Have you ever thought about how companies manage millions, if not thousands, of security events each day? The answer usually boils down to one thing: the management of logs within SIEM systems.
It may sound complicated initially. However, once you understand it, the process is actually quite easy. It's an essential aspect for every company, particularly in rapidly growing regions such as the UAE.
What is Log Management in SIEM?
In its essence, log administration is the act of acquiring, storing, analyzing, and monitoring log data generated by devices, systems, and applications.
Each time something occurs within your IT environment, such as an attempt to access a file, a login attempt, or an error in the system, it generates an entry in your log.
A SIEM system will take all of the logs and then do the following:
- They are brought together in one location
- They make sense.
- It alerts you if anything appears suspicious
Imagine it as an office for security where every action is recorded and closely monitored.
Businesses that invest in SIEM solutions in Dubai rely heavily on this technology to remain secure and in compliance.
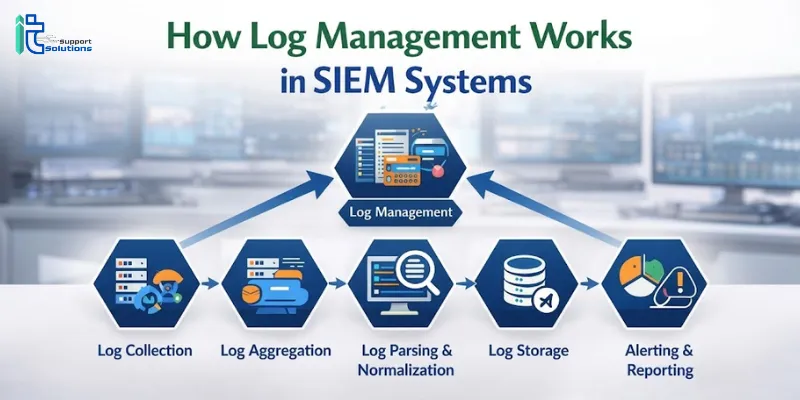
How Log Management Works in SIEM Systems
Let's break it into steps step-by-step.
Log Collection
Everything begins with the collection of data.
SIEM systems collect logs from multiple sources like:
- Servers
- Firewalls
- Network devices
- Applications
- Cloud platforms
A reliable SIEM solution provider in the UAE makes sure that all vital systems are connected properly, ensuring that there is no data that is important to miss.
Log Normalization
This is where things start to get interesting.
SIEM is a standardization tool that converts all the data into a standard format. This is known as normalization.
What is the significance of it:
- Data analysis is easier because it's more streamlined.
- Eliminates confusion
- It allows for more rapid detection of patterns
Without normalization, reading logs will be like reading several languages simultaneously.
Log Storage
After logs have been collected after normalization, they have to be securely stored.
SIEM systems:
- Logs to store for long periods (sometimes years)
- Ensure data integrity
- It is important to have quick access when you need it.
This is crucial to ensure compliance. A lot of laws in the UAE make it mandatory for businesses to keep records to be audited.
Companies that have an SIEM solution partner in UAE frequently modify storage policies according to the needs of their industry.
Log Analysis and Correlation
This is at the core of SIEM.
It seeks patterns and links events across various systems. This is known as correlation.
For instance:
- An unsuccessful login attempt
- This is followed by an successful login from an alternative location
- This is followed by massive downloads of data
SIEM detects the types of patterns and then flags these for potential dangers.
Real-Time Alerts
When suspicious activity is identified, SIEM generates alerts.
These alerts could include:
- Security teams
- Trigger automated responses
- Incorporated with incident management tools
Businesses that utilize SIEM solutions UAE depend on this feature to react swiftly and reduce the damage.
Reporting and Compliance
Then, SIEM systems generate reports.
These reports are helpful to:
- Security audits
- Checks for compliance
- Internal reviews
Companies that use SIEM solutions in Dubai often emphasize reports as being among the largest time savings.
Real-Life Example: Why Log Management Matters
Let's suppose a mid-sized firm in Dubai is hit by an incident involving data.
Without SIEM:
- The researchers don't know what time the breach occurred.
- They aren't able to identify the source.
- Recovery can take longer
With SIEM:
- Logs reveal exactly the date and time that suspicious activity began.
- The root of the breach can be identified immediately.
- The response is quicker and more efficient
This is the difference that log management can make.
Key Benefits of Log Management in SIEM
Here's a quick overview of the reason it's so beneficial:
- More visibility: Observe everything going on in your systems
- Improved threat detection speed, identify the threats before they grow
- Increased compliance to meet regulatory requirements.
- Effective investigations: Track incidents step-by step
- Workload reduction: Automate monitoring and reporting
A trusted SIEM solution provider in UAE makes sure you are getting the most of these advantages.
Choosing the Right SIEM Solution Partner
When deciding on an SIEM solution partner in UAE be sure to consider the following:
- Experience with local laws
- The ability to design solutions
- Monitoring and support on a regular basis.
- Integration capabilities
A trusted partner doesn't simply install the system; they also assist you in using it in a way that is efficient.
FAQs
1. What kind of logs does the SIEM system record?
SIEM systems record records from firewalls, servers, applications, cloud platforms, and even user activities. Basically, anything that causes an electronic event could be recorded.
2. How long will logs be stored within SIEM systems?
It's based on business needs and the compliance requirements. A lot of companies store logs for months, or even years.
3. Is SIEM just for large businesses?
Not at all. Even medium and small-sized companies are able to benefit, particularly in light of growing cybersecurity threats.
4. Can SIEM prevent cyberattacks?
It isn't able to prevent attacks by itself. However, it detects threats in advance and allows for quick response and reduces the impact.
5. Do I require an SIEM solution provider in the UAE?
Yes, using local providers can help ensure compliance, a proper installation, and support that is tailored to your specific region.
Conclusion
Log management is the foundation of any efficient SIEM system. It's what transforms raw data into useful insights that help businesses recognize threats, be compliant, and react faster if there's a problem. Without it, businesses are operating in the dark, reacting too late and frequently ignoring critical warning signals.
For businesses located in the UAE and especially those operating under strict regulations, investing in a SIEM solution in UAE is an intelligent and innovative move. When you choose the best SIEM solution partner in UAE, log management is more than a mere technical procedure. It's an advantage to be strategic too. In today's world of digital this advantage could make a huge difference.
















Sign in to leave a comment.