Cyber threats are no longer isolated IT issues — they are enterprise-wide risk factors affecting compliance, finances, operations, and customer trust. Selecting the right Cybersecurity Audit Company determines whether vulnerabilities are discovered early or exploited at scale.
Recent security assessments across Indian enterprises show that organizations conducting structured cybersecurity audits reduce breach exposure by up to 47%. However, choosing the wrong audit partner can result in incomplete risk analysis, compliance gaps, and false security assurance.
With regulatory scrutiny intensifying and cyber incidents rising more than 24% annually, decision-makers must evaluate cybersecurity audit providers using a strategic, risk-focused approach aligned with compliance, resilience, and operational continuity.
Why Is Choosing the Right Cybersecurity Audit Partner a Strategic Decision?
Cybersecurity audits influence regulatory readiness, cyber risk mitigation, and enterprise resilience. An experienced audit provider delivers:
- Comprehensive vulnerability visibility
- Compliance alignment
- Risk prioritization frameworks
- Security maturity benchmarking
- Incident preparedness insights
Organizations that partner with specialized audit experts achieve 35% faster remediation cycles and improved governance transparency.
What Core Capabilities Should a Cybersecurity Audit Company Provide?
Risk-Based Security Assessment
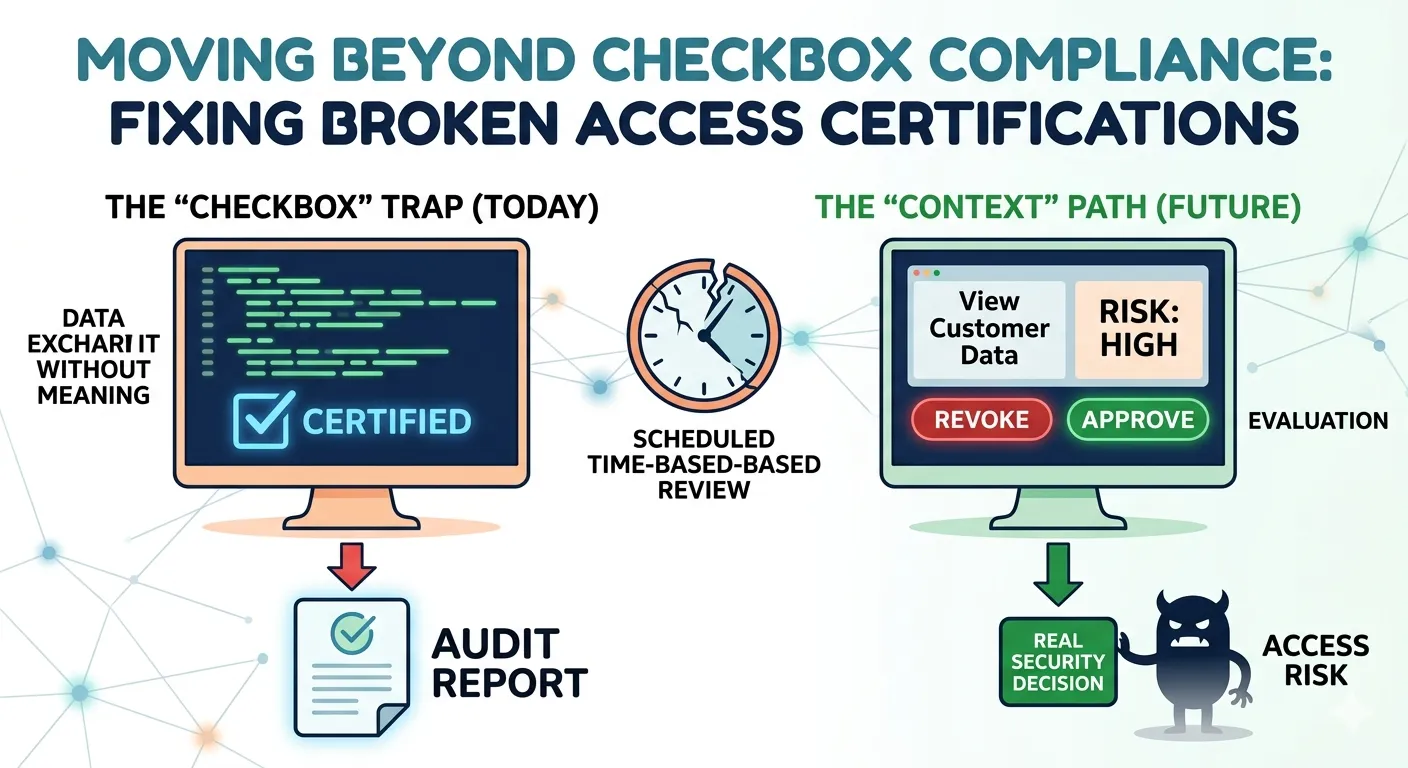
A reliable audit partner performs risk-prioritized evaluations rather than checklist-based scans.
Key inclusions:
- Network vulnerability assessment
- Application security testing
- Cloud configuration review
- Identity and access management analysis
- Threat exposure mapping
Internal enterprise studies show risk-based audits identify 60% more critical vulnerabilities than generic security scans.
Compliance & Governance Alignment
Enterprises must comply with multiple frameworks across industries.
A capable provider delivers structured IT audit and compliance services aligned with:
- ISO/IEC 27001 standards
- RBI cybersecurity guidelines
- SEBI IT governance directives
- Data protection regulations
- Sector-specific compliance mandates
Organizations adopting compliance-focused audits improve inspection readiness by over 40%.
Continuous Security Monitoring & Reporting
Modern cybersecurity requires ongoing risk visibility rather than one-time assessments. A Cybersecurity Audit Company delivers continuous monitoring frameworks that help organizations detect threats early and maintain compliance readiness.
Essential reporting features include:
- Executive risk dashboards
- Compliance gap analysis
- Threat trend reporting
- Remediation prioritization insights
- Audit trails for regulatory review
Enterprises with continuous monitoring reduce security blind spots by 38%.
How Important Is Industry Experience and Domain Expertise?
Industry-specific threat patterns require contextual understanding.
Sector Expertise Matters
Different sectors face unique cyber risks:
- Financial services — fraud, transaction manipulation
- Healthcare — patient data protection risks
- eCommerce — payment security threats
- Manufacturing — operational technology vulnerabilities
Security research indicates industry-specialized auditors improve threat detection accuracy by 42%.
Understanding India’s Regulatory Landscape
Cybersecurity governance in India continues to evolve. Organizations must align with national incident reporting and cybersecurity practices guided by Indian Computer Emergency Response Team advisories.
Audit providers familiar with India-specific regulations ensure compliance preparedness and faster regulatory response.
What Security Testing Methodologies Should Be Used?
Vulnerability Assessment & Penetration Testing (VAPT)
A comprehensive audit must include structured testing methodologies.
Testing approaches include:
- Automated vulnerability scanning
- Manual penetration testing
- API security testing
- Configuration reviews
- Privilege escalation simulations
Organizations conducting VAPT identify up to 70% of exploitable weaknesses before attackers do.
Cloud & API Security Evaluation
Cloud adoption across Indian enterprises is growing by over 26% annually. Misconfigured APIs and storage permissions remain leading breach causes.
Audit providers should evaluate:
- Identity and access policies
- Encryption standards
- API authentication mechanisms
- Data storage exposure risks
Improved cloud governance reduces unauthorized access incidents by nearly 50%.
Why Is Scalability Assessment Essential for Growing Enterprises?
As businesses expand, infrastructure complexity increases. Security frameworks must scale accordingly.
Audit focus areas for scalability:
- Microservices architecture security
- Third-party integrations
- Multi-location access controls
- Remote workforce security posture
- Hybrid cloud infrastructure protection
Security audits designed for scalability reduce system refactoring risks by 30% during expansion.
How Should Reporting Transparency and Remediation Guidance Be Evaluated?
An audit is valuable only if findings translate into actionable improvements.
Effective audit reports include:
- Risk severity classification
- Business impact analysis
- Step-by-step remediation guidance
- Compliance gap mapping
- Executive-level summaries
Organizations receiving structured remediation guidance resolve vulnerabilities 50% faster.
What Certifications and Standards Indicate Audit Credibility?
Security certifications demonstrate adherence to global standards and auditing best practices.
Look for expertise aligned with:
- ISO/IEC 27001 auditing practices
- Certified ethical hacking methodologies
- Risk management frameworks
- Information security governance standards
Certified auditors improve assessment reliability and compliance accuracy.
How Does Incident Response Evaluation Improve Security Readiness?
Security incidents are inevitable. Preparedness determines impact severity.
Audit providers should evaluate:
- Incident detection systems
- Threat monitoring capabilities
- Response workflow readiness
- Recovery and disaster response procedures
Organizations with tested incident response frameworks contain breaches 52% faster.
Why Should Enterprises Evaluate Data Protection & Privacy Controls?
Data protection regulations demand strict safeguards for personal and financial information.
Audit focus areas include:
- Encryption implementation
- Data classification policies
- Backup and recovery integrity
- Endpoint protection mechanisms
- Data loss prevention strategies
Security reviews show 68% of breaches involve sensitive data exposure, emphasizing strong protection controls.
What Questions Should You Ask Before Selecting an Audit Partner?
- Do they provide risk-based security assessments?
- Are their audits aligned with regulatory compliance frameworks?
- Do they include cloud and API security evaluation?
- Will they provide remediation guidance and security roadmaps?
- Can they support long-term security improvement strategies?
Structured evaluation ensures alignment with enterprise security goals.
Signs You May Have Chosen the Wrong Audit Provider
- Reports lack actionable remediation steps
- Compliance gaps remain unresolved
- No executive-level risk insights
- Limited visibility into cloud or API security
- Inadequate documentation for regulatory audits
Choosing the right partner prevents costly reassessments and compliance failures.
Key Outcomes of Selecting the Right Cybersecurity Audit Company
- Reduced cyber risk exposure
- Faster regulatory compliance readiness
- Improved security governance maturity
- Enhanced incident response preparedness
- Stronger stakeholder confidence
- Long-term cyber resilience
Organizations that invest in the right audit expertise strengthen operational continuity and digital trust.
FAQs
1. What factors matter most when selecting a cybersecurity audit provider?
Evaluate expertise, compliance alignment, testing methodologies, reporting transparency, industry experience, and ability to deliver actionable remediation guidance.
2. How do cybersecurity audits support regulatory compliance?
They identify compliance gaps, validate security controls, document safeguards, and prepare organizations for regulatory inspections and audits.
3. Should audits include cloud and API security assessments?
Yes. Cloud environments and APIs present major attack surfaces requiring evaluation of permissions, encryption, authentication, and configuration security.
4. How often should enterprises conduct cybersecurity audits?
Most organizations perform annual audits, while regulated industries and high-risk environments conduct quarterly assessments for continuous risk monitoring.
5. Can cybersecurity audits improve incident response readiness?
Yes. Audits evaluate detection systems, response workflows, and recovery procedures, enabling faster containment and reduced operational disruption.
















Sign in to leave a comment.