A patient management system in 2026 is no longer a simple scheduling and billing tool—it’s a mission-critical platform that orchestrates clinical workflows, patient engagement, revenue cycle processes, and interoperability across the healthcare ecosystem.
For healthcare providers, building a custom patient management system is often the only way to achieve differentiation, scalability, and compliance in a rapidly evolving regulatory and technological landscape. But success depends on three pillars: architecture, compliance, and integration. Get any one of these wrong, and the system becomes a bottleneck instead of a growth engine.
The core architecture decisions that determine whether a custom patient management system scales or breaks under clinical load
Microservices vs. monolithic architecture for PMS development
A monolithic architecture might seem faster to build initially, but it becomes a liability as complexity increases. A patient management system simultaneously handles scheduling, billing, clinical documentation, patient communication, and reporting—each with different performance and scaling requirements.
Microservices architecture solves this by isolating services:
- Scheduling services scale during peak booking hours
- Billing services handle batch processing independently
- Clinical documentation services manage high data throughput without impacting UI responsiveness
- Communication services (SMS, email, patient portals) scale horizontally
This service-level isolation prevents system-wide failures. If one component slows down, the rest of the system continues functioning. More importantly, it enables healthcare organizations to scale from a single clinic to multi-location networks without a full rebuild.
In contrast, monolithic systems often degrade under load because all modules share the same runtime and database dependencies. The result: slower performance, higher downtime risk, and expensive refactoring.
FHIR R4 as the foundation, not an integration layer
Many organizations still treat FHIR as an afterthought—something to “add later” for interoperability. That approach creates long-term technical debt.
A modern patient management system should be built with FHIR R4 as the core data architecture, not as a translation layer. This means:
- Patient records are structured as FHIR resources from day one
- APIs are natively FHIR-compliant
- Data exchange is standardized across systems
The benefits are immediate and compounding:
- Seamless integration with EHRs and payer systems
- Faster onboarding of third-party applications
- Reduced complexity in interoperability projects
- Built-in compliance readiness for data exchange standards
Organizations that retrofit FHIR later often face data mapping inconsistencies, performance overhead, and limited scalability in integrations.
Cloud-native deployment with hybrid PHI architecture
By 2026, the majority of healthcare providers have adopted cloud-based infrastructure—but not all workloads belong in the public cloud.
The optimal approach for a patient management system is a hybrid PHI architecture:
- Sensitive PHI storage: On-premises or private cloud environments
- Compute-intensive workloads: Public cloud (AI scheduling, analytics, reporting)
- Patient-facing applications: Cloud-hosted for scalability and accessibility
This model balances security with performance:
- Ensures strict control over protected health information (PHI)
- Enables rapid scaling of compute-heavy operations
- Reduces infrastructure costs without compromising compliance
Cloud-native design also supports containerization, orchestration (e.g., Kubernetes), and automated scaling—essential for handling unpredictable clinical workloads.
HIPAA, HITECH, and state-level compliance requirements that must be built into a patient management system from the first line of code
PHI handling architecture for patient management systems
Compliance is not a feature—it’s an architectural requirement. A patient management system must embed security controls at every layer.
Key safeguards required in 2026 include:
- AES-256 encryption for data at rest and in transit
- Immutable audit logging with six-year retention
- Role-based access control (RBAC) enforced at the data layer
- Multi-factor authentication (MFA) for all users accessing ePHI
Critically, RBAC should not be limited to the UI. Access policies must be enforced at the API and database levels to prevent unauthorized data exposure.
Audit logs must also be tamper-proof. This is essential not only for compliance but for forensic analysis in case of breaches.
SOC 2 Type II and HITRUST certification as procurement prerequisites
Healthcare buyers in 2026 are far more stringent. Enterprise hospital systems often require:
- SOC 2 Type II reports
- HITRUST certification
These are no longer “nice-to-have” credentials—they are procurement gatekeepers.
Building a patient management system with these standards in mind from the start has significant advantages:
- Faster sales cycles with enterprise clients
- Reduced risk of compliance gaps
- Lower long-term costs compared to retrofitting
Retrofitting compliance after development typically involves redesigning logging systems, access controls, and infrastructure—often at 2–3x the original cost.
State-specific patient data regulations beyond HIPAA
HIPAA provides a federal baseline, but state regulations often go further. For example:
- California mandates stricter patient data confidentiality requirements
- New York enforces enhanced cybersecurity obligations
- Other states are rapidly introducing their own healthcare data laws
A scalable patient management system must support jurisdiction-aware compliance:
- Configurable data handling policies
- Region-specific consent management
- Flexible storage and processing rules
Without this, organizations expanding across states face costly re-engineering efforts for each new market.
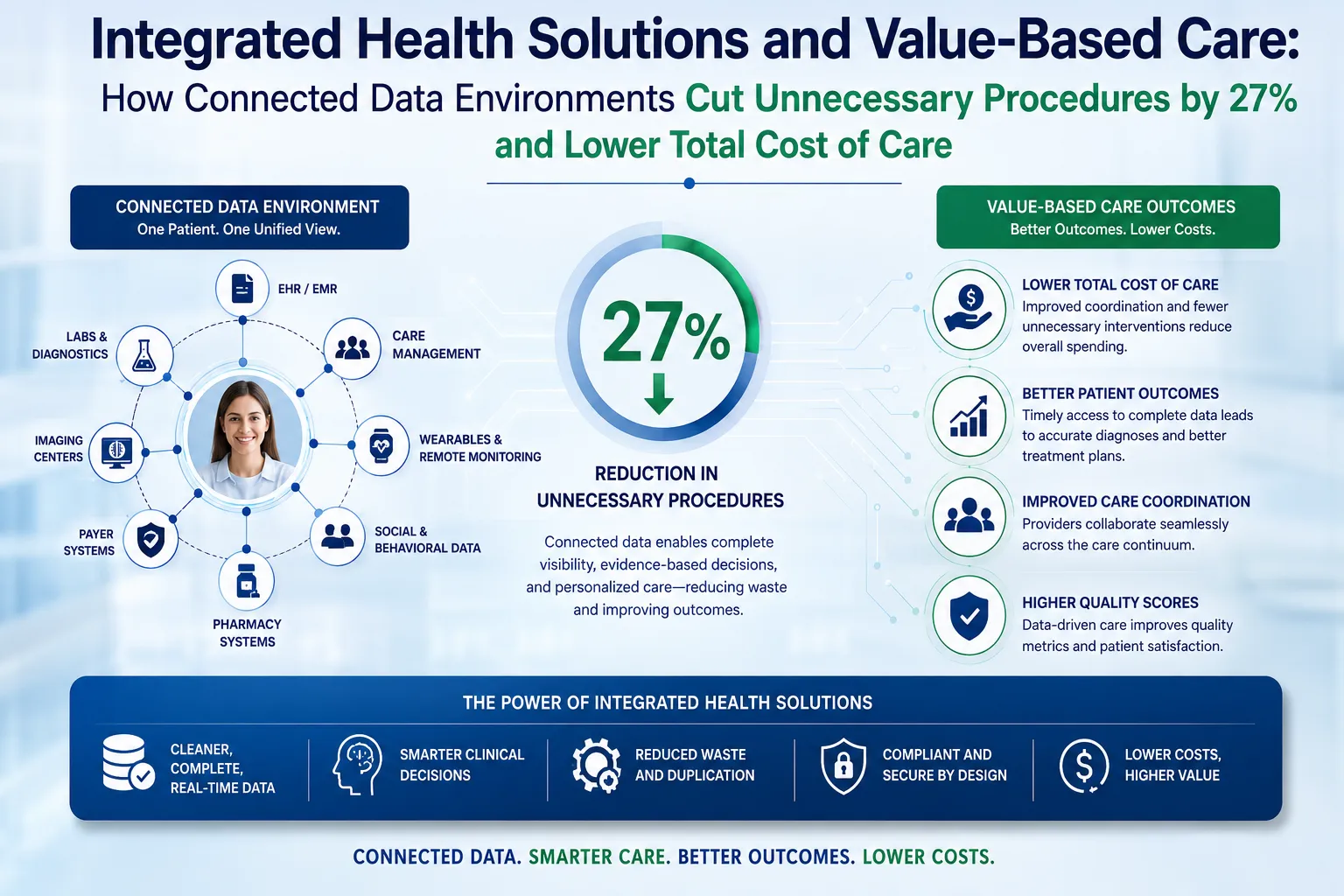
The integration layer: connecting a custom patient management system to EHRs, payers, devices, and patient-facing platforms
EHR integration depth and SMART on FHIR authentication
A patient management system cannot operate in isolation. Deep integration with EHRs is essential.
Using SMART on FHIR enables:
- Contextual app launch within EHR workflows
- Secure authentication and authorization
- Real-time, bidirectional data exchange
This allows:
- Scheduling data to flow directly into clinical documentation
- Patient records to remain consistent across systems
- Providers to avoid duplicate data entry
Without deep integration, standalone systems create friction, inefficiencies, and clinician dissatisfaction.
Payer connectivity and eligibility verification in real time
Revenue cycle inefficiencies often begin at the front desk—not in billing.
A modern patient management system should integrate:
- Real-time eligibility verification APIs
- Prior authorization workflows
- Automated claims rule validation
This ensures:
- Accurate patient coverage information at scheduling
- Reduced claim denials
- Faster reimbursement cycles
By embedding payer logic directly into the system, organizations eliminate downstream errors and improve financial performance.
Conclusion
Building a patient management system in 2026 requires more than assembling features—it demands a strategic approach to architecture, compliance, and integration.
- Architecture determines scalability and performance
- Compliance ensures trust and market access
- Integration defines usability and ecosystem connectivity
Organizations that invest in these foundations early can create platforms that not only meet today’s requirements but adapt to future regulatory changes, payer demands, and technological advancements.


















Sign in to leave a comment.