Modern businesses depend extensively on mobile applications to run their day to day operations. With the increase in the complexity of apps, attackers have also become more skilled and determined. This makes a comprehensive security assessment extremely essential to find security vulnerabilities before they are exploited.
What Is A Comprehensive Security Assessment?
A comprehensive security assessment is a manual testing of a mobile app infrastructure, APIs, and internal workflows simulating a real attack scenario. This helps organizations understand how a real breach could occur, what assets would be affected, and how quickly attackers could move inside the environment. By uncovering these risks, companies can reduce the chances of data breaches, save money, and keep business running.
For organizations handling sensitive data, especially in regulated industries, such assessments are critical for maintaining business application security. They help validate whether existing controls actually work in a production environment and whether teams are prepared to respond to real incidents.
Long-Term Advantages For Businesses
Regular comprehensive security assessments increase visibility across the whole application lifecycle. They help teams strengthen defenses, refine incident response plans, and improve collaboration between development, operations, and security teams. Businesses gain better control over risks and build stronger trust with customers and partners.
Comprehensive assessments also help businesses meet regulatory requirements by reporting security risks that are being identified and addressed in a structured manner. They provide documented evidence of due diligence, which is required by compliance frameworks. Instead of a one-time activity or incident-driven response, security becomes an ongoing improvement cycle. Weaknesses are regularly identified and defenses are continuously strengthened as threats evolve.
How Is Red Teaming Assessment A Comprehensive Security Assessment?
A Red Teaming security assessment represents a true comprehensive security assessment because it evaluates systems the same way real attackers would. Red Teaming involves skilled professionals who manually attempt to exploit applications, infrastructure, and workflows. This approach helps uncover issues that often go undetected by traditional security testing methods. Such issues may be related to business logic flaws, misconfigurations, weak authentication mechanisms, and insecure process flows.
Red team professionals recreate realistic attack scenarios using a combination of manual techniques and specialized Red Team tools. These simulations can include phishing attempts, privilege escalation, abuse of application functionality, etc. The goal of a Red Teaming assessment is not just to identify technical weaknesses but to understand how multiple gaps can be chained together to create an exploit chain with serious business impact. Businesses gain a clear picture of their real exposure, allowing them to prioritize remediation based on actual risk rather than theoretical severity. This makes Red Teaming an essential component of an effective business application security strategy.
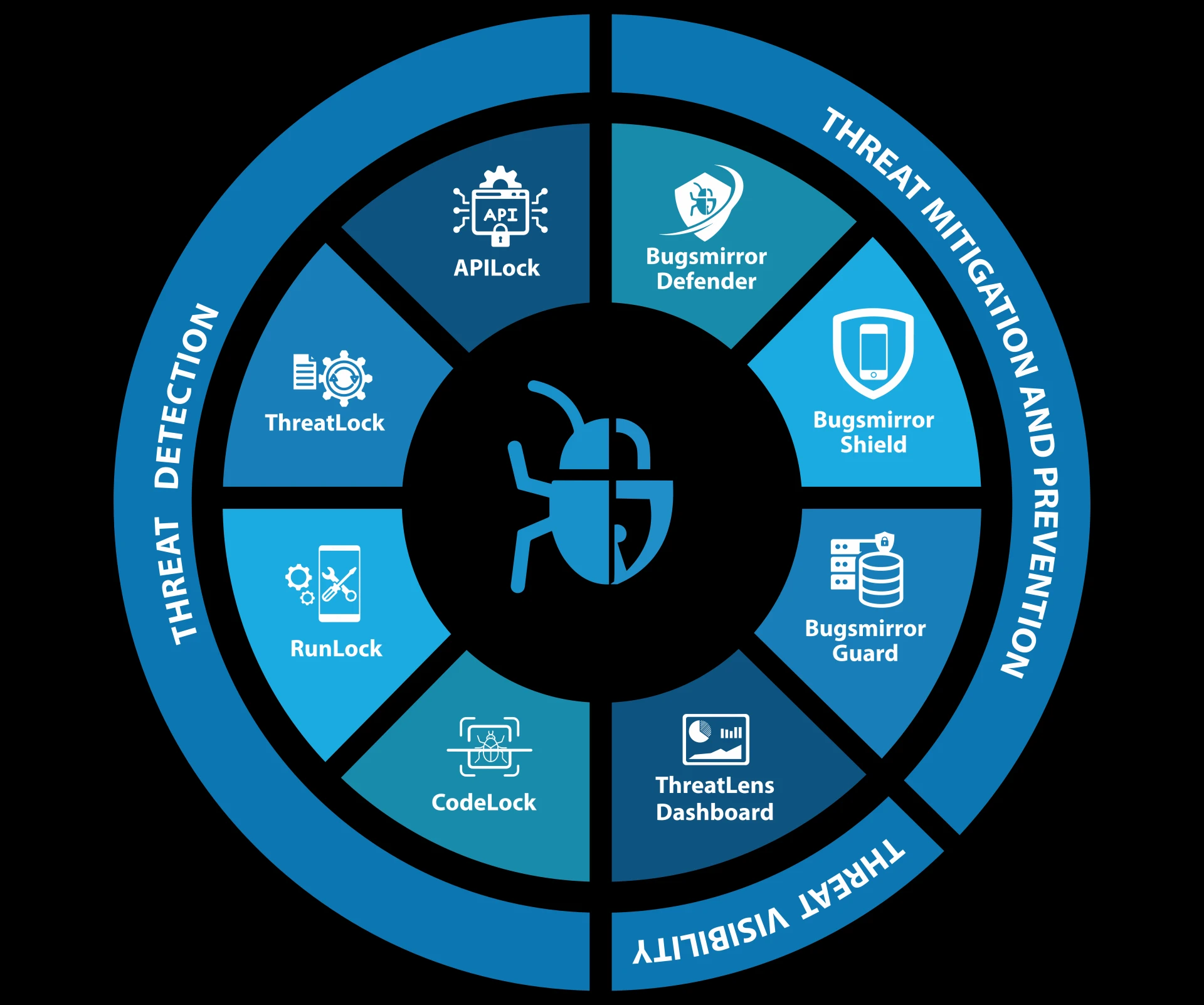
ThreatLock - Deep Red Teaming Security Assessment
Bugsmirror ThreatLock is an expert-led manual Red Teaming security assessment that simulates real attacker behaviour to uncover high-risk vulnerabilities. By combining skilled professionals, advanced Red Team tools, and structured testing methods, it delivers actionable insights and clear reports with PoCs (Proof-of-Concepts) to help businesses strengthen mobile app defenses.
Read More: What Is Mobile App Shielding? Why Every Fintech App Needs It?














Sign in to leave a comment.