Due to the internet's, mobile devices', and cloud technologies' explosive expansion, both individuals and organizations are continuously at risk from emerging risks. Application security is an important but frequently disregarded aspect of cybersecurity. We'll go over the definition of application security, its importance, and its place in the larger cybersecurity framework.
What is Application Security?
The methods and procedures used to defend software programs from online attacks are referred to as application security. These risks can include illegal access, data breaches, and malicious attacks that try to take advantage of software flaws. Frequently, intrusion detection systems, firewalls, and antivirus software come to mind when we think of security. Despite their importance, these only address a portion of the problem.
Why Application Security Matters
It is evident that application security is essential given the dynamic nature of cyberthreats. Let's examine the main justifications for why protecting digital assets is so important for any business or person.
1. Protecting Sensitive Data
Applications frequently manage huge amounts of sensitive data, such as login passwords, financial records, personal information, and intellectual property. Attackers can steal or alter this data if they have access to these programs. Identity theft, financial fraud, and even a decline in user or customer trust may result from this. A sensitive data breach can have serious financial and legal consequences as well as irreversible damage to a company's brand.
2. Preventing Unauthorized Access
Unauthorized access to networks, systems, or accounts is the foundation of many cyberattacks. An attacker may be able to increase their privileges and get access to other areas of a network, such as internal systems or private databases, if they are successful in breaching an application. By guaranteeing that only authorized users may communicate with the system, proper application security may help in preventing this type of illegal access.
3. Compliance and Legal Requirements
Strict rules in several industries mandate that businesses put specific security measures in place to safeguard data. For instance, the Health Insurance Portability and Accountability Act (HIPAA) in the United States and the General Data Protection Regulation (GDPR) in Europe provide specific guidelines for how businesses must safeguard patient information. Serious fines and legal consequences may result from breaking these rules.
4. Business Continuity
Business activities may be disrupted by a successful cyberattack that breaches an application. A malware infection, data breach, or denial-of-service (DoS) assault can all have a major effect on business continuity. Reputational harm and lost revenue can arise from downtime, data loss, and recovery efforts. Businesses can remain operating by lowering the likelihood of such disruptions through application security.
5. Increasing Customer Trust
Customers are becoming more aware of their security and privacy in a world where data breaches are becoming more frequent. Businesses that take precautions to safeguard their apps give their clients the impression that their data is secure and that security is a top priority. This can provide a competitive advantage in the market and increase consumer loyalty.
Key Elements of Application Security
Let's review the basic elements of a solid application security strategy in more detail now that we know why application security is so important.
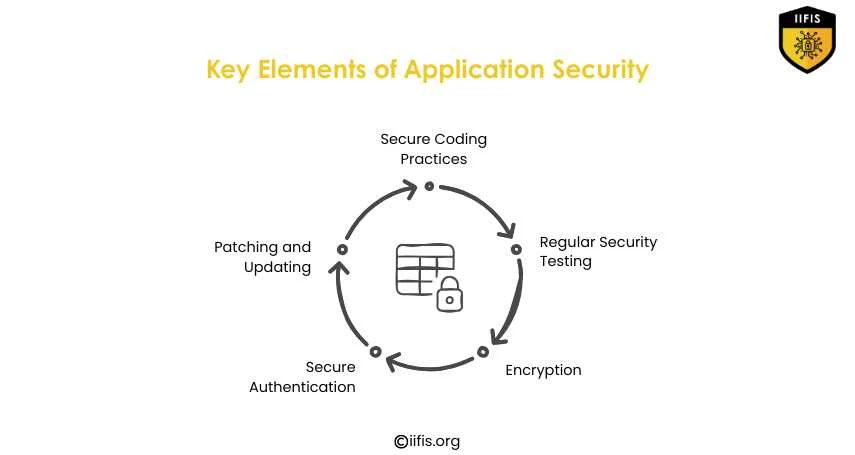
1. Secure Coding Practices
Any secure application's construction is its cornerstone. When creating software, developers should adhere to secure coding techniques to prevent creating vulnerabilities. This covers input validation, appropriate error management, and steering clear of typical coding errors that pose security threats. Early vulnerability detection is possible for enterprises by including security into the development process.
2. Regular Security Testing
At various phases of the application development process, security testing should be carried out as a continuous procedure. Finding vulnerabilities in code and operating programs can be helped by tools such as dynamic application security testing (DAST) and static application security testing (SAST). Finding vulnerabilities before attackers do can also be accomplished by regular penetration testing, in which ethical hackers try to compromise the system.
3. Encryption
One of the most important precautions for safeguarding private information is encryption. Organizations can prevent hackers from reading or using data they intercept by encrypting it. This holds true for data that is stored in databases or files as well as data that is in transit. Strong encryption mechanisms should be used by applications to safeguard sensitive data, including user information.
4. Secure Authentication and Authorization
Multi-factor authentication (MFA) and other robust authentication techniques may help in preventing unwanted access to apps. Furthermore, users should only be able to access the resources they require thanks to appropriate authorization procedures. For example, unless authorized, an employee shouldn't be able to view client data.
5. Patching and Updating
If programs' vulnerabilities are not patched or updated on a regular basis, attackers can frequently take advantage of them. To address identified vulnerabilities as soon as feasible, developers should monitor them and deliver updates. The window of opportunity for attackers is reduced when programs are updated on a regular basis.
Best Practices for Securing Applications
Businesses and developers can stick to a number of recommended practices to guarantee the security of their applications:
1. Implement Secure Software Development Lifecycle (SDLC)
Every stage of software development, from planning to testing and deployment, incorporates security through the SDLC process. This method guarantees that security is a fundamental component of the development process rather than an afterthought.
2. Use Security Frameworks and Standards
To guarantee the security of their apps, developers can utilize a variety of security frameworks and standards. The Open Web Application Security Project (OWASP), for example, lists the ten most prevalent web application vulnerabilities and offers advice on how to fix them. Organizations may stay up to date on the latest security best practices by following these guidelines.
3. Incorporate Security in DevOps (DevSecOps)
Security is now a fundamental part of the DevOps approach, which stresses cooperation between development and IT operations teams; this is called DevSecOps. This method incorporates security into every stage of the development process, from deployment to design.
The Role of IIFIS Certification in Application Security
Getting an IIFIS Application Security Certification can be a beneficial first step for people and companies looking to improve their cybersecurity capabilities. The International Institute of Information Security (IIFIS) provides certificates that enable people to acquire the know-how required to evaluate, oversee, and protect applications in a digital environment that is becoming more and more complicated. Security experts can better defend their apps against changing cyberthreats by obtaining the appropriate certifications.
In the linked world of today, application security is no longer an optional issue; it is a must. Organizations may avoid data breaches, safeguard sensitive data, and guarantee business continuity by proactively securing their apps. Ignoring application security can have serious repercussions, including monetary losses, harm to one's reputation, and legal issues.



















Sign in to leave a comment.