Social engineering techniques come in a variety of shapes and sizes. The techniques that are commonly used are listed below.
The Familiarity Exploit: Users are less suspicious of people they know. Prior to launching a social engineering attack, an attacker can become acquainted with the users of the target system. The attacker may interact with users during meals, when they are smoking, at social events, and so on. This familiarises the attacker with the users. Assume the user works in a building that requires an access code or card to gain entry; the attacker may follow the users as they enter such locations. Because they are familiar with them, the users are more likely to hold the door open for the attacker to enter. The attacker may also ask you where you met your spouse, the name of your high school math teacher, and other personal information. Because they trust the familiar face, users are more likely to reveal answers. If a user forgets their password, this information could be used to hack email accounts and other accounts that ask similar questions.
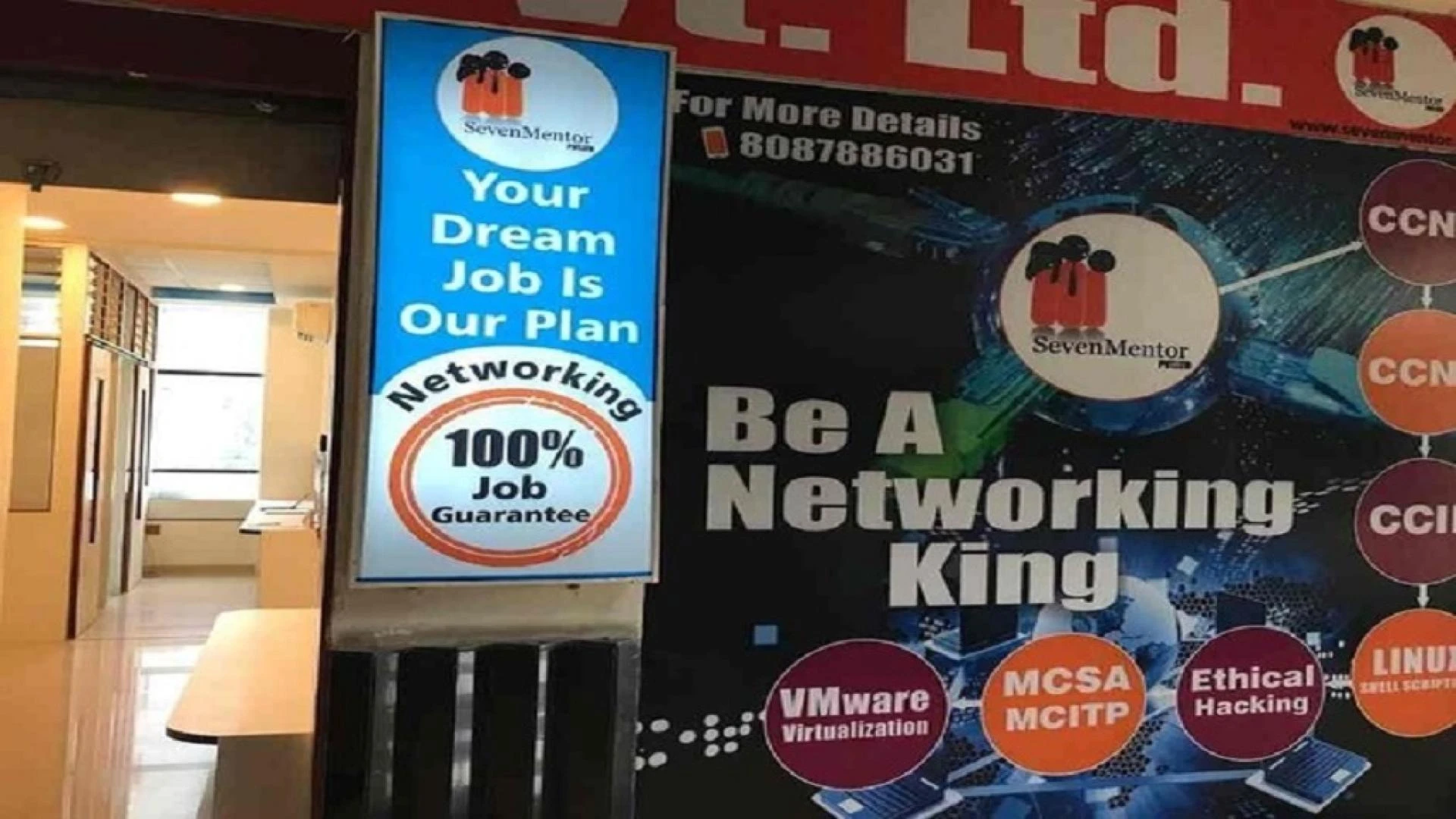
Upskilling and current in the workplace require Ethical Hacking Course.
Intimidating Situations: People avoid people who intimidate those around them. Using this technique, the attacker may pretend to have a heated conversation on the phone or with a scheme accomplice. The attacker may then request information from users, which will be used to compromise the security of the users' system. Users will almost certainly give correct answers in order to avoid a confrontation with the attacker. This method can also be used to avoid being questioned at a security checkpoint.
0


Sign in to leave a comment.