Securing CUI in Microsoft 365: A Guide for Government Contractors
If your organization works with the Department of Defense (DoD) or other government agencies, protecting Controlled Unclassified Information (CUI) within Microsoft 365 isn’t optional—it’s mission-critical. With the rise in cyber threats and evolving compliance requirements, a single misstep can lead to contract loss, fines, or a breach of sensitive government data. So how can you ensure your Microsoft 365 environment is truly secure?
This practical guide outlines how to safeguard CUI while aligning with federal compliance standards.
What Is CUI, and Why Does It Matter?
CUI refers to unclassified government information that still requires protection due to its sensitivity. Examples include:
- Technical data tied to defense projects
- Export-controlled information (ITAR, EAR)
- Procurement and financial documentation
- Personally Identifiable Information (PII)
Failure to protect CUI isn’t just risky—it can result in regulatory penalties, loss of business eligibility, and serious national security concerns.
5 Steps to Protect CUI in Microsoft 365
1. Classify & Label Sensitive Data
You can’t protect what you haven’t identified. Start by:
- Using Microsoft Purview Sensitivity Labels to tag CUI files
- Enforcing Data Loss Prevention (DLP) policies to restrict sharing
- Training employees on CUI identification and proper handling
2. Strengthen Access and Authentication
Limiting CUI exposure starts with access control. Ensure:
- Multi-Factor Authentication (MFA) is active for all users
- Conditional Access Policies are applied based on device, location, or user risk
- Role-Based Access Control (RBAC) is in place to restrict CUI to authorized personnel
3. Encrypt Data at Rest and in Transit
Encryption is essential to prevent data leaks or interception:
- Use Microsoft 365 Message Encryption for sensitive emails
- Enable BitLocker on OneDrive and SharePoint content
- Confirm end-to-end encryption is active in Microsoft Teams
4. Monitor & Respond to Threats in Real Time
Modern attacks require continuous defense. Be proactive with:
- Microsoft Defender for Office 365 to catch phishing and malware
- Microsoft Sentinel for centralized threat visibility
- Automated response through Defender’s advanced analytics
5. Be Audit-Ready for CUI Compliance
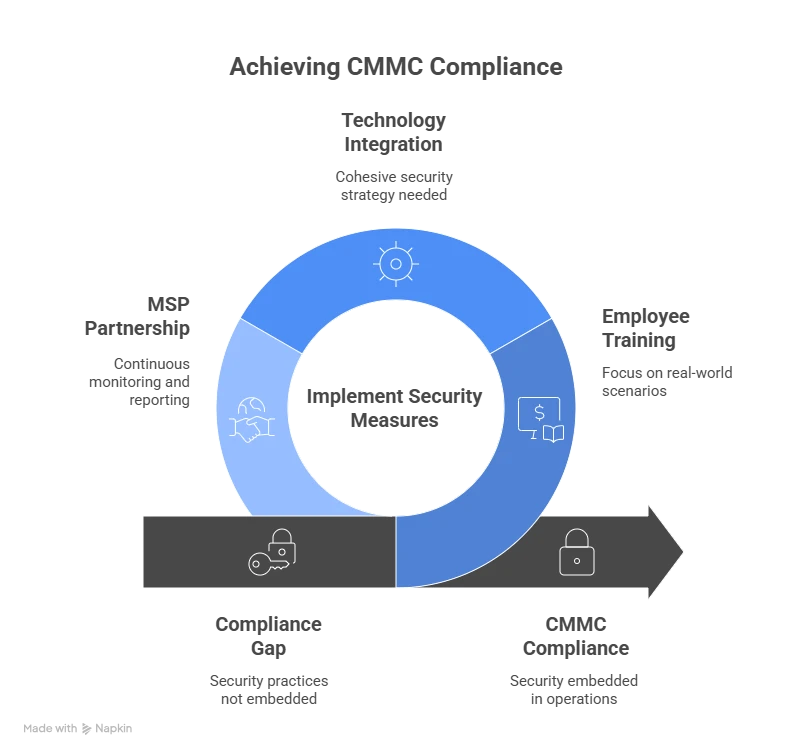
Federal compliance frameworks like NIST 800-171 and CMMC 2.0 require more than a secure setup—they demand documented proof.
- Perform a gap analysis to find vulnerabilities
- Work with a compliance expert to align with DoD expectations
- Enable continuous compliance monitoring and evidence collection
Don’t Wait Until It’s Urgent
Even with the right configurations, your environment may not meet CUI compliance if you're operating in Microsoft 365 Commercial. For many contractors, the critical first step is moving to an authorized, compliant cloud environment.
That’s why organizations preparing for CMMC turn to GCC High migration services—to ensure their data, users, and infrastructure are set up for secure handling of CUI from day one.
Conclusion: CUI Compliance Is a Journey, Not a Checkbox
Securing CUI in Microsoft 365 is an ongoing effort—one that demands more than just the right tools. It requires a strategic approach, informed configuration, employee awareness, and constant alignment with evolving federal requirements. By starting with a compliant foundation and layering on strong controls, your organization can meet DoD expectations, reduce risk, and stay competitive.
Ready to get your environment compliant and secure? Start with a move to GCC High—your first step toward confident CUI protection.















Sign in to leave a comment.