In an era where technology is smaller and more accessible than ever, the "bugged room" is no longer just a plot point in a spy thriller. From corporate boardrooms to private residences, the reality of unauthorized surveillance is a growing concern. Many people assume they can simply buy a cheap wand online to clear a room, but modern "bugs" are far more sophisticated, often using burst transmissions or passive recording to stay invisible.
True security requires a professional approach. This is where hidden wiretap detection experts come into play. These specialists don’t just "look" for cameras; they perform what is known as Technical Surveillance Counter-Measures (TSCM) to identify threats that are physically and electronically invisible to the untrained eye.
The Technical Sweep: Identifying Invisible Signals
The first phase of a professional sweep focuses on the electromagnetic spectrum. Illegal devices are essentially tiny radios or computers, and like all electronics, they leave a digital footprint. Hidden wiretap detection experts use a multi-layered technical approach to hunt down these signals.
- RF Spectrum Analysis: Experts use high-end spectrum analyzers to scan the airwaves. While basic detectors might find a constant signal, pros look for “burst transmitters”- devices that store data and "dump" it in a split-second spike to avoid detection.
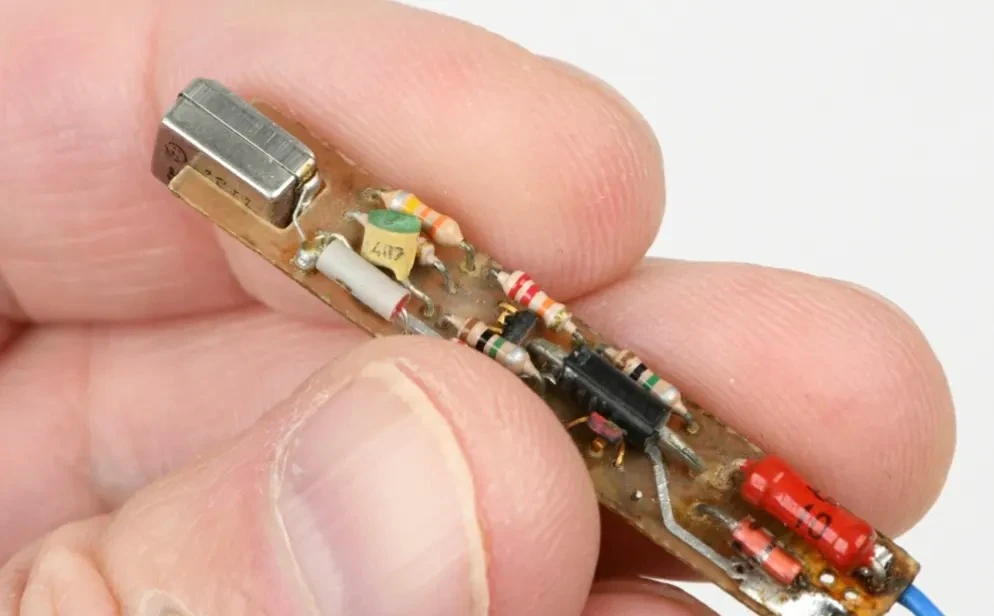
- Non-Linear Junction Detection (NLJD): This is the gold standard for wiretap detection services. An NLJD sends out a signal that reacts with the semiconductor components found in all electronic circuits. Crucially, it can find a bug even if it is turned off, has a dead battery, or is hidden deep inside a wall.
- Thermal Imaging: Even the most efficient microphone generates a tiny amount of heat. Using FLIR (Forward-Looking Infrared) cameras, experts look for "heat blooms" behind paintings, inside smoke detectors, or within furniture that shouldn't be warm.
- Time-Domain Reflectometry (TDR): For physical wiretaps, experts analyze the integrity of phone and data lines. By sending a pulse down the wire, they can find anomalies like a "tap" that changes the resistance or length of the cable pinpointing exactly where a line has been compromised.
The Forensic Audit: Finding What Tech Misses
While high-tech gadgets are essential, they are only half the battle. A device that records locally to an SD card and doesn't transmit a signal won't be caught by a radio scanner. This is where the methodical, hands-on work of wiretap detection services becomes vital.
Experts conduct a grueling "top-to-bottom" physical search of the environment. This isn't just a quick glance behind the curtains; it involves a grid-based dismantling of the room. They pay close attention to:
- Parasitic Devices: Many bugs "hitchhike" on your power. Experts will disassemble power strips, light switches, and wall outlets to look for components that don't belong to the original hardware.
- Visual Anomalies: They look for "white dust" (drywall debris) on the floor, which suggests someone recently drilled a tiny hole for a pinhole camera. They also check for mismatched screws or wall plates that are slightly out of alignment.
- Optical Scopes: Using borescopes - tiny cameras on flexible cables - experts can peer inside HVAC ducts and ceiling voids without tearing down the architecture.
- Carrier Current Detection: Some sophisticated bugs use the building’s own electrical wiring to send audio back to a listener. Experts test the "mains" power lines for these unauthorized data transmissions.
Ultimately, hidden wiretap detection experts provide more than just a sweep; they provide a forensic audit. If a device is found, they don't just rip it out. They follow protocols to preserve fingerprints or MAC addresses that might lead back to the perpetrator. In a world where privacy is increasingly fragile, a professional, multi-layered sweep is the only way to truly reclaim your space.
















Sign in to leave a comment.