It is well-known that 70% of the global smartphone market is powered by Android, and they are the prime target of attackers. While Android’s security model has improved over the years, rooted devices continue to be a major risk for mobile applications that handle sensitive data, payments, authentication, or business logic. Root detection has become a critical security control for protecting apps at runtime.
What Is Rooting?
Rooting a device means getting root/administrative access to a device by a user or attacker. Once a device is rooted, system-level protections are bypassed, allowing full control over apps, memory, and system processes. Attackers can modify app behaviour, bypass security checks, inject malicious code, or intercept sensitive data such as tokens, API keys, and encryption secrets.
According to mobile security reports, a significant portion of Android devices globally are either rooted or running custom ROMs, and a large portion of mobile fraud originates from these compromised devices. For companies like fintech, gaming, healthcare and enterprise apps, prevention of rooting is necessary to avoid revenue loss and data breaches.
On rooted devices, attackers can:
- Hook or alter an app using frameworks like Frida or Xposed.
- Bypass in-app purchase and payment verification.
- Disable SSL pinning and intercept API traffic.
- Extract hardcoded secrets and sensitive data.
- Tamper with business logic (limits, pricing, scoring).
Once the app is running on a compromised device, traditional security measures such as code obfuscation, static analysis, or client-side validation may not be enough. This is where runtime root detection comes into the picture.
Root detection and how it works?
Root detection is a process that identifies when a device is rooted and prevents the app from running on that rooted device. Modern root detection is not a single check but contains a combination of multiple techniques:
- Checking for root binaries (su, magisk, busybox).
- Detecting modified system files.
- Kernel-level root detection.
- Identifying hooking frameworks and debuggers.
- Detects escalation of unauthorised permissions.
- Maintain app integrity.
Sometimes attackers hide root status using tools like Magisk Hide or patch system calls; thus, one can not rely on basic detection. Root detection must be continuous, multi-layered, and runtime-based, not a one-time check.
Why Root Detection Must Be Runtime-Based
Static checks or one-time validations fail because attackers can activate root tools after the app launches. Runtime detection solves this by constantly watching the device and reacting instantly if something suspicious or unsafe happens.
This approach reduces:
- Fraud attempts.
- Data theft.
- App cloning.
- Reverse engineering.
- Abuse of business logic.
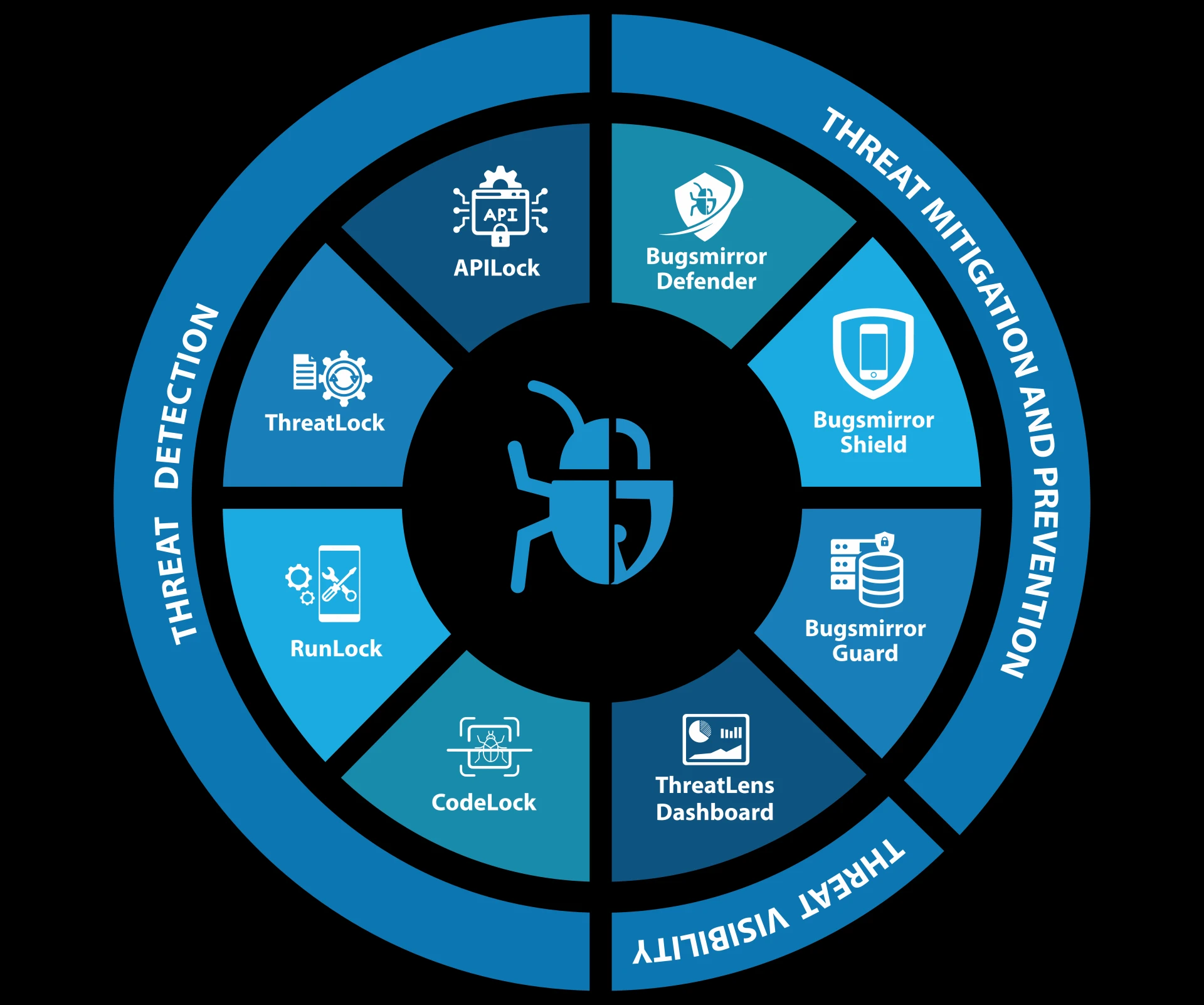
How Bugsmirror Defender Protects Apps from Rooted Devices
Bugsmirror Defender is a runtime application self-protection tool built specifically for mobile apps. It detects rooted environments in real time and prevents apps from running in hostile conditions.
Defender uses multi-layer root detection, checking device integrity, monitoring runtime behaviour, unauthorised escalation attempts, and tampering activities. When a rooted device is detected, the app can automatically block execution, limit sensitive features, or alert backend systems.
Additionally, Bugsmirror Defender provides comprehensive runtime security and protects mobile applications against:
- Runtime code injection.
- App tampering.
- Debugging and hooking.
- API abuse.
- Insecure communication
- Code encryption to avoid reverse engineering.
Bugsmirror Defender keeps apps protected by continuously monitoring device behaviour and updating its protection based on real attack patterns, even when attackers take full control of a device.
Protect your mobile app from rooted devices and runtime attacks. Visit Bugsmirror today!

















Sign in to leave a comment.