Organizations have networks, cloud systems, and databases where they store and process large amounts of digital information. Cybersecurity ensures that this information does not fall into the wrong hands or result in data theft or system failure. Data science assists cybersecurity teams in data analysis, threat detection, and security monitoring. Many professionals study these analytical methods through a Data Science Course in Hyderabad, which explains how data science techniques support cybersecurity systems.
Role of Data Science in Cybersecurity Monitoring
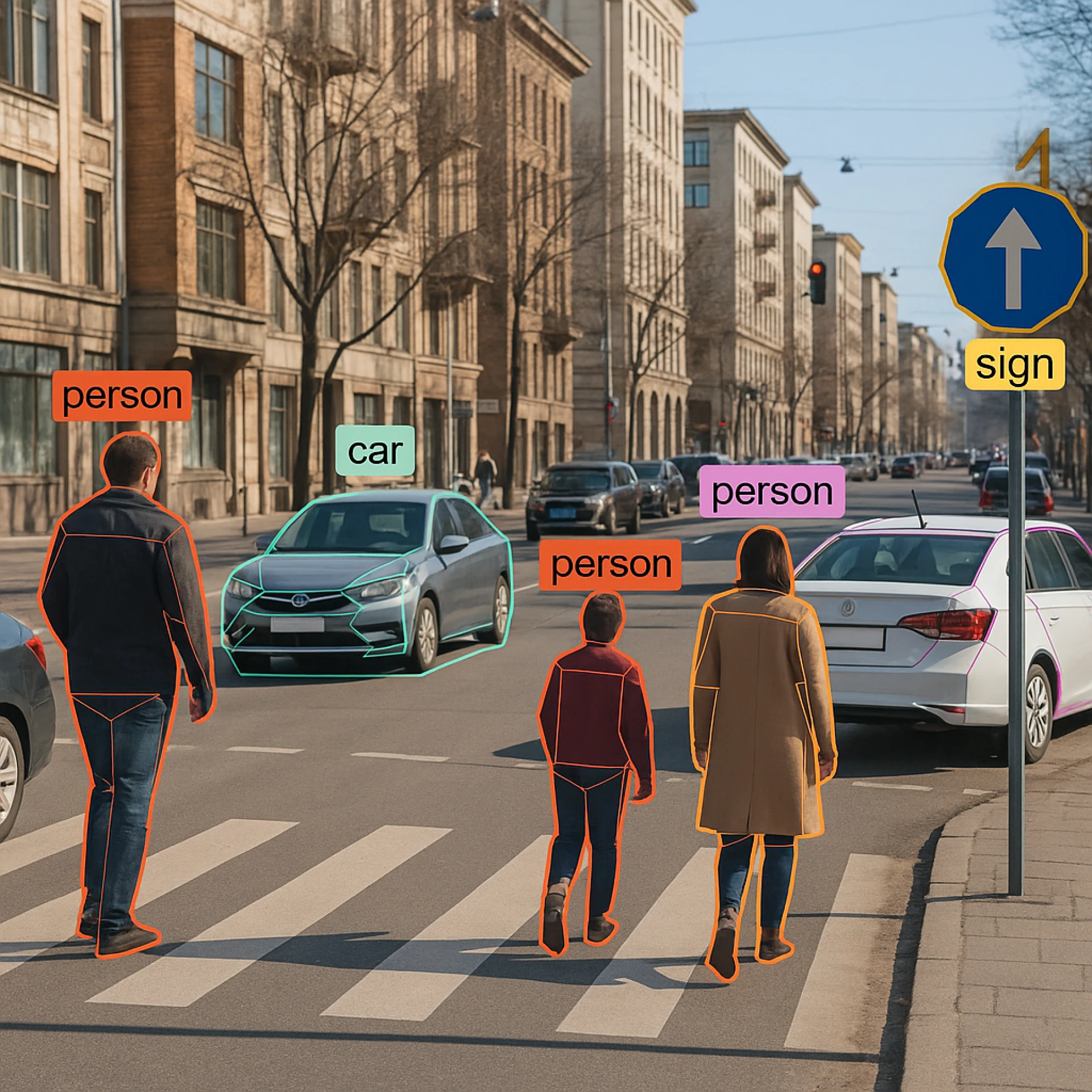
Cybersecurity teams manage large datasets that contain network traffic records, system activity logs, and user access information. Data science methods help analysts organize this information. Analysts identify patterns that indicate suspicious behaviour within digital systems.
Network monitoring tools collect detailed records of data transfers across servers and devices. These records show connection sources, data volume, login frequency, and access duration. Analysts study these patterns and detect abnormal activity that may signal security threats.
Security monitoring systems also track user behaviour across applications and databases. Analysts examine login times, device usage, and access locations. Any changes in these patterns may indicate possible unauthorized access.
Another important task in cybersecurity operations is log analysis. Events and program activities are recorded in system logs. Analysts examine these records to identify irregular activities such as failed login attempts or unusual system commands.
Cybersecurity teams also examine traffic flow across corporate networks. Data science tools organize traffic records and identify unusual data transfer patterns. Large or sudden data movements may indicate possible data exfiltration.
Data science training in Hyderabad empowers IT staff and cybersecurity professionals by enhancing their analytical skills. These programs help them develop monitoring systems that support security operations, fostering a sense of competence and readiness.
Security teams also maintain monitoring dashboards that display network activity indicators. These dashboards show login trends, alert notifications, and system health metrics. Analysts review this information regularly to identify emerging risks and security issues.
Threat Detection Using Data Science Models
Explain how early threat detection models help prevent breaches by identifying malicious activity, reinforcing their significance in cybersecurity.
Machine learning algorithms identify network activities based on historical security records. Analysts train these models using examples of malicious activity and normal system behaviour. New system activity is analyzed using these models to identify events that require investigation.
Email security systems also use data science to identify threats. Security software analyzes sender behaviour, message structure, and attachment characteristics. These systems identify spam messages, phishing attempts, and harmful attachments that may compromise system security.
Malware detection tools also use data science analysis. These systems evaluate how software programs interact with files, memory resources, and network connections. Analysts identify malicious programs when these behaviors differ from normal software activity.
Intrusion detection systems are also supported by data science. These systems analyze network traffic patterns and detect suspicious communication between devices. Analysts examine unusual connection attempts or unexpected traffic flows.
Security analysts also study domain activity and access patterns. Data science tools analyze internet traffic and identify links to dangerous or suspicious websites. This analysis helps prevent malware downloads and protects organizational networks.
Many cybersecurity professionals develop these analytical skills through Data Science Training in Hyderabad, which explains machine learning techniques used in cybersecurity applications. Training programs also explain how analysts test detection models and improve accuracy.
Threat detection systems improve cybersecurity response speed. Automated analysis identifies threats faster than manual monitoring methods. Rapid detection allows security teams to contain incidents before they affect larger systems.
Data Privacy and Protection in Data Science Systems
Financial records, health data, and personal information are sensitive data handled by data science systems. Cybersecurity measures protect this information when it is stored, analyzed, and transmitted. Data protection in data science environments is strictly enforced within organizations.
Access control systems restrict user access to specific datasets. Security teams allocate permissions based on the roles and responsibilities of employees. These controls limit unnecessary access to sensitive information.
Encryption provides another important protection method. Encryption converts readable information into coded formats that unauthorized users cannot interpret. Organizations apply encryption to stored data and network communications.
Data science infrastructure is also secured through protected storage systems. Analytical datasets are stored in secure databases and protected servers. Security teams monitor these systems and enforce strict authentication measures.
Cybersecurity teams also monitor user activity within data platforms. Analysts examine system logs that record dataset access and system modifications. These records help identify suspicious activity and prevent data misuse.
Data governance policies guide the use of data science systems. These policies define rules for dataset storage, sharing, and analysis. Structured governance reduces the risk of data exposure.
Educational programs, such as a Data Science Course in Hyderabad, explain how analysts manage data security within analytical projects. These programs also explain regulatory frameworks that guide responsible data usage.
Regular security audits and strict data security policies help organizations build trust and confidence in their data protection measures. These practices reassure cybersecurity teams that their efforts are effective in safeguarding sensitive information.
Cybersecurity Risk Analysis with Data Science
Cybersecurity risk analysis evaluates potential attacks on digital systems and data infrastructure. Data science supports this analysis through statistical methods and predictive modeling. Analysts study historical security and system vulnerabilities to estimate future risks.
Security teams collect information about software vulnerabilities, attack patterns, and network weaknesses. Data science tools organize these datasets and highlight areas that require security improvements. This analysis helps organizations strengthen system protection.
Risk models examine several system factors such as software updates, access privileges, and network configurations. Analysts evaluate these variables and estimate the probability of cyber incidents. This information supports security planning and infrastructure modernization.
Cybersecurity teams also monitor global threat intelligence reports. Analysts examine trends of cyberattacks across industries and regions. These insights help organizations prepare for emerging security threats.
Data analysis is also an important part of cybersecurity investigations conducted by incident response teams. Analysts review system logs, access history, and network traffic reports. Detailed analysis helps determine the origin and method of cyberattacks.
Security teams also use predictive models to identify potential security threats. These models evaluate system vulnerabilities and estimate possible attack scenarios. Early risk identification allows organizations to implement preventive security measures.
Many professionals develop cybersecurity risk assessment skills through Data Science Training in Hyderabad. Training sessions explain statistical analysis methods and data modeling techniques used in cybersecurity planning.
Organizations also prepare detailed security reports based on analytical findings. These reports include threat trends, vulnerability rates, and system performance indicators. Management teams use these reports to guide long-term cybersecurity strategies.
Conclusion
Cybersecurity plays a critical role in securing digital structures and confidential data. Data science provides cybersecurity with the help of surveillance systems, threat detection models, data protection policies, and risk assessment. These analytical tools assist companies in detecting threats, controlling vulnerabilities, and managing cyber resources. These analytical skills are acquired by many professionals during a Data Science Course in Hyderabad, and this is how data science can enhance the cybersecurity system and present-day digital security activities.
















Sign in to leave a comment.