Cybersecurity is the defense against many types of attacks on devices and services that are connected to the internet. It is the process of protecting networks, systems, and data from illegal access, data breaches, and online threats. Because of the growing reliance on technology for government, corporate, and personal activities, cyber security has emerged as a major concern for organizations all over the world in our Cyber Security Course in Bangalore.

Cybersecurity Types
Specialized fields that individually secure certain facets of digital systems, networks, and data are included in cyber security. The main categories of cyber security are listed below:
1. Security of Networks
Safeguarding computer networks' accessibility, confidentiality, and integrity is known as network security. It seeks to protect the network infrastructure from dangers such as illegal access, data breaches, and cyberattacks.
2. Data Protection
The main goal of information security is to shield private information against unwanted access, alteration, or destruction. This comprises information sent via networks, saved in files, and stored in databases.
3. Safety of Applications
Protecting software programs against flaws that hackers could take advantage of is the main goal of application security. From creation to deployment and upkeep, it guarantees the security of applications.
4. Protection of Endpoints
Endpoint security safeguards network-connected devices, including PCs, tablets, and smartphones. These endpoints are frequently targeted by cybercriminals because they act as gateways to the larger network.
5. Protection of Clouds
Cloud security is concerned with protecting information, programs, and services that are housed on cloud computing platforms. Securing these platforms is crucial as more companies shift to cloud environments in order to guard against data breaches and illegal access in our Cyber Security Online Course.
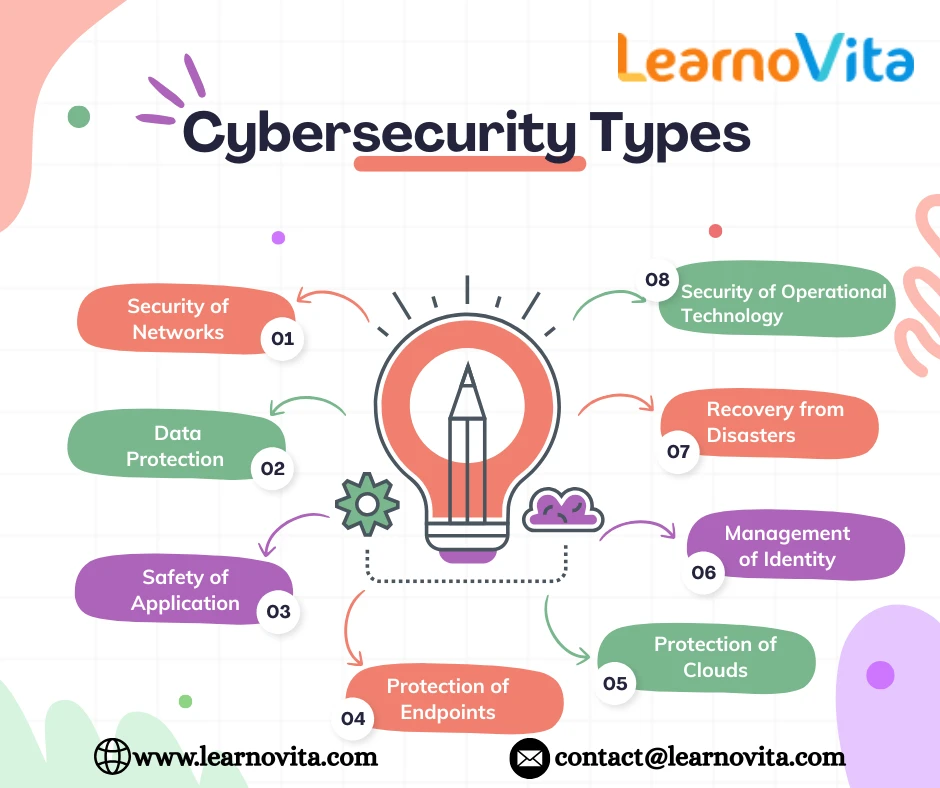
6. Management of Identity and Access (IAM)
IAM, which guarantees that only authorized users can access particular systems or data, is a crucial part of cyber security. It encompasses procedures and tools for controlling user identification, authorization, and authentication.
7. Recovery from Disasters
In the event of a cyberattack or natural disaster, this kind of cyber protection guarantees that businesses can carry on with their activities and recover swiftly. It entails getting staff, procedures, and systems ready to deal with interruptions.
8. Security of Operational Technology (OT)
The software and hardware systems utilized in the transportation, energy, and manufacturing sectors are safeguarded by OT security. These systems regulate physical processes, thus protecting them from interference or harm is essential.
Conclusion
Our digital lives are shielded from the increasing risk of cyberattacks by cyber security. Protecting sensitive data has become more crucial as our reliance on technology for both personal and professional purposes grows. We may greatly lower the risk of cyber threats by comprehending the fundamentals of cyber security and implementing strong security procedures.


















Sign in to leave a comment.