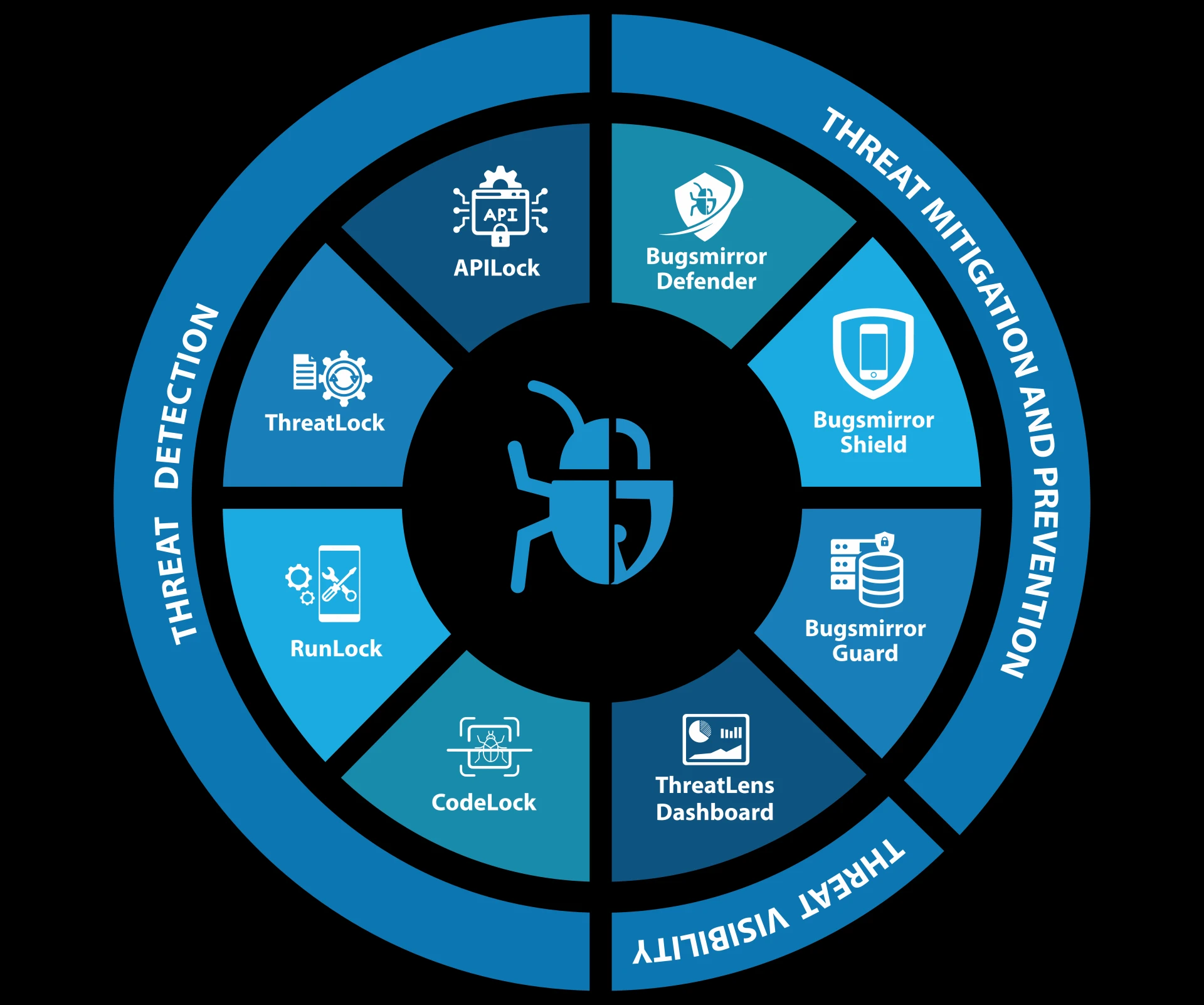
Bugsmirror Defender is a runtime protection solution for mobile applications. It works from inside an app. Once integrated, it continuously checks for malicious behavior while the app is running on a user’s device.
Most modern mobile attacks do not happen statically; they happen at runtime. Attackers use modified devices, debuggers, hooking tools, etc., to manipulate app behavior. Bugsmirror Defender is built to stop these threats using Runtime Application Self-Protection technology. The app protects itself while it is being used.
Bugsmirror Defender relies on RASP application security to monitor runtime behavior. Its runtime monitoring includes:
- Observing how the app executes
- Monitoring how memory is accessed
- Checking how the runtime environment behaves
If abnormal activity is detected, the app can respond instantly. This approach reduces as well as eliminates the attacker’s time window and limits damage.
Unlike traditional protection methods, Defender does not depend on servers or network connectivity. Detection and response work even when the device is offline.
Device and OS Integrity Checks
Bugsmirror Defender continuously performs device and Operating System integrity checks to ensure a mobile app runs only in trusted and secure environments. These checks help identify compromised devices, unsafe configurations, active runtime manipulation attempts, etc., and protect app in following scenarios:
- Bugsmirror Defender detects rooted and jailbroken devices, including deep kernel-level root access.
- If a compromised device is detected, Defender stops app execution or limits app behavior.
- It identifies malicious root apps that allow elevated privileges to attackers.
- Defender flags emulators and virtual machines commonly used for application analysis.
- It checks for unlocked bootloaders and insecure system configurations.
- It also monitors OS settings such as ADB debugging, developer mode, and accessibility permissions.
- Bugsmirror Defender detects and blocks debuggers, hooking frameworks, and Frida tools that attackers use to inspect and modify app behavior.
These protections are essential for RASP application security, where threats must be eliminated during execution, not after damage is done. If a device fails integrity checks, the app can restrict or block access.
Protection From Mobile App Tampering
Bugsmirror Defender protects mobile apps from common tampering techniques, including:
- App Repackaging
- Static App Patching
- App Spoofing
Defender ensures that only authentic app builds are allowed to run. Modified or cloned app versions are blocked. This plays a key role in mobile app shielding, protecting business logic and proprietary information.
Secure Communication
Bugsmirror Defender protects network traffic using SSL pinning. It detects proxies, packet sniffing, and VPN misuse. Sensitive data transmission is protected using encryption and decryption. Data integrity checks ensure values are neither monitored nor altered during execution.
Mobile Privacy
Bugsmirror Defender protects user privacy by blocking screenshots, screen recording, screen sharing, and overlays inside the app. Copy-paste can be restricted.
For fraud prevention, Bugsmirror Defender detects app cloning, second-space usage, keylogging, and tap jacking attacks. Marketplace enforcement checks help prevent sideloaded or redistributed apps from running.
Protection Against 45+ Runtime Security Threats
Bugsmirror Defender protects both Android and iOS mobile apps from 45+ runtime security threats. Defender allows mobile applications to defend themselves automatically in real-world runtime conditions by embedding Runtime Application Self-Protection directly into an app.
Explore how Bugsmirror Defender can strengthen mobile apps from within and protect them against runtime security threats before they impact app users and businesses.
Read More: How To Prevent Mobile App Repackaging?
















Sign in to leave a comment.