In an increasingly connected world, where data breaches and cyberattacks cost businesses trillions globally, cybersecurity is no longer a back-office concern—it's a boardroom priority. But the cyber threat landscape has evolved dramatically, and traditional firewalls and manual monitoring no longer cut it.
Enter artificial intelligence.
Today’s frontline defense against sophisticated cyber threats isn’t a human analyst alone—it’s a dynamic combination of algorithms, behavioral models, and self-learning systems, all created by the hands of a skilled artificial intelligence developer.
Why Cybersecurity Needs AI in 2025
Cyberattacks are no longer brute force—they’re subtle, silent, and increasingly automated. From polymorphic malware to zero-day exploits and deepfake phishing, attackers are now leveraging AI to craft smarter intrusions.
To defend against AI-powered threats, organizations need AI-powered defenses. This is why cybersecurity teams are rapidly hiring artificial intelligence developer talent who can build predictive, adaptive, and autonomous defense systems.
AI Use Cases in Modern Cybersecurity
Let’s break down the top applications of AI in cybersecurity today:
1. Threat Detection and Prevention
Traditional systems rely on known signatures. But AI can detect:
- Anomalous behaviors
- Zero-day exploits
- Insider threats
- New attack patterns
By using unsupervised learning and clustering, AI models flag deviations in real-time—far faster than any human could.
2. Phishing Detection
Phishing scams are more convincing than ever, often powered by generative AI. Developers use natural language processing (NLP) models to:
- Analyze email content
- Flag suspicious language patterns
- Identify fake login pages and URLs
AI can catch subtle cues in tone, domain spoofing, and link redirection—signals that even experienced users might miss.
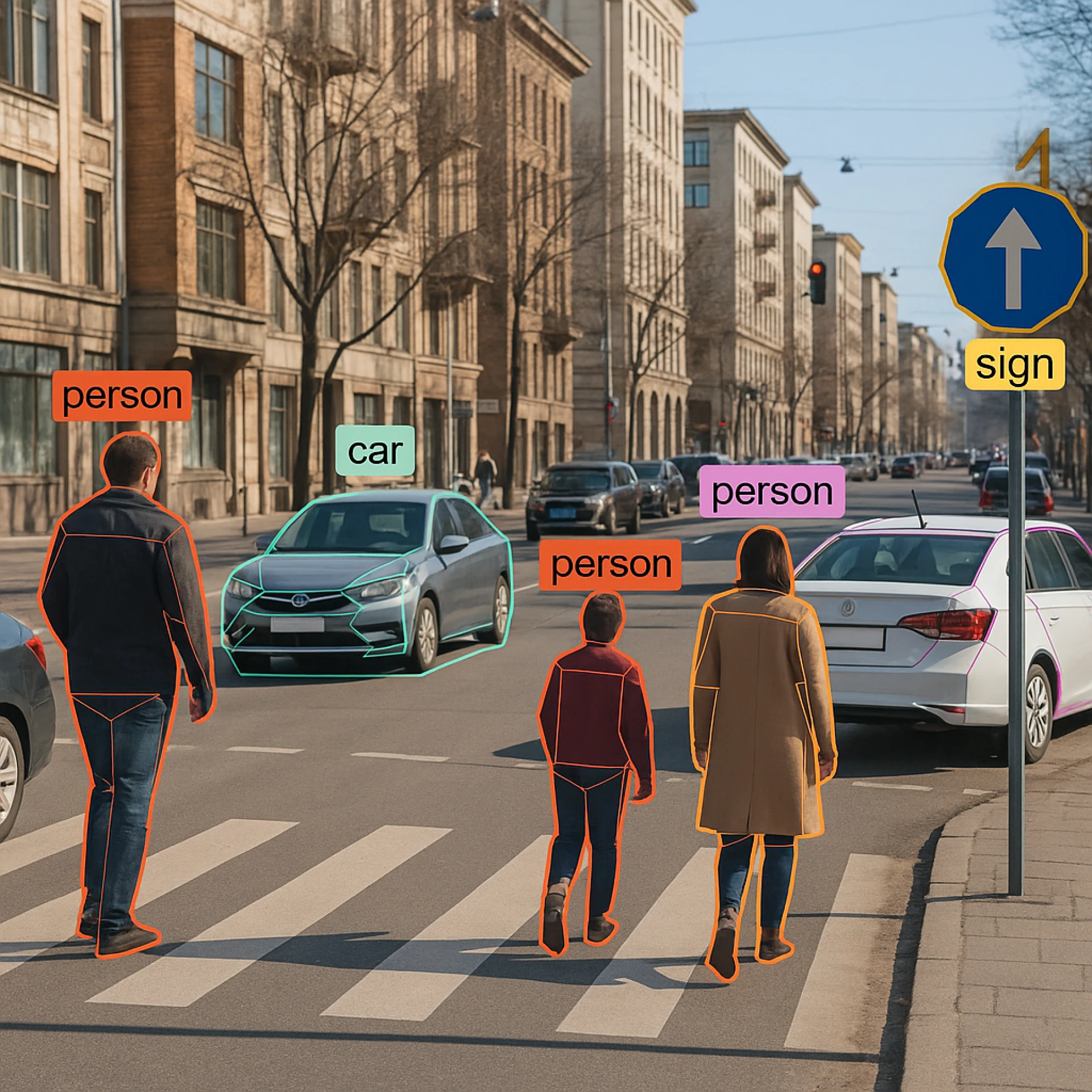
3. User and Entity Behavior Analytics (UEBA)
AI models learn how users normally interact with systems. Any deviation—like logging in from an unusual location or downloading large volumes of data—is flagged for review.
A artificial intelligence developer uses time-series modeling, clustering algorithms, and autoencoders to build these behavior profiles.
4. Security Information and Event Management (SIEM) Optimization
SIEM platforms are used to collect and analyze security data. With AI, these platforms become smarter:
- Prioritize critical alerts
- Eliminate false positives
- Correlate data across sources
This allows security teams to focus on real threats instead of chasing noise.
5. Malware and Ransomware Detection
AI can reverse-engineer suspicious files and detect previously unknown malware strains by:
- Analyzing file behaviors in sandbox environments
- Using convolutional neural networks (CNNs) to detect image-based payloads
- Classifying malware families using bytecode
The key here is speed and adaptability—exactly what AI excels at.
Skills an AI Developer Needs in Cybersecurity
To be effective in this domain, a artificial intelligence developer must blend technical skill with security acumen:
Skill Area Required Knowledge Machine Learning Classification, clustering, anomaly detection Cybersecurity Basics Firewalls, endpoint security, network protocols NLP Detecting phishing, fake text, social engineering content Time-Series Analysis Analyzing system logs and login patterns Cloud Security Tools AWS Shield, Azure Defender, Google Chronicle
Many top developers in this field also pursue certifications like Certified Ethical Hacker (CEH) or CompTIA Security+ to understand the attacker's mindset.
Tools Used by AI Developers in Cybersecurity
Tool/Framework Purpose Scikit-learn, XG Boost Traditional ML models for classification Tensor Flow, Py Torch Deep learning for complex threat models Snort, Suricata Integrate AI with intrusion detection systems Elasticsearch & Kibana Analyze log data at scale with ML-based filters Apache Kafka Stream real-time security events into AI models
AI developers must integrate these tools into the company’s existing security stack without disrupting performance.
Why the Demand Is Skyrocketing
Cybersecurity Ventures predicts that by 2025, cybercrime will cost the world $10.5 trillion annually. This makes cybersecurity the fastest-growing segment in tech hiring—and AI developers are at the center of that growth.
As threats become automated and personalized, AI becomes the only viable line of defense at scale.
Enterprises, governments, and even startups now compete for top-tier artificial intelligence developer talent that can design AI-powered security tools, autonomous monitoring systems, and adaptive firewalls.
AI in Action: Real-World Examples
🔹 Darktrace
Uses AI to monitor network traffic and detect anomalies across IT, OT, and cloud systems. Their models stop attacks in real time—even novel ones.
🔹 CrowdStrike
Integrates AI for endpoint protection and threat intelligence. Known for preventing major ransomware attacks on enterprises.
🔹 IBM QRadar + Watson
Combines SIEM with NLP to understand threats and recommend remediation steps autonomously.
Risks and Ethics of AI in Cybersecurity
With great power comes new concerns. Developers must build AI that avoids:
- False positives: Blocking legitimate activity
- Bias in training data: Missing threats from underrepresented behaviors
- Overdependence: Relying entirely on machines for critical decisions
Explainability, transparency, and continuous retraining are key pillars of ethical cybersecurity AI.
Career Path for AI Developers in Cybersecurity
For those looking to enter the field, here’s a typical progression:
- Start with ML Basics: Python, scikit-learn, NLP
- Learn Cybersecurity Foundations: Networking, authentication, common attacks
- Contribute to Open Source: Projects like MITRE ATT&CK or OSSEC
- Specialize in Real-Time Systems: Kafka, Spark, edge AI
- Build a Portfolio: Create models that detect anomalies or simulate phishing defense
The intersection of cybersecurity and AI is one of the most rewarding—and well-compensated—careers in tech.
Conclusion: Code That Protects the Digital World
In the new era of digital warfare, it’s not just hackers versus firewalls anymore—it’s AI versus AI. The question is: which side of the intelligence are you on?
Organizations that want to protect their customers, data, and reputations must move beyond traditional defenses. They must embed intelligence into their security stack—and that starts by hiring the right talent.
Whether you're a SaaS company, a financial institution, or a government agency, hiring an artificial intelligence developer is no longer a luxury—it’s a necessity for survival.












Sign in to leave a comment.