In today’s rapidly evolving digital landscape, everything from banking and education to shopping and healthcare takes place online. While this shift has brought immense convenience, it has also increased the risk of cyber threats for individuals, businesses, and governments alike. As cyber risks grow more complex, enrolling in a cybersecurity course in Bangalore has become essential—not just for tech professionals, but for anyone looking to protect themselves in the digital age.
What is cyber security?
Cybersecurity is the practice of protecting systems, networks, and data from cyber threats such as hacking, malware, phishing, ransomware, and other malicious attacks. It involves a wide range of tools, technologies, and best practices designed to guard digital infrastructure and sensitive information from unauthorized access, disruption, or destruction.
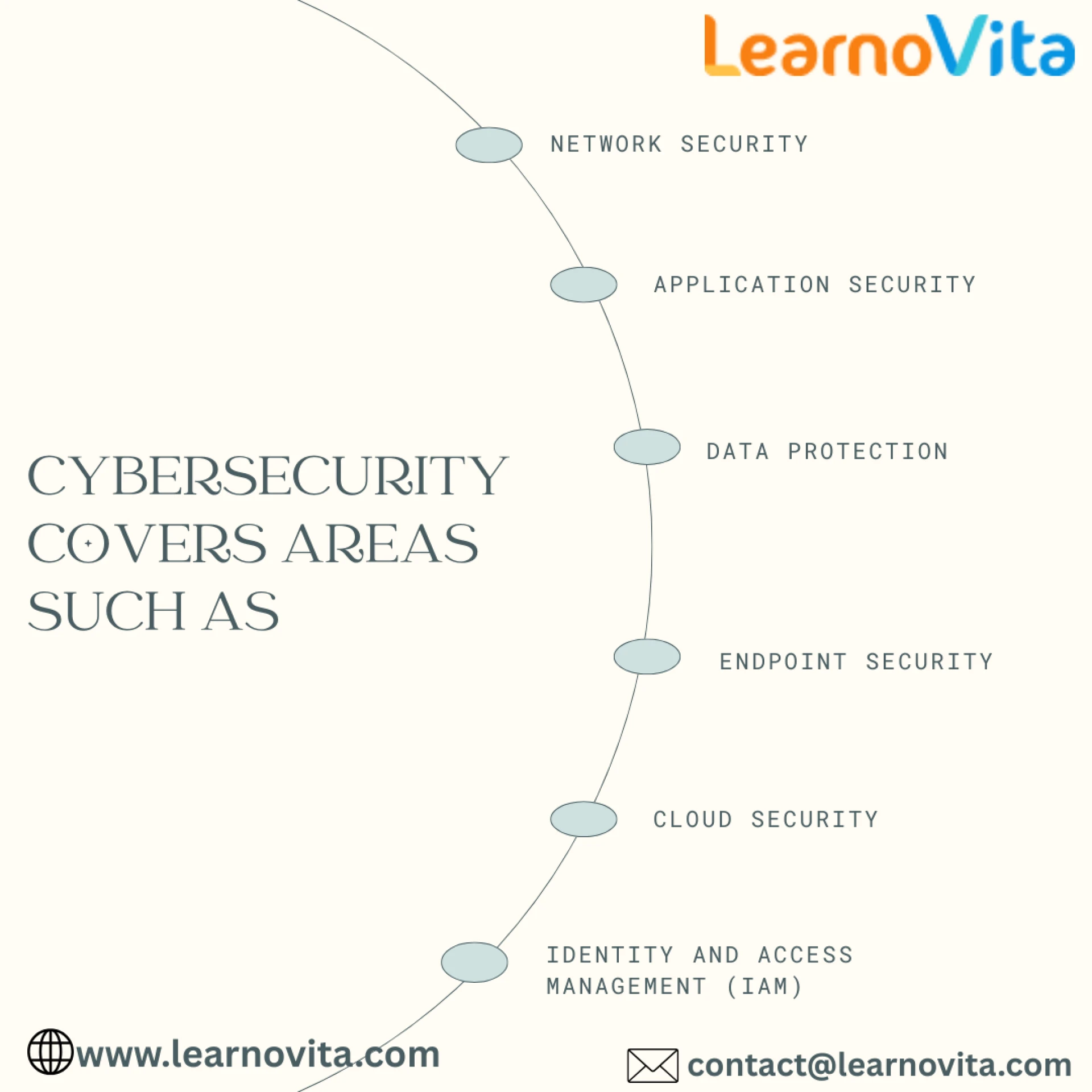
Cybersecurity covers areas such as
1. Network Security
Network security involves protecting computer networks from intrusions, misuse, or unauthorized access. It uses tools like firewalls, intrusion detection systems, and encryption to safeguard data in transit.
2. Application Security
Application security focuses on identifying and fixing vulnerabilities in software and apps. It ensures secure coding practices and protects against threats like SQL injection and cross-site scripting.
3. Data Protection
Data protection involves securing sensitive information from loss, corruption, or theft. It includes encryption, access control, and backup strategies to ensure data privacy and integrity.
4. Endpoint Security
Endpoint security safeguards devices like laptops, smartphones, and desktops from cyber threats. It uses antivirus, device management, and monitoring tools to protect entry points into a network.
5. Cloud Security
Cloud security protects data, applications, and services hosted in cloud environments. It addresses risks like unauthorized access and data breaches through encryption, policies, and compliance controls.
6. Identity and Access Management (IAM)
Identity and Access Management (IAM) plays a crucial role in ensuring that only authorized users can access specific systems and data. At the Best Software Training Institute, students learn how IAM uses authentication, role-based access, and continuous monitoring to prevent unauthorized access and secure digital environments.
How to Stay Protected
Here are some basic but powerful steps individuals and businesses can take:
- Use strong passwords and change them regularly.
- Enable two-factor authentication (2FA) wherever possible.
- Keep software and systems updated to patch known vulnerabilities.
- Install antivirus and firewall protection.
- Avoid clicking on suspicious links or downloading unknown attachments.
- Educate employees and family members about cyber risks.
Conclusion
Cybersecurity isn’t just an IT issue—it’s a personal and societal responsibility. In a world that’s increasingly digital, protecting our online lives is as important as locking our doors. Taking proactive steps today can help us create a safer, more secure digital future for everyone.


















Sign in to leave a comment.