High-risk sites demand precise, resilient access control. These environments include critical infrastructure, large corporate campuses, data centers, and facilities handling sensitive materials. The right mix of technologies lowers risk, speeds responses, and keeps operations running smoothly.
What high-risk sites demand
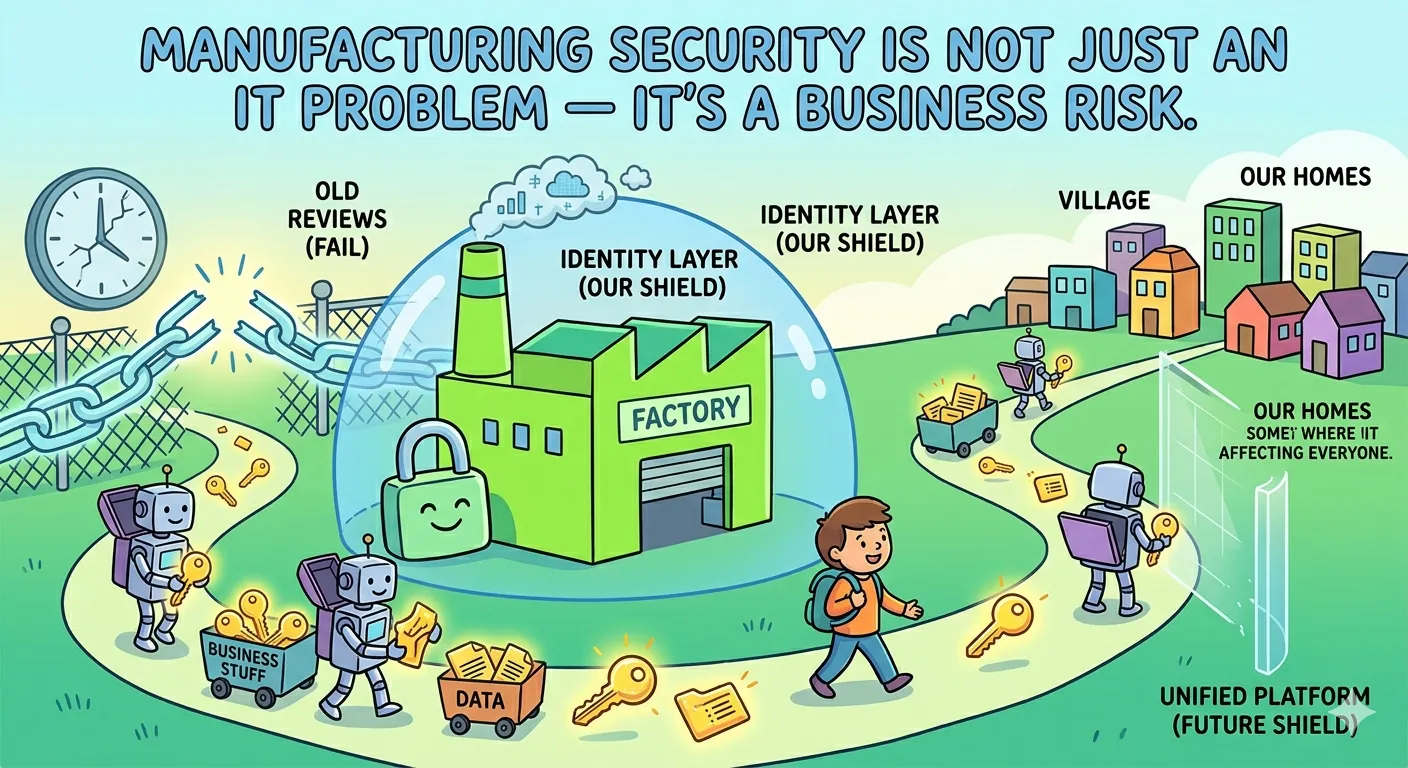
Security goals are clear: verify identities, limit entry, monitor activity, and respond to threats in real time. Access control is not a single tool but a layered system. It combines physical barriers, verification methods, and centralized monitoring to create a credible defense against intrusion and insider risk.
Core technologies powering access control
Modern access control relies on several technologies that work together. The goal is to verify credentials quickly, grant appropriate access, and log events for auditing. Below is an overview of the most impactful technologies in this space.
- Smart cards and readers: Contact or contactless credentials that store user data and permissions. They enable rapid door unlocking while keeping logs of each entry.
- Biometric verification: Fingerprint, iris, facial recognition, or palm print provide a high level of certainty about identity, especially when combined with a strong policy framework.
- Electronic door controllers: Local devices that manage door states, monitor tamper events, and enforce policy at the point of entry.
- Mobile credentials: Smartphones and wearables act as keys. They reduce physical touchpoints and simplify credential management.
- Video analytics and integration: Real-time monitoring ties access events to surveillance feeds, improving post-event analysis and response.
- Alarm and event management platforms: Centralized software that coordinates credential validation, door status, and incident alerts.
All of these technologies must integrate with policy-driven workflows. A well-engineered system enforces least privilege, supports rapid revocation, and aligns with regulatory requirements. The most effective setups use a central identity and access management (IAM) layer that communicates with door controllers and surveillance systems.
Implementation patterns
Implementation varies by site. Here are common patterns that yield reliable results without overengineering.
- Start with a risk assessment. Map all entry points, sensitive zones, and critical assets. Define who needs access and when.
- Choose a modular architecture. Pick a core access control platform and add readers, biometrics, and mobile credentials as needed.
- Enforce strong identity verification. Use multi-factor authentication where possible, combining something you have (credential) with something you are (biometric) or know (PIN).
- Integrate with security operations. Link access events to surveillance and alarm systems for coordinated responses.
- Plan for revocation and changes. Automate credential removal when roles change or personnel depart.
These patterns help ensure the system remains scalable, auditable, and resilient to compromise. A practical deployment favors phased rollouts, rigorous testing, and clear change-management processes.
Technology overview for access control security servicesTechnologyPurposeReal-world exampleSmart cardsCredential storage and door authorizationEmployee badge unlocks office doors and lifts in a secure facilityBiometricsIdentity verification with high certaintyFacial recognition at sensitive access points, with fallback PINMobile credentialsCredential delivery via smartphones or wearablesSmartphone app unlocks dormitory gates and parking barriersElectronic door controllersDoor state management and local decision makingRemote monitoring of door status and tamper alertsVideo analyticsContext for access events and post-event investigationLinking a denied entry to a facial match in surveillance footageAlarm and event platformsCentralized incident planning and responseAutomatic lockdown if multiple sensors trigger
Threat-aware design principles
High-risk sites demand design that anticipates both external attacks and internal misuse. The following principles help teams build robust systems without creating friction for legitimate users.
- Least privilege access: Grant permissions only to the doors and areas a user absolutely needs.
- Fallback and fail-secure modes: If a component fails, critical doors stay locked and alerts fire, not silent.
- Tamper resistance: Use hardware that resists cloning, spoofing, and forced entry attempts.
- Data protection: Encrypt credential data in transit and at rest; enforce strict access to logs.
In practice, this means clear access policies, routine credential audits, and a fast incident response plan. A well-documented policy reduces confusion during a crisis and speeds recovery after an event.
Choosing a provider and solution mix
The right partner delivers a balanced stack, supported by solid service commitments. Look for a system that scales from dozens to thousands of doors, with options to tailor workflows to your industry.
- Interoperability: The system should play well with existing surveillance, badge issuance, and HR systems.
- Auditability: Every entry and denial should be timestamped and easy to review.
- Resilience: Assess uptime guarantees, backup readers, and remote management capabilities.
- Security updates: A clear roadmap for firmware patches and vulnerability handling.
Beyond technology, focus on process. Incident response drills, credential lifecycle management, and continuous improvement cycles keep the solution effective over time. A thoughtful deployment pairs hardware with a disciplined, policy-first approach to access control security services.
Operational considerations for high-risk sites
Operations shape the real-world effectiveness of any access control system. The following considerations help maintain steady protection without slowing work processes.
- Physical layout: Place readers at vehicle entry points, building vestibules, and restricted corridors in lines that mirror workflows.
- Credential hygiene: Regularly refresh credentials, revoke on exit, and monitor for anomalies like credential sharing.
- Monitoring and alerts: Set tiered alerts for different risk levels and ensure on-site staff can respond quickly.
- Testing cadence: Run quarterly tabletop exercises and annual full-scale drills to validate readiness.
When operations are aligned with security controls, you get faster access for legitimate users and fewer false positives. The outcome is smoother daily activity and stronger protection against breaches.
Future-ready trends to watch
As threats evolve, so do access control solutions. Here are a few trends informing next-generation deployments.
- Context-aware access: Systems adjust permissions based on location, time, and risk signals.
- Decentralized identity: Edge devices authenticate locally and share minimal data with central systems.
- AI-driven anomaly detection: Real-time patterns flag unusual entry behavior for quick review.
Adopting these trends can extend the life of your investment and improve resilience. A pragmatic approach blends proven controls with selective, privacy-conscious innovations.

















Sign in to leave a comment.