Finding a vulnerability is only part of the story. The real challenge begins when you try to turn that weakness into something actionable. This is where exploitation comes in, and why it remains one of the most technical and respected skills in cybersecurity.
For professionals looking to build this depth, platforms like Cyberwarfare Labs provide hands-on environments to practice real scenarios. Programs such as Certified-Exploit-Development-Professional are designed to guide learners through structured labs that reflect what is expected from the best cyber exploitation course and help them progress toward the best certification cyber security paths.
What Makes Exploitation Different
Exploitation is not about running tools and collecting results. It requires understanding how software behaves under unexpected conditions.
When an application crashes, an experienced professional does not stop there. They ask:
• Why did it crash?
• What part of memory was affected?
• Can this behavior be controlled?
• Is it possible to redirect execution?
This mindset separates basic testing from advanced offensive work.
Thinking Like an Exploit Developer
Exploitation is as much about thinking as it is about technical skill. It involves breaking down how a system works and identifying where control can be gained.
Instead of looking at applications as black boxes, professionals begin to see:
• How input flows through the program
• Where memory is allocated and used
• How the system handles unexpected data
• What protections are in place
This perspective is often developed through training aligned with the best cyber exploitation course, where learners spend time analyzing behavior rather than just identifying issues.
Where the Real Learning Happens
Exploitation cannot be mastered through theory alone. It requires trial, error, and close observation.
In practical environments, learners typically work with vulnerable binaries where they:
• Trigger crashes intentionally
• Analyze memory using debuggers
• Modify inputs to control execution
• Gradually build working exploits
Programs designed for the best certification in cyber security emphasize this iterative learning process, where understanding comes from doing.
Key Skills You Build Along the Way
Understanding Memory Behavior
At the core of many exploits is how memory is managed. Learning how stack and heap structures work helps professionals understand where things can go wrong.
Debugging and Analysis
Debugging tools allow you to step through execution and observe how a program behaves. This is where most insights come from during exploitation.
Crafting Reliable Exploits
Creating an exploit is rarely a one-time success. It involves refining payloads until they behave consistently under different conditions.
Bypassing Modern Protections
Modern systems include protections that make exploitation harder. Learning how to work around these defenses is a key step toward advanced skill levels.
A Practical Approach to Skill Building
Hands-on labs are where everything comes together. Instead of just reading about vulnerabilities, learners actively work through them.
Typical practice involves:
• Analyzing how and why a program fails
• Using debugging tools to trace execution
• Controlling program flow through crafted inputs
• Achieving stable code execution
This approach is what defines a best cyber exploitation course, where the focus is on building real capability rather than theoretical understanding.
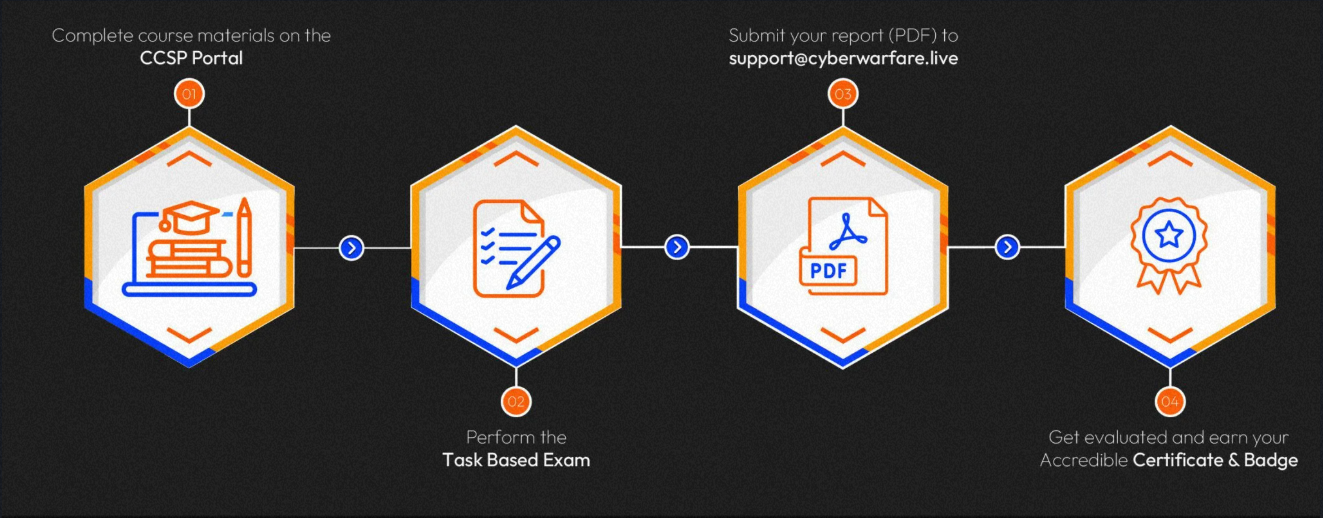
Certification Procedure
Who this is for
• Professionals who want to move beyond basic penetration testing
• Individuals interested in vulnerability research
• Security enthusiasts exploring low-level system behavior
• Learners aiming for advanced offensive roles
• Those preparing for the best certification cyber security
Why These Skills Matter
Exploitation skills are not just about attacking systems. They help professionals understand the real impact of vulnerabilities.
Organizations value individuals who can demonstrate how a flaw can be used in practice, not just identified. This level of understanding is critical in advanced security roles, including red teaming and vulnerability research.
As systems become more complex, the ability to think at a lower level and analyze behavior deeply is becoming increasingly important.
Final Thoughts
Exploitation is a skill that develops over time through consistent practice and curiosity. It requires patience, attention to detail, and a willingness to experiment.
By working through structured labs and real scenarios, professionals can build a strong foundation in understanding how software behaves under attack. Training aligned with the best cyber exploitation course and the best certification cyber security helps bridge the gap between knowing about vulnerabilities and actually exploiting them.






Sign in to leave a comment.