What Is Mobile App Tampering?
Mobile app tampering is an attack in which attackers reverse engineer a mobile application and modify its code or behavior without the developer’s consent. This gives attackers the authority to exploit vulnerabilities in the mobile app, bypass security controls, insert malicious code to perform unauthorized activities, etc.
Tampered mobile apps look similar to legitimate mobile apps, and normal users generally cannot differentiate between them. Using tampered apps is risky, as they can steal sensitive data and even trick users into performing malicious activities.
How Do Attackers Tamper With Mobile Apps?
Attackers tamper with mobile apps using techniques such as:
- App Repackaging – Attackers modify and redistribute apps to mislead users into installing fake versions of those apps.
- Static App Patching – They change an app’s binary or source code to disable security checks, unlock paid features, etc.
- App Spoofing – They develop fake apps that imitate real ones to collect personal, financial, and other details from normal app users.
What Do Attackers Do With Tampered Apps?
Mobile app tampering poses a serious threat to both app users and businesses. Attackers tamper with mobile apps to:
- Bypass authentication or license verification mechanisms
- Harvest sensitive data such as login credentials, financial details, etc.
- Repackage apps and distribute malicious copies under the same brand name
These tampered apps can not only harm end users but also result in significant reputational and financial losses for the businesses that own the original apps. To prevent such incidents, it’s very necessary to implement mobile application security that detects and prevents app tampering.
How To Detect And Prevent App Tampering?
To protect mobile apps against tampering, first monitor an app’s runtime environment to identify tampering attempts such as unauthorized changes in the app’s code. Then prevent tampering using mobile app shielding technologies such as Runtime Application Self-Protection, which integrates within a mobile app to protect it from tampering. Embedding such security features inside an app makes it extremely difficult for attackers to reverse engineer the app or modify its code, ultimately preventing app tampering.
Robust Protection From Mobile App Tampering - Bugsmirror Defender
Bugsmirror Defender provides a comprehensive and multi-layered defense for detecting and preventing mobile app tampering. Defender is a RASP-based security solution that detects and prevents unauthorized modifications to an app’s code and behaviour in real time.
When attackers attempt to tamper with an app, Bugsmirror Defender identifies the change and blocks the tampered version immediately, maintaining app integrity. In addition to app tampering, Defender also protects apps from more than 45 runtime security threats, such as keyloggers, debugging, screen capturing, packet sniffing, unsecured Wi-Fi, emulators, etc.
Developed by the world’s number 1 Bug Hunters for Google, Bugsmirror Defender’s cutting-edge security features ensure that mobile apps protect themselves from runtime security attacks and maintain their reliability and trustworthiness across both Android and iOS platforms.
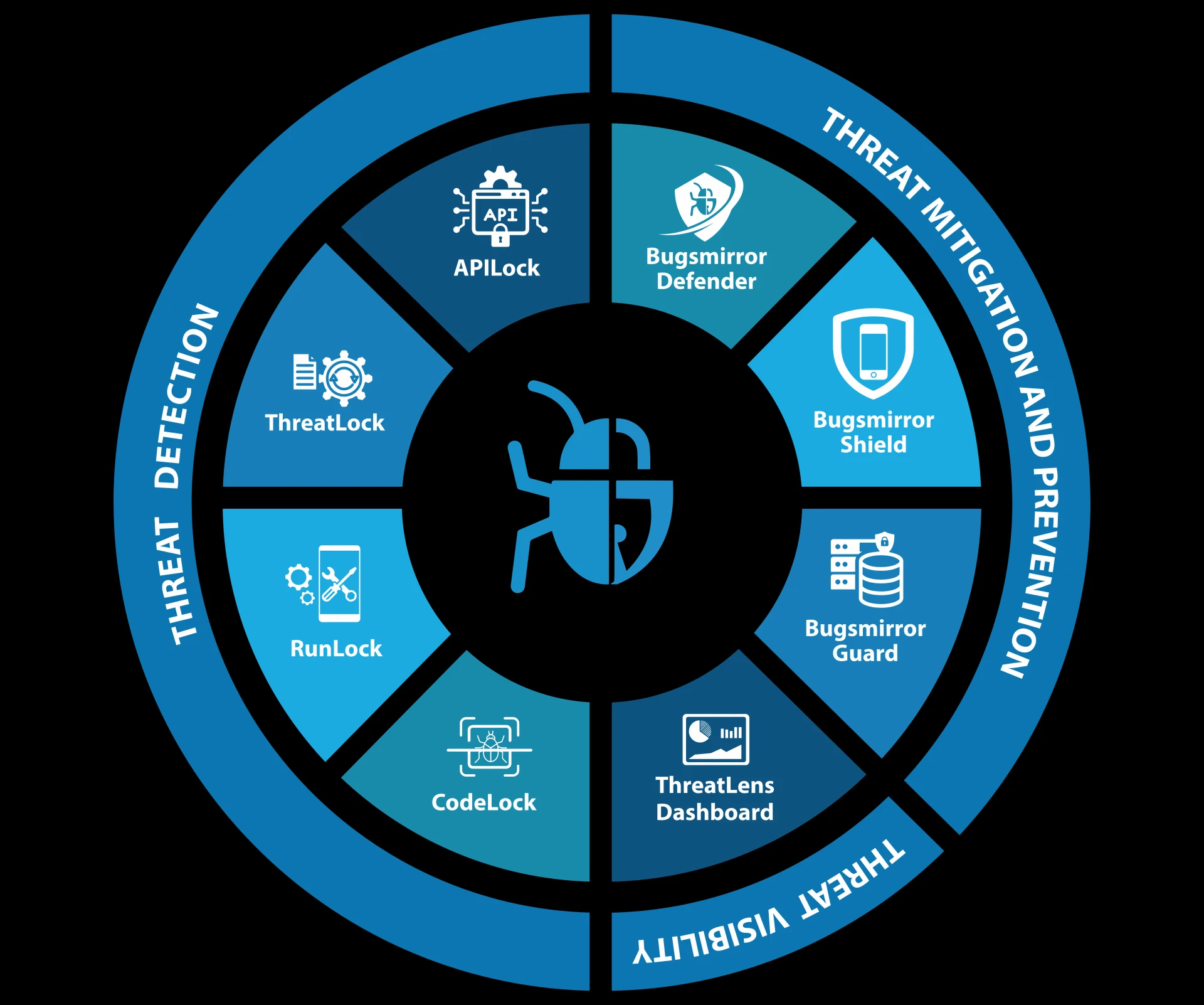
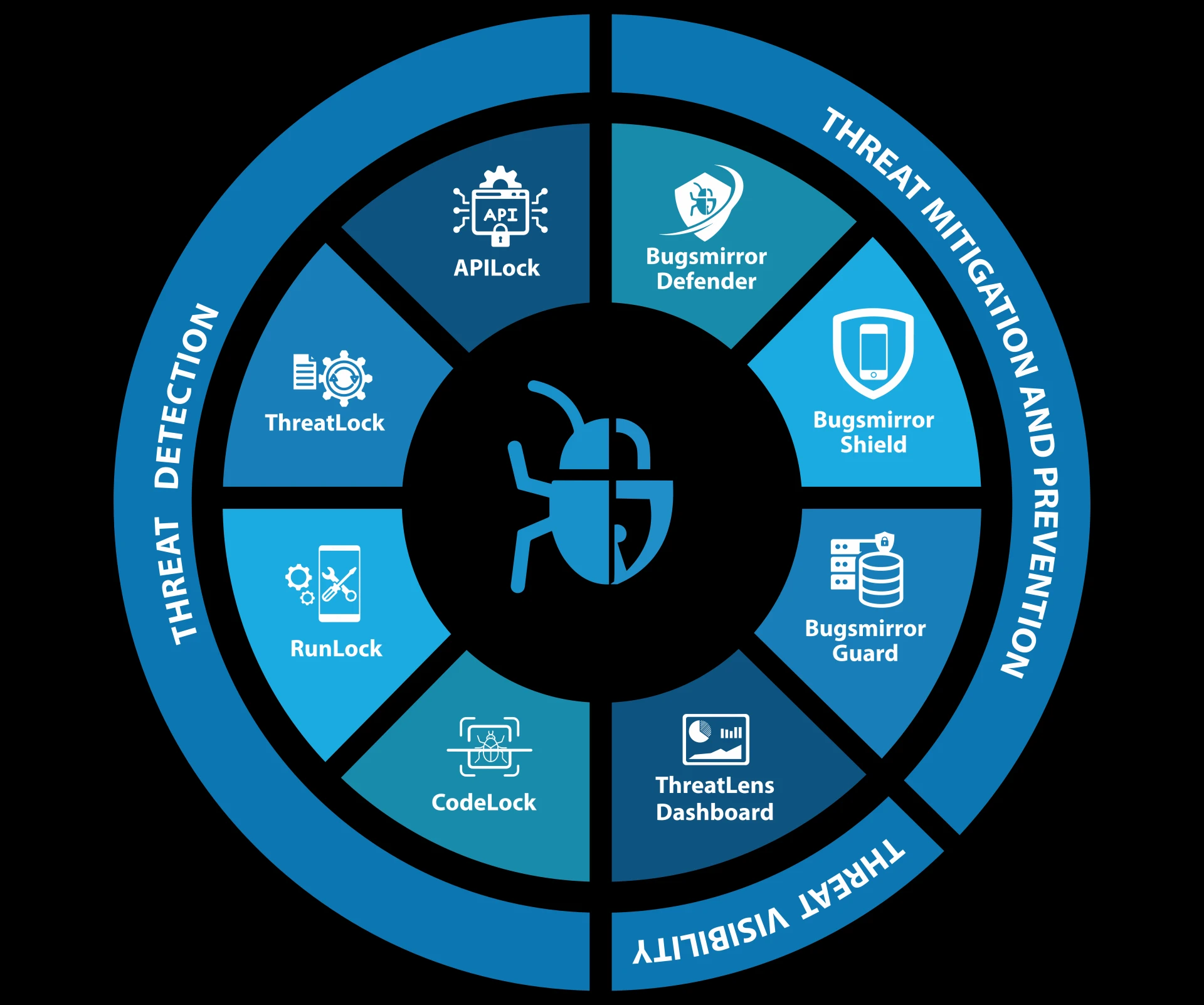
Bugsmirror Defender is a part of Bugsmirror Mobile Application Security Suite and Tools (MASST), an end-to-end security platform for mobile app protection.
Read More: How Mobile App Security Solutions Enhance App Security?



















Sign in to leave a comment.