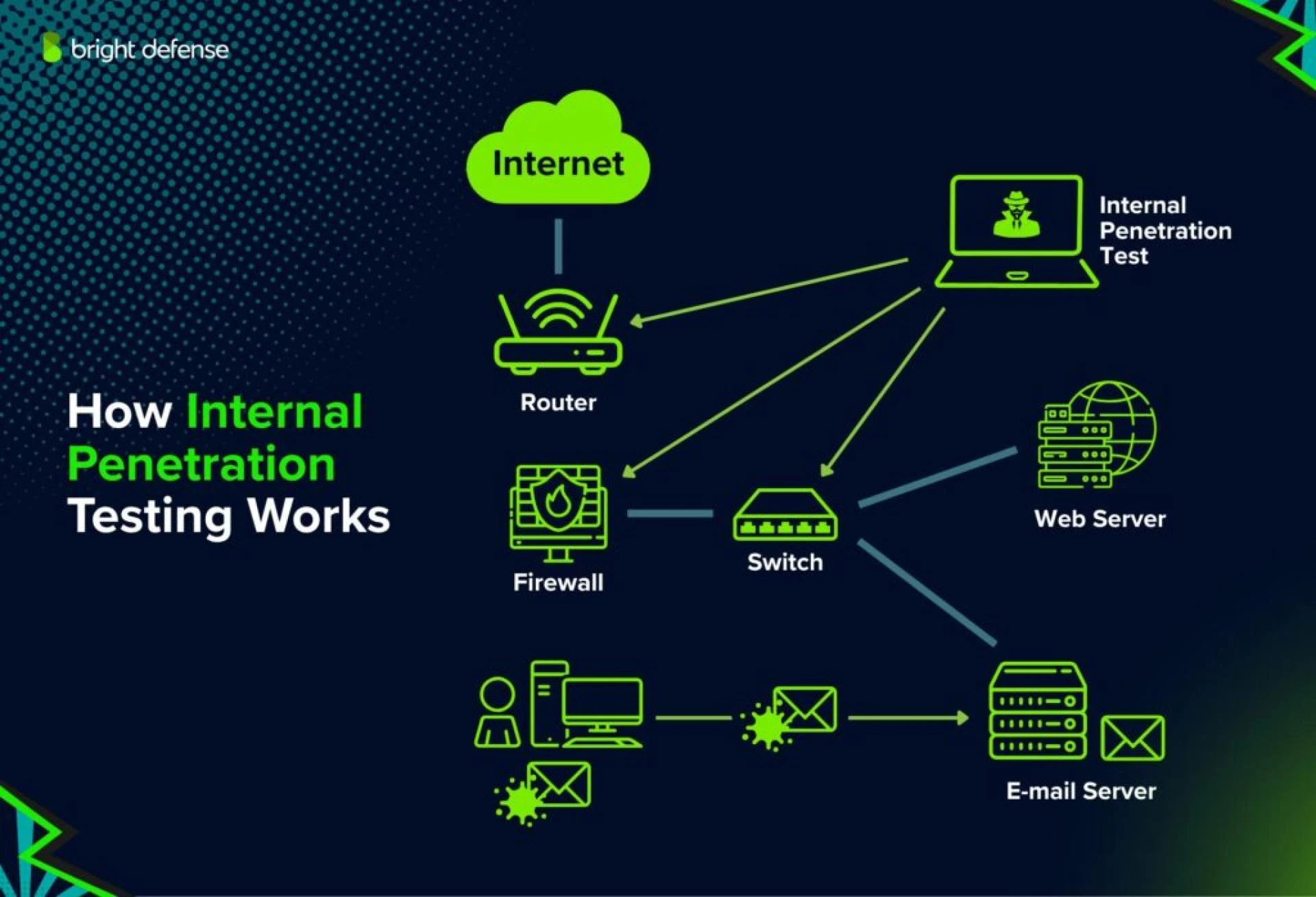
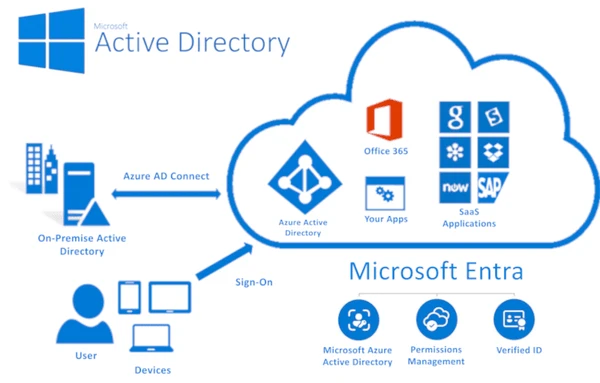
2. Hybrid Environments Increase Complexity
In 2026, most organizations operate a mix of:
- On-prem AD
- Azure AD / Entra ID
- Third-party identity providers
This creates complexity, and complexity creates risk. Misconfigurations between cloud and on-prem directories can create identity backdoors that attackers love to exploit.
A comprehensive assessment ensures these environments are aligned, hardened, and monitored.
3. Privilege Creep Is at an All-Time High
Employees change roles, but their privileges often don’t. Over time, organizations accumulate:
- Stale admin accounts
- Dormant privileged accounts
- Unused service accounts
- Excessive group memberships
This “privilege creep” becomes a goldmine for attackers. An AD risk review highlights where privileged access should be removed or reduced.
4. Compliance Pressures Are Increasing
In 2026, frameworks such as NIST 800-53, ISO 27001, SOC 2, and new government regulations emphasize identity security as a core requirement.
An AD risk assessment supports compliance by:
- Documenting misconfigurations
- Showing remediation plans
- Providing audit-ready visibility
- Reducing identity-related nonconformities
5. Legacy Configurations Still Haunt Modern AD
Even organizations with modern cloud infrastructure often retain:
- Legacy protocols
- Outdated domain controllers
- Weak NTLM settings
- Poor password policies
These legacy elements become attack vectors. An assessment reveals what should be updated, replaced, or decommissioned.
6. Zero Trust Requires Strong AD Foundations
Zero Trust is now mainstream, but it fails without a secure identity layer. If AD is misconfigured, attackers can bypass Zero Trust controls entirely.
An AD Risk Assessment ensures Zero Trust rests on a hardened, trustworthy identity system.
Key Components of an Effective AD Risk Assessment
Privilege and Access Review
This includes:
- Admin group evaluations
- Lateral movement path mapping
- Privilege escalation analysis
Authentication and Policy Assessment
Evaluating:
- Password policy strength
- MFA coverage
- Kerberos misconfigurations
- NTLM exposure
Security Configuration Review
Checking for:
- Unsecured domain controllers
- Legacy configurations
- Open attack surfaces
Threat Detection and Logging
Ensuring visibility into:
- Suspicious authentication activities
- Privileged account use
- Potential compromise indicators
Benefits of Performing an AD Risk Assessment in 2026
- Reduced breach risk by eliminating identity attack paths
- Improved privilege hygiene through cleanup and restructuring
- Enhanced readiness for ransomware and insider threat attacks
- Faster compliance audits and fewer identity-related findings
- Stronger Zero Trust alignment and better identity governance
In short, organizations strengthen their security posture where attackers aim most: identity.
Conclusion: Strengthen Your Identity Security Before Attackers Exploit It
As cyber threats accelerate in 2026, securing Active Directory is one of the smartest investments an organization can make. An Active Directory Risk Assessment gives you a clear, actionable path to closing identity-based vulnerabilities before adversaries exploit them.
If you’re ready to secure your environment with advanced identity defense, Lmntrix Active Defense offers world-class assessments, detection, and response capabilities built for modern hybrid environments.
Protect your organization today with Lmntrix Active Defense.
Frequently Asked Questions
1. How often should an organization perform an Active Directory Risk Assessment?
Most organizations should conduct a risk assessment annually, and anytime major identity or infrastructure changes occur. High-risk industries may benefit from quarterly reviews.
2. Does an AD Risk Assessment disrupt operations?
No. A well-designed assessment is non-intrusive and uses read-only access. Daily operations remain unaffected.
3. Is an AD Risk Assessment necessary for companies using both on-prem AD and Azure AD/Entra ID?
Absolutely. Hybrid identity environments introduce additional complexity, and an assessment ensures both systems are secure and aligned.
















Sign in to leave a comment.