You have no clue about when you coincidentally permit infections to go into your framework. The most well-known conduct is exploring to risky connections. Ordinarily, digital aggressors shoot messages to irregular messages with the expectation that somebody will inadvertently open their messages and snap the malevolent connections in them. It is simply a question of an accidental snap, and the web aggressors would get total admittance to your framework mcafee.com/activate

mcafee.com/activate
Similar Reads
Browse topics →
NAS Meets the Edge: Decentralized Storage Solutions for the Age of IoT

STAKE.CH: Die Zukunft des Krypto-Handels

Top Benefits of People Counting software for Your Business growth

MEAN Stack Development: The Ideal Choice for Startup Web Solutions

Why Partnering With a Web Application Development Company is Crucial For…

Top Things to Consider When Hiring a IoT Development Company for Busines…

An Important Aspect of AI is Customer Segmentation

14 Tips to Optimize Drupal Website Performance
T
Top 12 performance marketing agencies to improve your ROI in 2023
More in Technology
Browse all in Technology →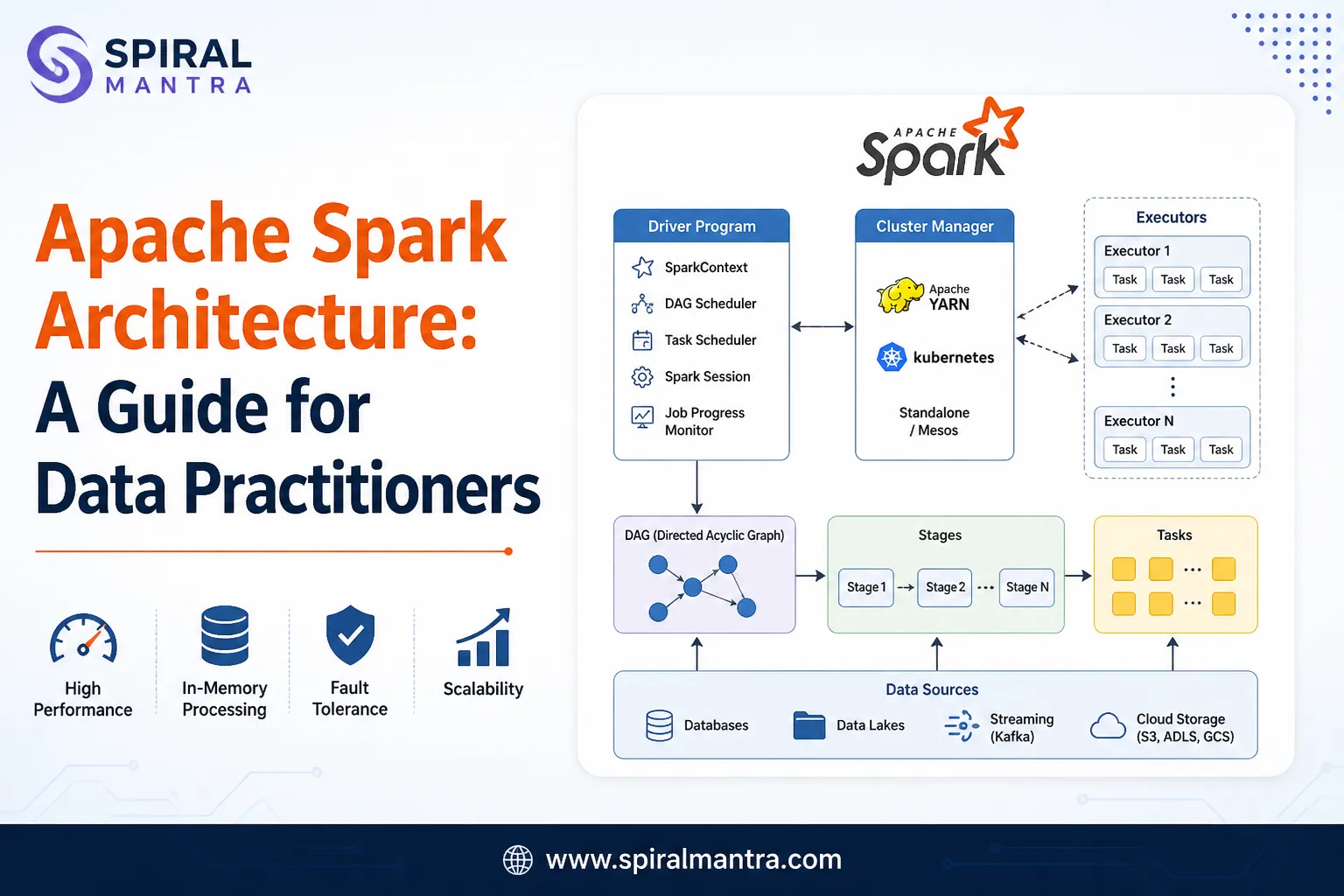 Technology
Technology
Apache Spark Architecture: a Guide for Data Practitioners
 Technology
Technology
Don't Start a Hybrid Crypto Exchange Until You Understand This Cost Fact…
 Technology
Technology
How Speech Analytics Improves Call Center Performance Management
 Technology
Technology
Everyone Wants to Build a Crypto Wallet but Few Know What It Really Take…
 Technology
Technology
The Death of the Stock Photo: Elevating Corporate Visuals with Native AI
 Technology
Technology
Installing Pop!_OS 24.02 LTS
Sign in to leave a comment.