Introduction
Enterprise security teams are facing a rapidly shifting threat landscape defined by cloud adoption, distributed architectures, and continuous software delivery. Traditional security models, which depend on periodic scans and static rules, are no longer sufficient to protect complex digital ecosystems. Modern attacks exploit misconfigurations, hidden dependencies, and behavioural anomalies that legacy tools struggle to identify. In this environment, organizations require intelligent, always-on security capabilities that move beyond reactive detection. An AI-powered approach to security scanning is becoming central to how enterprises maintain trust, resilience, and operational continuity.
AI Vulnerability Assessment Tool Establishing a Strong Security Baseline
A comprehensive security strategy begins with visibility. The AI Vulnerability Assessment Tool enables enterprises to establish a clear baseline by evaluating applications, infrastructure, and configurations through intelligent analysis.
Unlike conventional assessments that rely on signature matching, this tool interprets code behaviour, system interactions, and historical risk patterns. It uncovers vulnerabilities embedded deep within legacy logic, third-party libraries, and architectural assumptions. By delivering contextual insights rather than raw findings, it allows security teams to understand not just what is vulnerable, but why it matters to business operations.
This foundational clarity is critical for prioritizing remediation and building a sustainable defense model.
AI Vulnerability Scanner Enhancing Continuous Threat Discovery
Static security reviews quickly become outdated as systems evolve. The AI Vulnerability Scanner addresses this challenge by introducing continuous, adaptive scanning across enterprise environments.
Its machine-learning models detect emerging threats by analyzing runtime behavior, configuration drift, and anomalous system activity. This allows it to identify risks that traditional scanners overlook, including subtle logic flaws and environment-specific weaknesses. By reducing false positives and highlighting high-impact vulnerabilities, the scanner helps security teams focus their efforts where it matters most.
Continuous discovery ensures that security posture evolves alongside applications rather than lagging behind them.
Security Automation in SDLC Embedding Protection into Engineering Workflows
Security is most effective when it is built into the development lifecycle rather than applied after deployment. Security Automation in SDLC enables this shift by integrating intelligent security checks directly into development and deployment pipelines.
Automated analysis evaluates code changes, infrastructure updates, and configuration modifications as they occur. This early detection prevents vulnerabilities from reaching production and reduces the cost and complexity of remediation. Development teams receive actionable feedback in real time, improving both speed and quality.
By aligning security with delivery workflows, enterprises achieve secure-by-design engineering without slowing innovation.
AI Security Scanner Delivering Real-Time Behavioural Defense
At the operational layer, the AI Security Scanner plays a critical role in maintaining digital trust. It continuously monitors applications and environments to detect suspicious behaviour, misconfigurations, and policy violations.
Rather than relying solely on predefined rules, the scanner learns normal system behaviour and flags deviations that may indicate compromise or misuse. This behavioural intelligence is particularly valuable for identifying insider threats, lateral movement, and zero-day exploitation attempts.
Real-time scanning transforms security from a periodic audit function into an active, responsive defense capability.
AI Security Scanner as a Strategic Risk Management Capability
Beyond detection, an advanced security scanner contributes to strategic risk management by correlating findings across systems and prioritizing remediation based on business impact. It evaluates how vulnerabilities interact across applications, infrastructure, and data flows.
This holistic perspective allows leaders to make informed decisions about remediation sequencing, investment priorities, and risk acceptance. Security becomes a business-aligned function rather than a purely technical concern.
Through intelligent correlation and prioritization, enterprises gain the ability to reduce exposure systematically rather than reactively.
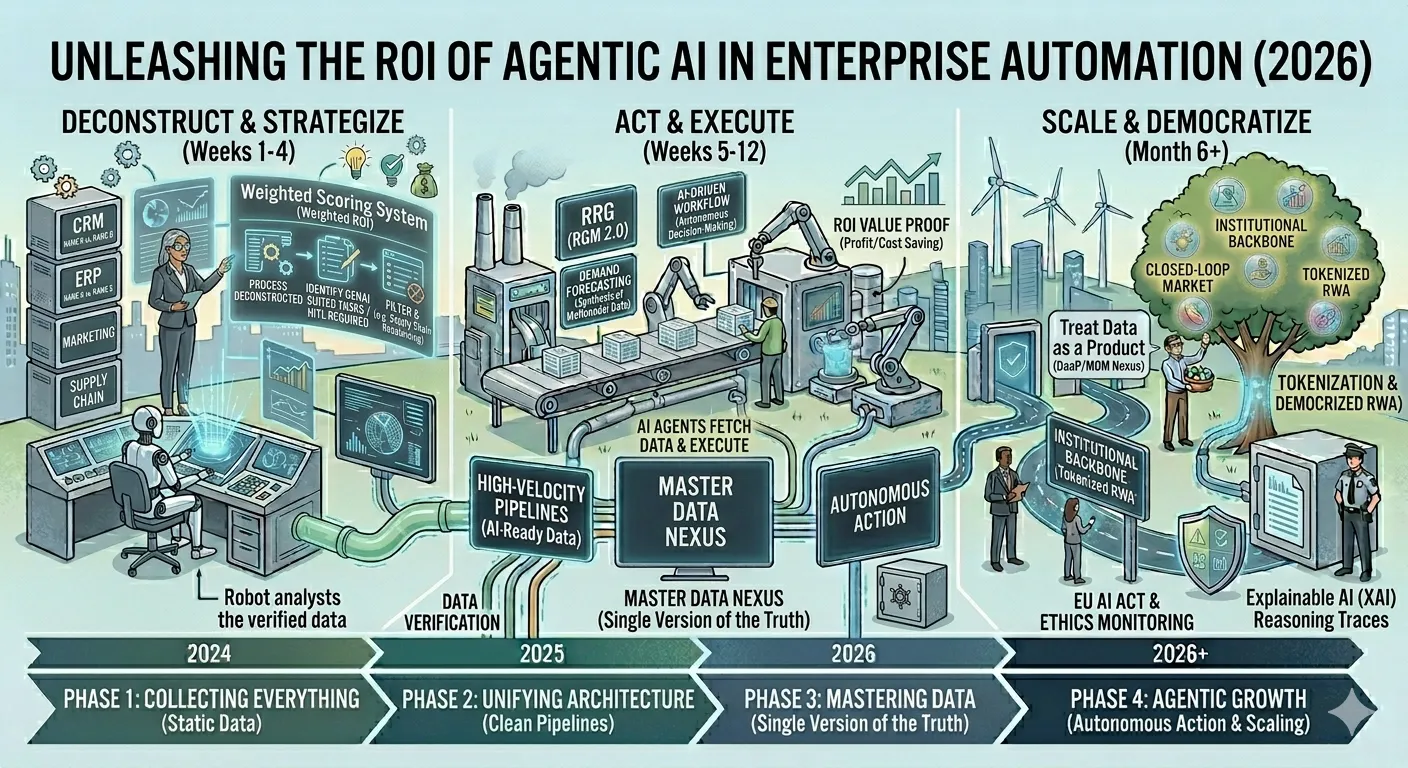
Agentic AI Vulnerability Detection Advancing Autonomous Defense
Modern threats evolve faster than manual response processes can handle. Agentic AI vulnerability detection introduces autonomy into enterprise security by learning from new attack patterns and adapting defenses accordingly.
This capability reasons across interconnected systems, identifying compound risks that emerge only when vulnerabilities interact. It anticipates likely attack paths and highlights weak points before they are exploited. Over time, the system becomes more accurate as it learns from incidents, threat intelligence, and environmental changes.
Autonomous detection shifts security from reactive incident response to proactive risk prevention.
AI Driven Vulnerability Assessment Enabling Intelligent Prioritization
While detection is essential, effective defense depends on prioritization. AI-Driven Vulnerability Assessment brings intelligence to this decision-making process by evaluating vulnerabilities based on exploitability, exposure, and business criticality.
It synthesizes insights from scanners, lifecycle automation, and agentic detection to present a unified risk view. This allows security teams to focus remediation efforts on vulnerabilities that pose the greatest real-world threat rather than those with the highest theoretical severity.
Intelligent prioritization ensures that security resources are applied efficiently and strategically.
Conclusion
Enterprise security is no longer defined by isolated tools or periodic reviews. It requires continuous intelligence, automation, and adaptability across the entire digital ecosystem. The AI Security Scanner represents a pivotal capability in this evolution, providing real-time visibility, behavioural insight, and strategic context for modern defense.
When combined with AI-driven assessment, continuous scanning, SDLC automation, and autonomous vulnerability detection, organizations achieve a resilient security posture that evolves with their environment. This integrated approach allows enterprises to protect critical systems, maintain trust, and support innovation without compromise in an increasingly complex threat landscape.
Have Questions? Ask Us Directly!
Want to explore more and transform your business?
Send your queries to: [email protected]



















Sign in to leave a comment.