In the evolving landscape of security technology, the rise of cloud-based access control systems marks a significant shift from traditional physical security measures. This advancement offers unprecedented convenience and scalability, transforming how businesses and institutions secure their premises.
By leveraging cloud technology, access control systems have become more adaptable, efficient, and accessible, setting them apart in the realm of security solutions.
The Evolution and Advantages of Cloud-Based Systems
Traditionally, access control systems were predominantly managed on-site, requiring substantial physical infrastructure and hands-on administration. These systems, while effective in their time, posed limitations in terms of scalability, flexibility, and remote management capabilities.
The advent of cloud-based access control has revolutionized this narrative by introducing a platform that transcends these boundaries, offering a multitude of benefits that set it apart.
One of the primary advantages of cloud-based access control is its unparalleled scalability. Businesses can effortlessly expand their security infrastructure as they grow, adding new doors or access points without the need for extensive hardware upgrades or reconfigurations. This scalability not only makes it an ideal solution for growing businesses but also ensures that the security system can evolve with the changing needs of an organization.
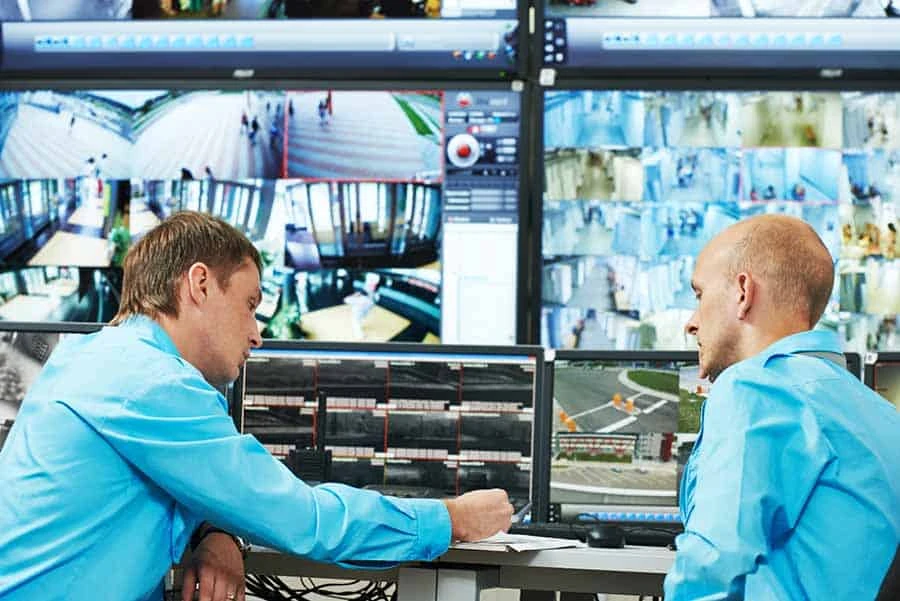
Furthermore, the flexibility and remote management capabilities provided by cloud-based systems are second to none. Administrators can access the system from anywhere in the world, provided they have an internet connection.
This means that managing access permissions, monitoring entry and exit logs, and updating security protocols can be done without being physically present at the site. Such flexibility is invaluable in today’s dynamic work environments, where remote work and flexible schedules are becoming increasingly common.
Security and Integration: The Core Features
At the heart of cloud-based access control's appeal is its robust security framework. By leveraging advanced encryption and secure cloud storage, these systems ensure that sensitive data is protected against unauthorized access and cyber threats. This is a critical consideration in an era where data breaches and cyber-attacks are on the rise.
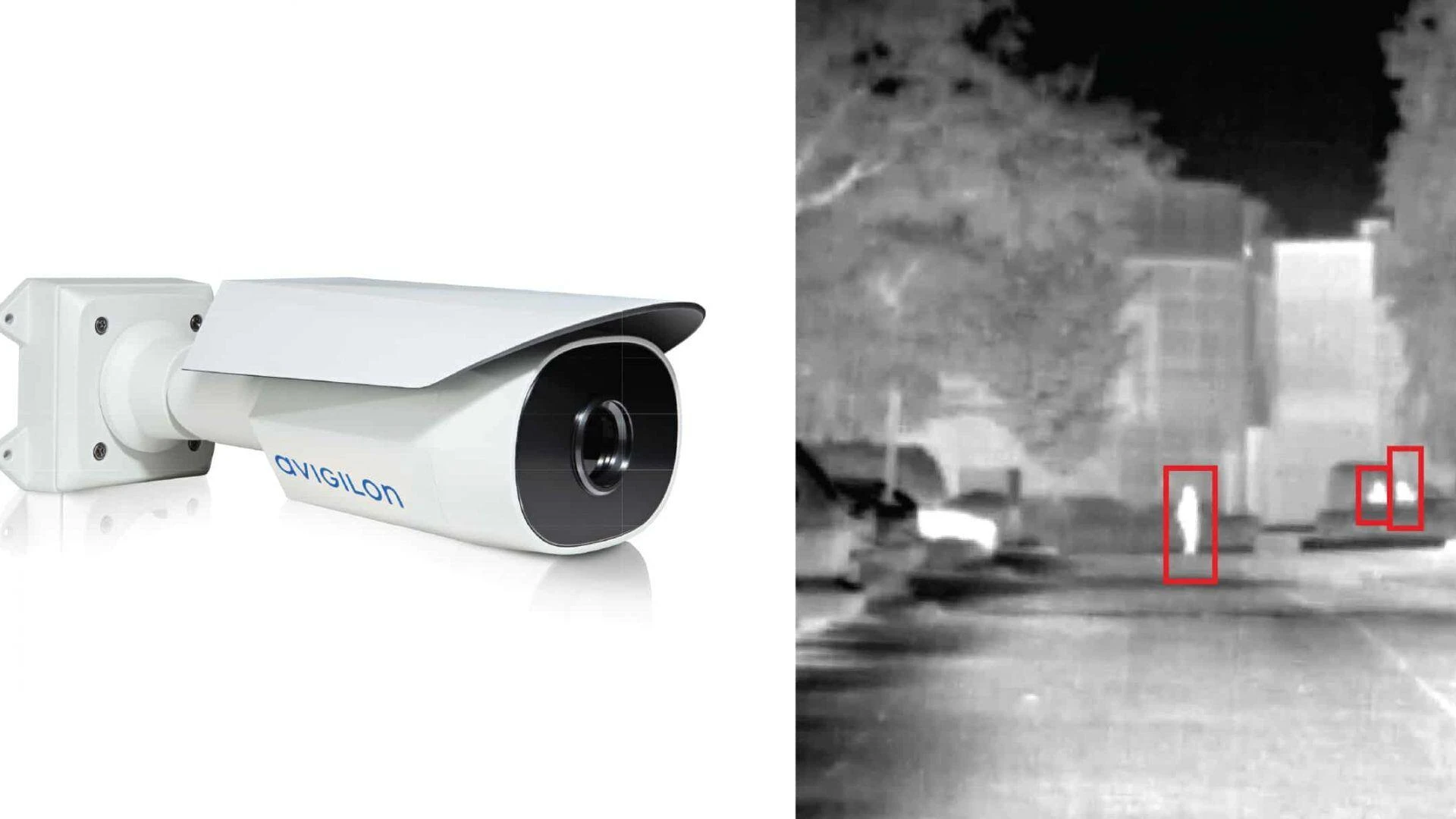
In addition to security, cloud-based systems offer superior integration capabilities. They can seamlessly integrate with other security systems, such as video surveillance and alarm systems, providing a comprehensive security solution.
This integration extends to various business systems, enabling functionalities such as the automatic deactivation of access rights upon employee termination, thereby enhancing overall security and operational efficiency.
The Difference Between Wiegand and OSDP
In the context of access control systems, the difference between Wiegand and OSDP (Open Supervised Device Protocol) represents a significant technological evolution. Wiegand, once the standard for access control communications, is increasingly being replaced by OSDP for its superior security features and flexibility.
OSDP supports two-way communication between readers and controllers, allowing for advanced encryption, continuous monitoring, and the ability to update reader firmware remotely.
This transition reflects the broader move towards more secure, scalable, and efficient access control solutions, much like the shift towards cloud-based systems.
Challenges and Considerations
While cloud-based access control systems offer numerous benefits, there are challenges and considerations to be aware of. Data privacy and security are paramount, necessitating stringent measures to protect against breaches.
Additionally, the reliance on internet connectivity means that any disruptions can impact access control operations. Hence, selecting a reliable cloud provider and ensuring robust cybersecurity measures is crucial.
The Future of Access Control
Looking ahead, the future of access control lies in the continued innovation and integration of cloud technology. As artificial intelligence and machine learning technologies advance, cloud-based access control systems are set to become even more intelligent and autonomous, offering predictive analytics and adaptive security measures.
In conclusion, cloud-based access control systems stand out for their scalability, flexibility, security, and integration capabilities. By addressing the limitations of traditional systems and embracing the potential of cloud technology, these systems offer a forward-looking solution that meets the dynamic needs of modern businesses.
As the security landscape continues to evolve, the importance of adopting such innovative solutions cannot be overstated, ensuring that organizations can protect their assets and people effectively in an increasingly complex world.





















Sign in to leave a comment.