What Is Rooting?
Rooting can be defined as the technique used to obtain administrative or root privileges on an Android device. Through such privileges, device users are able to access restricted areas, change system files, overcome manufacturer-imposed restrictions, etc. Usually, developers and researchers perform rooting to understand a device in a better way. Generally, users root their devices to have more control over the device and perform activities such as:
- Remove pre-installed applications on the device
- Modify performance settings
- Personalize device features, etc.
How Does Rooting Become A Security Threat?
Rooting a device might be useful, but it comes with significant risks. If an attacker has a rooted device, they can remove its built-in security measures to exploit apps running on the device. It means application-stored data, app functionality, etc., can be compromised. By rooting, attackers gain full administrative control of devices and perform malicious activities such as:
- Modify devices’ Operating Systems and disable built-in protections.
- Access and alter shared file system data
- Interfere with or change the behavior of applications on the devices
- Steal or expose sensitive information stored within devices
Rooting can allow attackers to compromise financial information, medical records, corporate confidential data, etc.
Why Is Root Detection Necessary?
Root detection is an essential security measure that allows mobile apps to determine whether they are being executed on rooted devices. If it’s found that an app is running on a rooted device, steps such as crashing the app or showing a dialog on the device should be taken to prevent it from being compromised.
By incorporating root detection within a mobile app security plan, companies can protect user data, preserve trust, and improve overall security posture.
What Is The Role Of RASP Tools In Root Detection?
Traditional security solutions are unable to protect mobile apps against rooting attacks. Modern Runtime Application Self-Protection tools can protect mobile apps on rooted devices. RASP tools embed security directly inside an app to monitor the app in real time and detect and prevent the app from running on rooted devices.
RASP security can counter rooting attempts even when attackers employ advanced tools to conceal root status—RASP-based Root detection can reveal and thwart such attempts. For healthcare, fintech, and other industries that experience frequent targeting of sensitive user data, preventing apps from running on rooted devices is critical.
Bugsmirror Defender is a robust RASP-based security solution that protects mobile applications on rooted devices. Defender protects mobile apps from running on rooted, malicious, and compromised devices. It protects apps from rooting even when attackers try to run apps with advanced techniques.
Bugsmirror Defender protects mobile apps against rooting, as well as 45 other runtime security threats like debugging, app repackaging, keyloggers, packet sniffing, screen capturing, app spoofing, etc. With real-time threat detection blended with strong threat prevention, Bugsmirror Defender makes mobile apps secure.
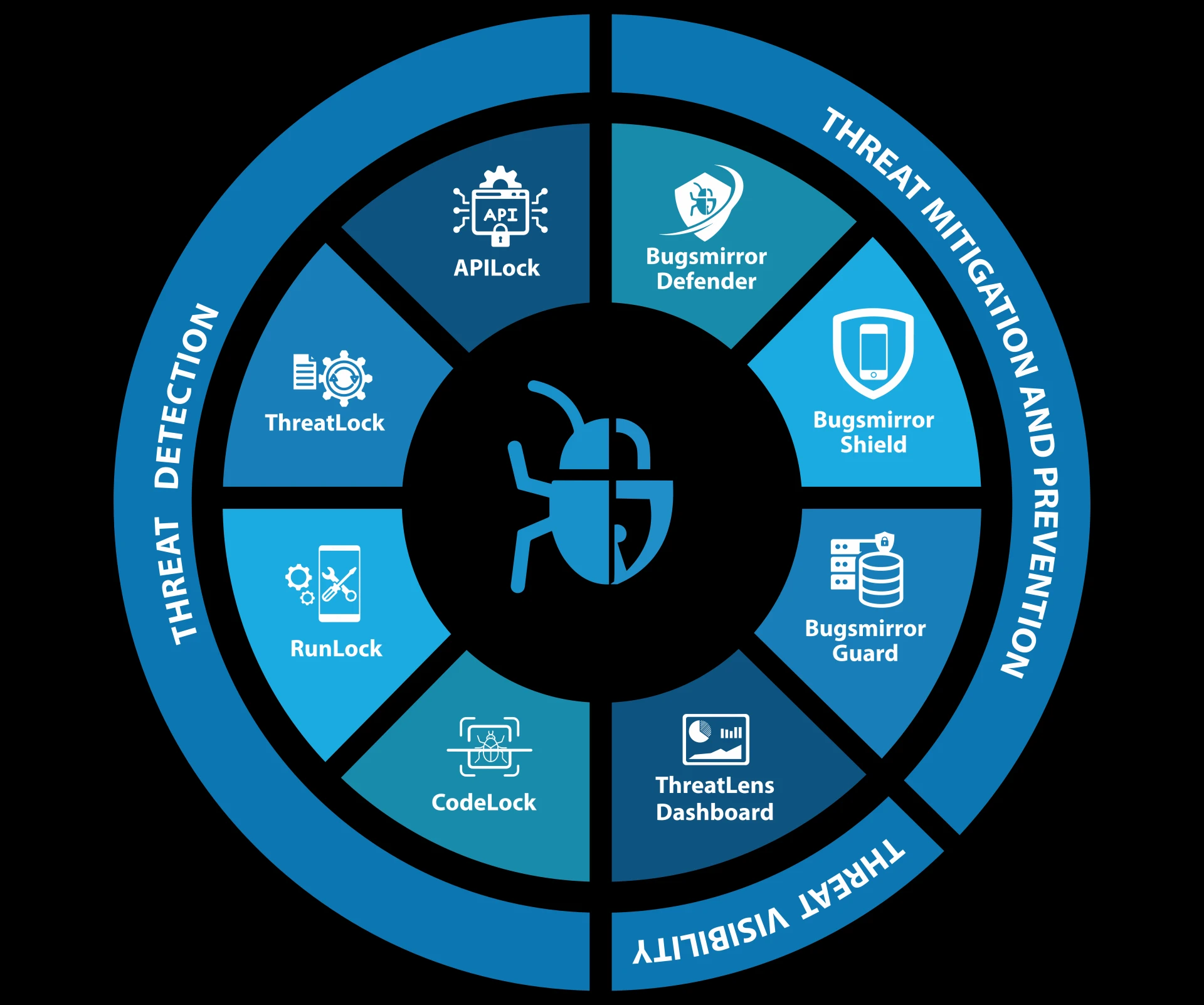
Bugsmirror Defender is a part of Bugsmirror MASST (Mobile Application Security Suite & Tools), a complete security platform that has several security solutions to detect, mitigate, and understand security threats.
Read More: What Is Mobile App Shielding And How It Protects Apps?



















Sign in to leave a comment.