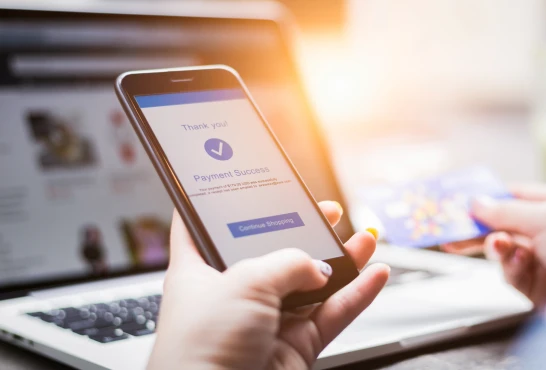
In today’s digital world, protecting sensitive data is not optional. From financial transactions to personal information, organizations are expected to keep data locked down at all times. This is where Hardware Security Modules, commonly known as HSMs, step in. Think of an HSM as the ultimate bodyguard for cryptographic keys, built specifically to keep them safe from both cyber threats and internal misuse.
What Is a Hardware Security Module?
A Hardware Security Module is a physical device designed to securely generate, store, and manage cryptographic keys. These keys are used for encryption, decryption, digital signatures, and authentication. Unlike software-based security tools, HSMs keep cryptographic operations inside tamper-resistant hardware. This means sensitive keys never leave the device, reducing the risk of exposure.
HSMs are widely used in industries that handle high-value data, including banking, healthcare, government, and cloud services. If compliance, trust, and strong security matter, HSMs are usually part of the setup.
Why HSMs Matter
Cyberattacks are getting smarter, and data breaches are expensive. One of the most common attack paths is compromised encryption keys. HSMs solve this problem by isolating key management from general-purpose systems. Even if a server is compromised, the keys remain protected inside the HSM.
HSMs also support regulatory compliance. Standards such as PCI DSS, HIPAA, GDPR, and FIPS 140 require strong encryption and secure key management. Using an HSM helps organizations meet these requirements without cutting corners.
How HSMs Work in Practice
HSMs perform cryptographic functions internally. When an application needs to encrypt data or sign a transaction, it sends a request to the HSM. The operation happens inside the device, and only the result is returned. The key itself never leaves the secure boundary. This setup minimizes attack surfaces and keeps sensitive material out of reach.
Modern HSMs come in different forms, including network-attached devices, PCIe cards, and cloud-based HSM services. Each option supports different performance, scalability, and deployment needs, making it easier to match security to business goals.
Benefits Beyond Security
While security is the main reason to use an HSM, there are practical benefits too. HSMs centralize key management, simplify auditing, and reduce operational risk. They also improve trust with customers and partners by demonstrating a serious commitment to protecting data.
From a performance standpoint, HSMs are optimized for cryptographic operations, which can reduce latency and improve reliability in high-volume environments.
Final Thoughts
Hardware Security Modules have become a core part of modern security architecture as organizations place greater emphasis on protecting sensitive data and meeting compliance requirements. A range of HSM solutions exist to support different industries and use cases. Providers such as Futurex contribute to this space by developing hardware-based security technologies that help organizations manage encryption keys, protect critical assets, and maintain trust in an increasingly digital environment.
















Sign in to leave a comment.