Mobile applications have become an important technology through which businesses connect with customers and provide them with products and services. With the massive increase in use of mobile applications for business purposes, application security has become a major aspect that companies need to take care of.
What Are The Critical Pain Points Of Application Security?
Business apps handle personal details, financial data, device permissions, business logic, etc. If this information is exposed because of weak security, companies may face financial loss, legal issues, and severe damage to brand credibility. The critical pain points of business application security are:
1. Growing Volume and Complexity of Security Threats
Attack techniques evolve fast, and business applications face a wide range of risks such as data exposure, runtime tampering, and logic manipulation. Companies must constantly update their mobile application security measures to stay ahead.
2. Absence of DevSecOps Practices
Most development teams still focus heavily on app features, not protection. Without integrating security practices throughout the Software Development Life Cycle (SDLC), applications often ship with avoidable vulnerabilities. Promoting DevSecOps (Development, Security, and Operations) helps teams detect issues early, reduce rework, and strengthen overall mobile application security.
3. Developers Struggling With Priorities
Developers often prioritize delivering features quickly. Without dedicated training in application security, security tasks may be overlooked or deprioritized. Companies must ensure that development teams have the time, tools, and knowledge required to create secure apps.
4. Compliance and Security Requirements
The global shift toward strict data protection rules has increased expectations from app developers. More checks, audits, and guidelines now apply to application security, and many companies must upgrade their processes to align with government and industry standards. Even with compliance, businesses must add additional layers of protection using strong app security practices.
5. Failing Compliance Audits
Compliance audits validate whether an app meets necessary security requirements. When a business application fails these checks, it affects market trust and can lead to fines or operational delays. Fixing audit failures is difficult if developers are not fully trained in secure coding practices.
Addressing the above pain points will make business applications more secure and protect sensitive user information and user trust. This will help to increase business revenue as well as customer satisfaction.
Strengthen Business Application Security With Bugsmirror MASST
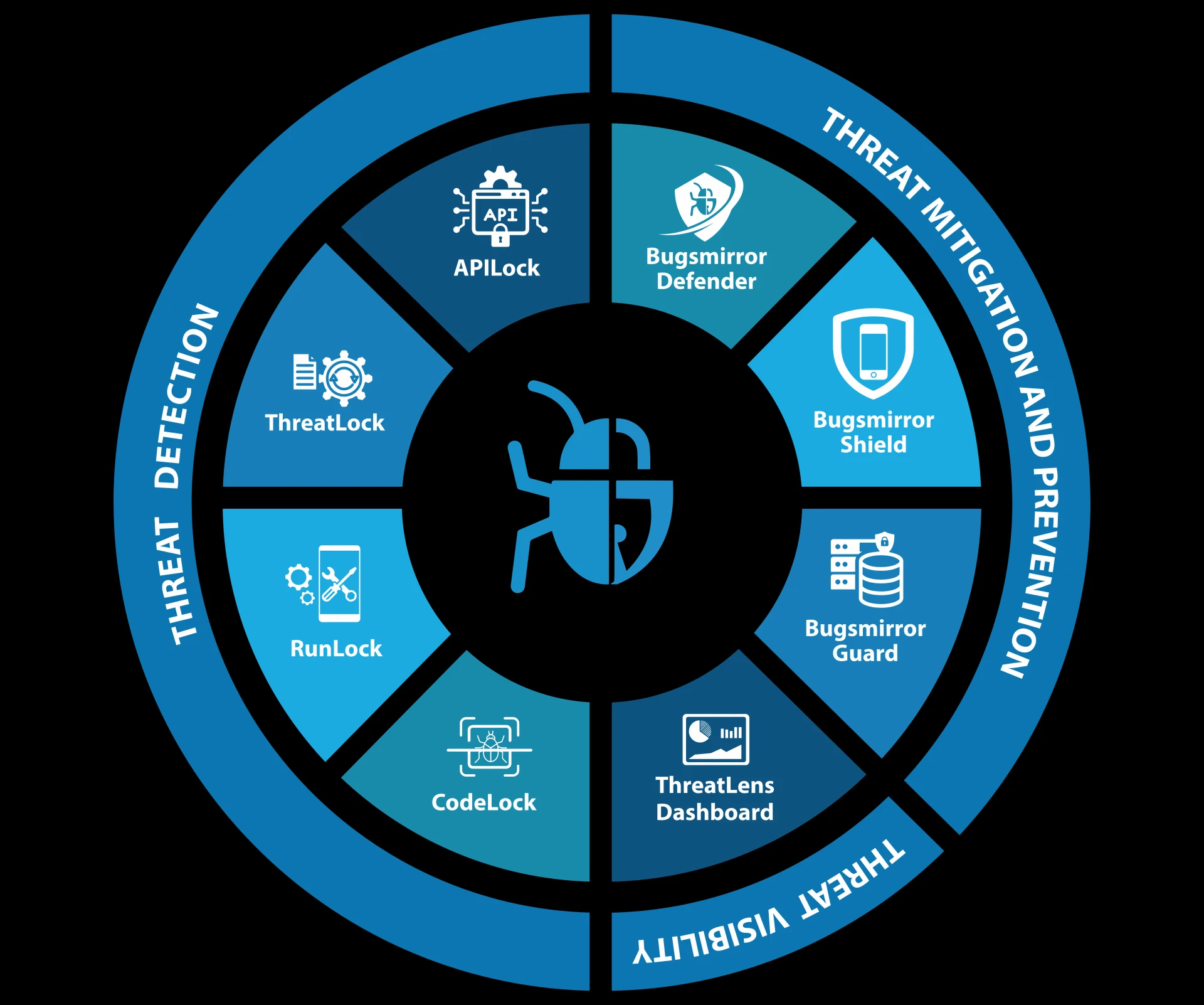
Strengthening business application security is not a one-time task. Mobile apps require ongoing monitoring, updates, and improvements as new risks appear. To address security challenges, companies should opt for mobile app security solutions that offer end-to-end coverage. Bugsmirror MASST (Mobile Application Security Suite & Tools) provides complete security with these application security tools:
- CodeLock: Static Application Security Testing tool
- RunLock: Dynamic Application Security Testing tool
- APILock: API Security Testing tool
- ThreatLock: Red Team Security Testing tool
- Bugsmirror Defender: Runtime Application Self-Protection tool
- Bugsmirror Shield: Anti-reverse engineering and Intellectual Property Protection tool
- Bugsmirror Guard: Sensitive data Protection tool
- ThreatLens: Dashboard for viewing and analyzing security threats detected and prevented by Bugsmirror Defender
Bugsmirror MASST makes business applications secure, reliable, and trustworthy.
Read More: Top 5 Mobile Phones Security Threats - How To Mitigate Them?

















Sign in to leave a comment.