In an era where internet security dangers loom large, protecting your website from harmful attacks is critical. An IP address checker is a must-have defense tool. We'll look at the ways for using IP address checkers to strengthen your website's defenses and protect against potential threats.
Understanding IP Address Checkers
What is an IP Address Checker?
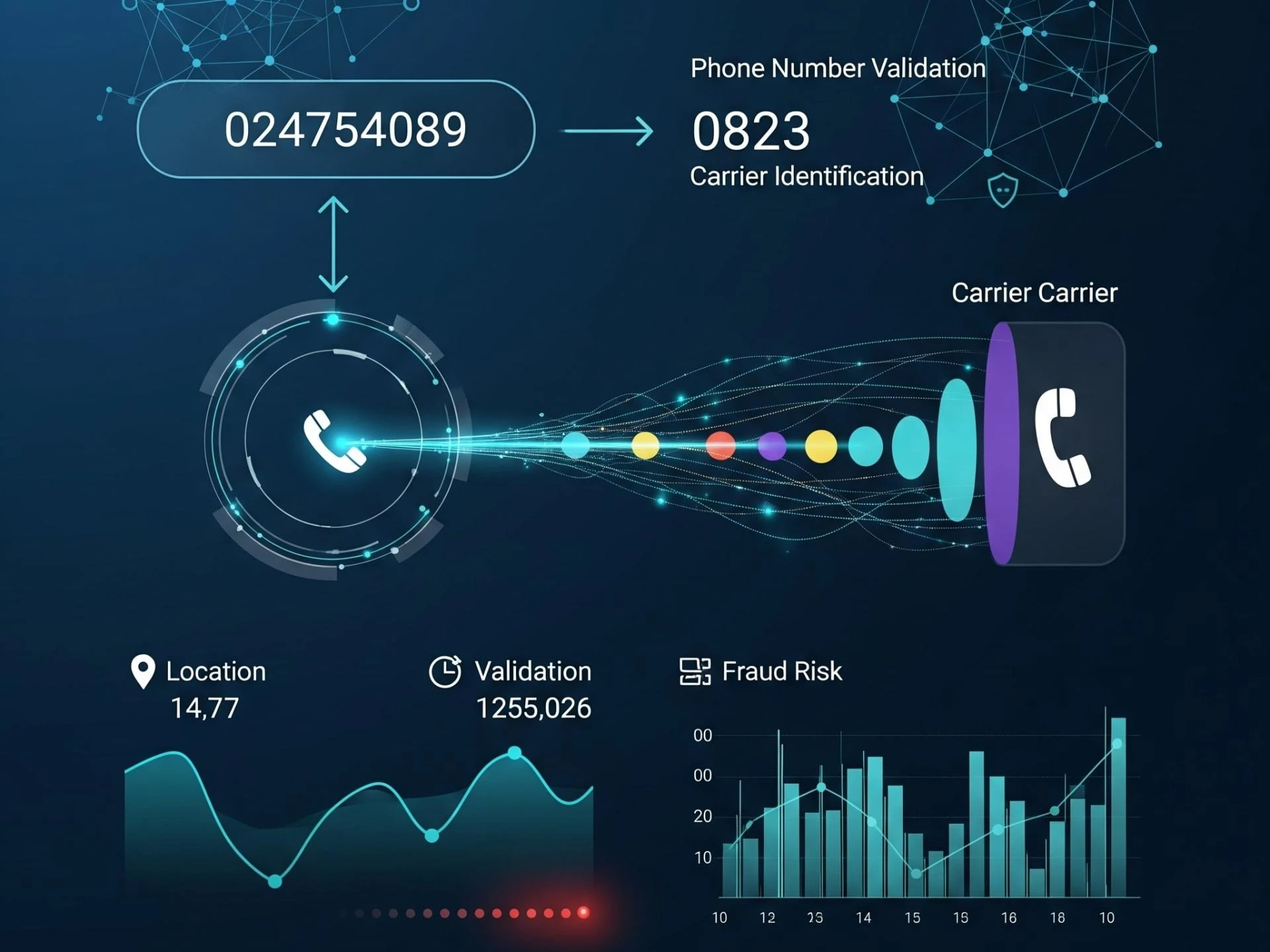
An IP address checker for website is a crucial tool that allows website owners to verify the authenticity and location of visitors based on their IP addresses. By leveraging this tool, website owners can gain valuable insights into user behavior and effectively identify potential security risks. Whether it's ensuring the legitimacy of visitors or detecting suspicious activity, the IP address checker for website plays a pivotal role in safeguarding online platforms. Additionally, by analyzing IP addresses, website owners can tailor their content or services to specific regions or demographics, enhancing user experience and engagement. Overall, integrating an IP address checker for website into security protocols is essential for maintaining the integrity and safety of online assets.
Importance of IP Address Verification
Verifying IP addresses helps prevent unauthorized access, thwart malicious activities such as hacking and phishing attempts, and enhance overall website security. By identifying suspicious IP addresses, website owners can take proactive measures to safeguard their data and assets.
Strategies for Effective IP Address Checking
Real-Time Monitoring
Implement real-time IP address checking to monitor incoming traffic continuously. By analyzing IP addresses in real-time, website owners can promptly detect and block suspicious activities before they escalate into security breaches.
Geolocation Tracking
Utilize geolocation tracking to identify the geographical location of visitors based on their IP addresses. This information enables website owners to implement region-specific security measures and tailor content to target audiences effectively.
Blacklist/Whitelist Management
Maintain a blacklist of known malicious IP addresses and a whitelist of trusted IPs. Regularly update these lists to ensure that unauthorized entities are blocked, while legitimate users can access the website without interruption.
Threat Intelligence Integration
Integrate threat intelligence feeds into your IP address checking system to stay informed about emerging security threats. By leveraging up-to-date threat data, website owners can proactively defend against evolving attack vectors and vulnerabilities.
Automated Response Mechanisms
Implement automated response mechanisms to handle detected security threats swiftly. Automated responses may include blocking suspicious IP addresses, alerting administrators, or triggering additional security protocols to mitigate risks effectively.
Benefits of IP Address Checker Strategies
Enhanced Security
By leveraging IP address checker strategies, website owners can significantly enhance their website's security posture and protect against various cyber threats, including DDoS attacks, SQL injections, and malware infections.
Improved User Experience
Implementing IP address checking mechanisms allows website owners to deliver a seamless and secure browsing experience to their visitors. By detecting and blocking malicious activities, users can interact with the website without encountering security-related disruptions.
Compliance with Regulations
Adhering to IP address checker strategies helps ensure compliance with regulatory requirements and data protection laws. By safeguarding user data and preventing unauthorized access, website owners demonstrate their commitment to protecting user privacy and security.
Conclusion
In conclusion, IP address checker strategies play a crucial role in empowering your website's defense against cyber threats. By implementing real-time monitoring, geolocation tracking, blacklist/whitelist management, threat intelligence integration, and automated response mechanisms, website owners can enhance security, improve user experience, and achieve compliance with regulatory standards. By unveiling these strategies, you can strengthen your website's defenses and safeguard your online assets against potential risks.
FAQ
Can IP address checkers prevent all security threats?
While IP address checkers are effective in detecting and mitigating many security threats, they cannot guarantee protection against all types of cyber attacks. It's essential to implement a comprehensive security strategy that includes multiple layers of defense.
Are IP address checkers compatible with all website platforms?
Yes, most IP address checkers are compatible with a wide range of website platforms and content management systems. However, it's essential to verify compatibility with your specific platform before implementation.
How often should I update my blacklist/whitelist of IP addresses?
It's recommended to update your blacklist/whitelist regularly to ensure that you're blocking unauthorized entities and allowing legitimate users to access your website. The frequency of updates may vary depending on your website's traffic and security requirements.
Can IP address checkers impact website performance?
While IP address checkers may introduce minimal overhead, their impact on website performance is generally negligible. However, it's essential to optimize your IP address checking mechanisms to minimize any potential performance impacts.
Are there any legal considerations when implementing IP address checker strategies?
Yes, it's crucial to ensure that your IP address checker strategies comply with relevant privacy and data protection regulations, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). Be transparent about your data collection and usage practices to maintain legal compliance.
















Sign in to leave a comment.