When it comes to national security, public safety, and uninterrupted critical services, cybersecurity isn’t just important—it’s vital. Government agencies and critical infrastructure operators are top-tier targets for cyberwarfare, nation-state actors, and ransomware groups. Yet many still rely on legacy defenses and static audits.
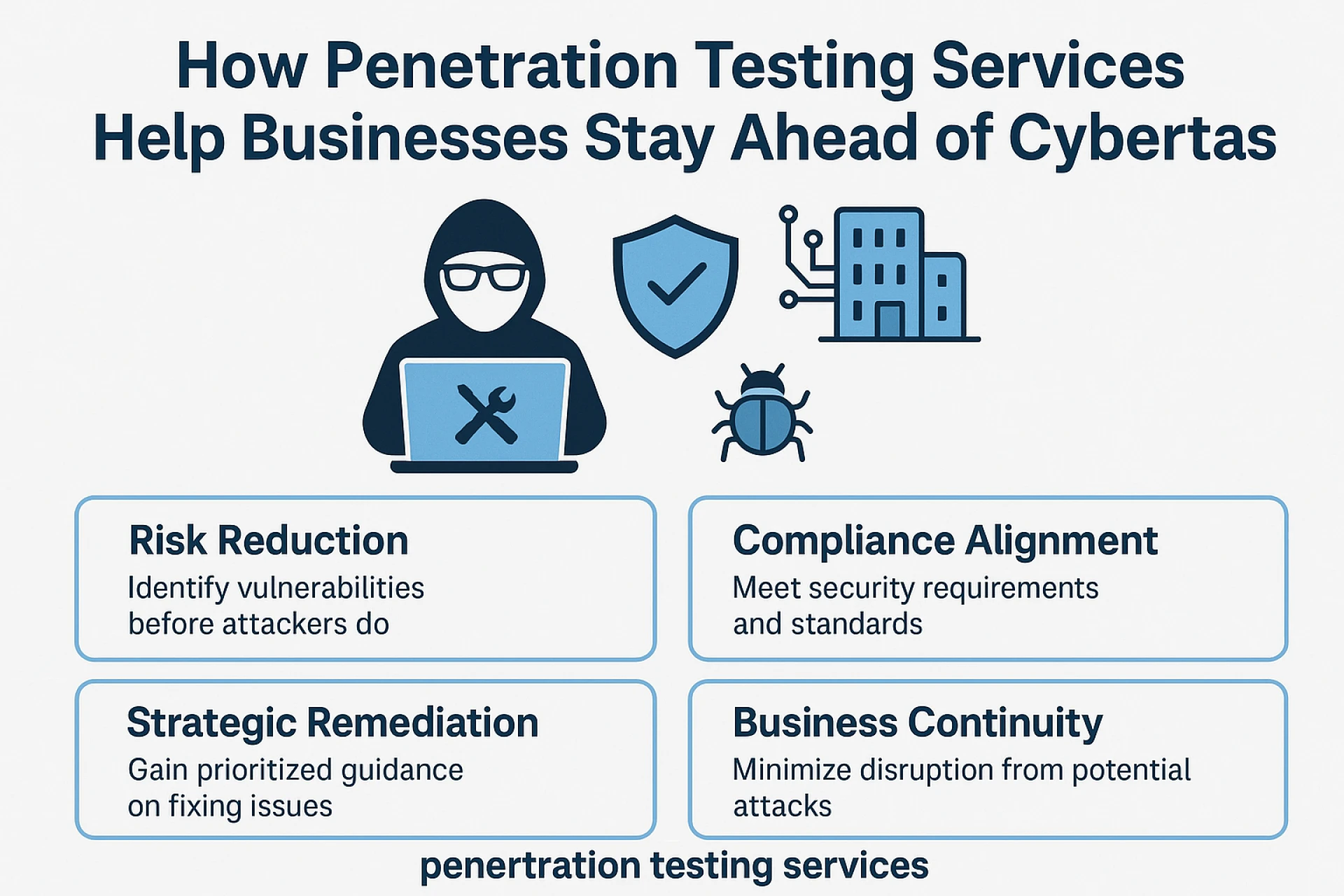
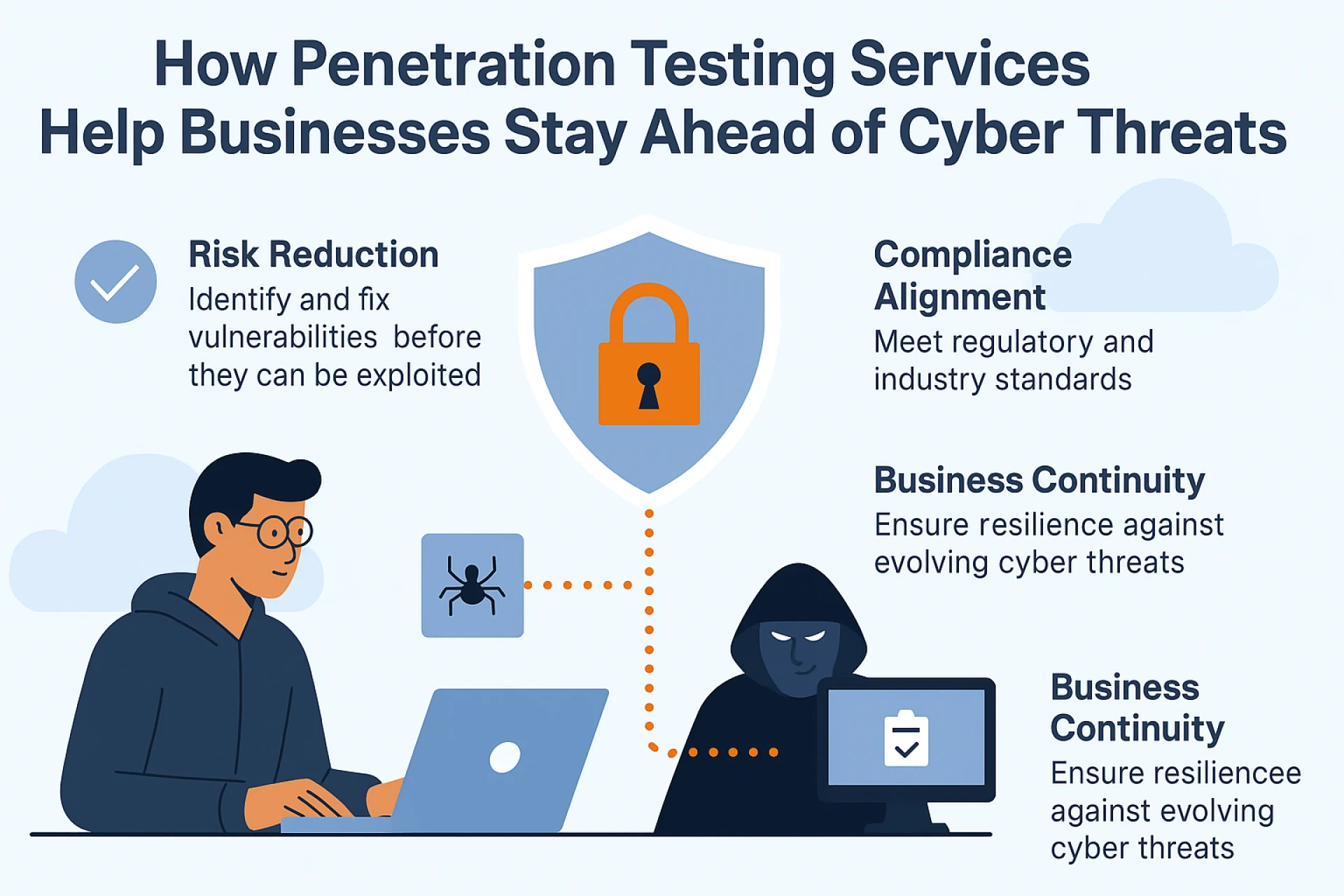
To counter evolving threats, agencies are turning to penetration testing services—tactical assessments that simulate how adversaries would breach real systems.
High Stakes, High Exposure
Whether it’s a water treatment facility, defense contractor, transportation grid, or public health network, these systems are often:
- Legacy-based or patchwork modernized
- Exposed via ICS/SCADA misconfigurations
- Vulnerable to phishing and credential abuse
- Dependent on high-trust vendor ecosystems
One weak link can ripple through national infrastructure.
How Penetration Testing Helps
Penetration testing services offer:
- Red team simulations that mimic nation-state capabilities
- Physical and digital access tests to evaluate hybrid risks
- Operational disruption modeling to test real-world fallout
- Clear remediation guidance to harden mission-critical systems
Beyond Compliance: National Readiness
While frameworks like NIST, FISMA, and CMMC mandate testing, true resilience comes from treating cybersecurity like a live-fire exercise—not a checklist.
Learn how top-tier security teams simulate threats and strengthen defenses at
👉 penetration testing services
Final Word
Defense starts with visibility. Penetration testing services help public sector and critical infrastructure leaders stay ahead of adversaries by preparing for the attacks that matter most—before they happen.












Sign in to leave a comment.