In today’s fast-evolving digital landscape, organizations face increasing cyber threats that can disrupt operations, compromise sensitive data, and damage brand reputation. Developing cyber hygiene is no longer optional—it is a critical strategy that enables businesses to prepare for, respond to, and recover from cyber incidents effectively. By combining proactive security measures with adaptive recovery plans, companies can ensure continuity even in the face of sophisticated attacks.
What Is Icyber Resilience?
Icyber resilience refers to an organization’s ability to anticipate, withstand, recover from, and adapt to cyber threats. Unlike traditional cybersecurity, which focuses mainly on prevention, icyber resilience emphasizes a holistic approach. It includes detection, response, recovery, and continuous improvement.
This approach ensures that even if an attack bypasses defenses, the organization can minimize damage and resume normal operations quickly. Businesses that invest in icyber resilience gain a competitive edge by maintaining trust and reliability.
Why Icyber Resilience Matters
Cyberattacks such as ransomware, phishing, and data breaches are becoming more frequent and complex. A single incident can lead to financial loss, regulatory penalties, and long-term reputational harm. Icyber resilience helps organizations:
- Reduce downtime and operational disruptions
- Protect critical data and IT assets
- Maintain customer trust and compliance
- Improve incident response efficiency
By focusing on resilience, companies shift from a reactive stance to a proactive and adaptive security posture.
Key Components of an Effective Icyber Resilience Strategy
To build strong icyber resilience, organizations must implement several core components:
1. Risk Assessment and Asset Visibility
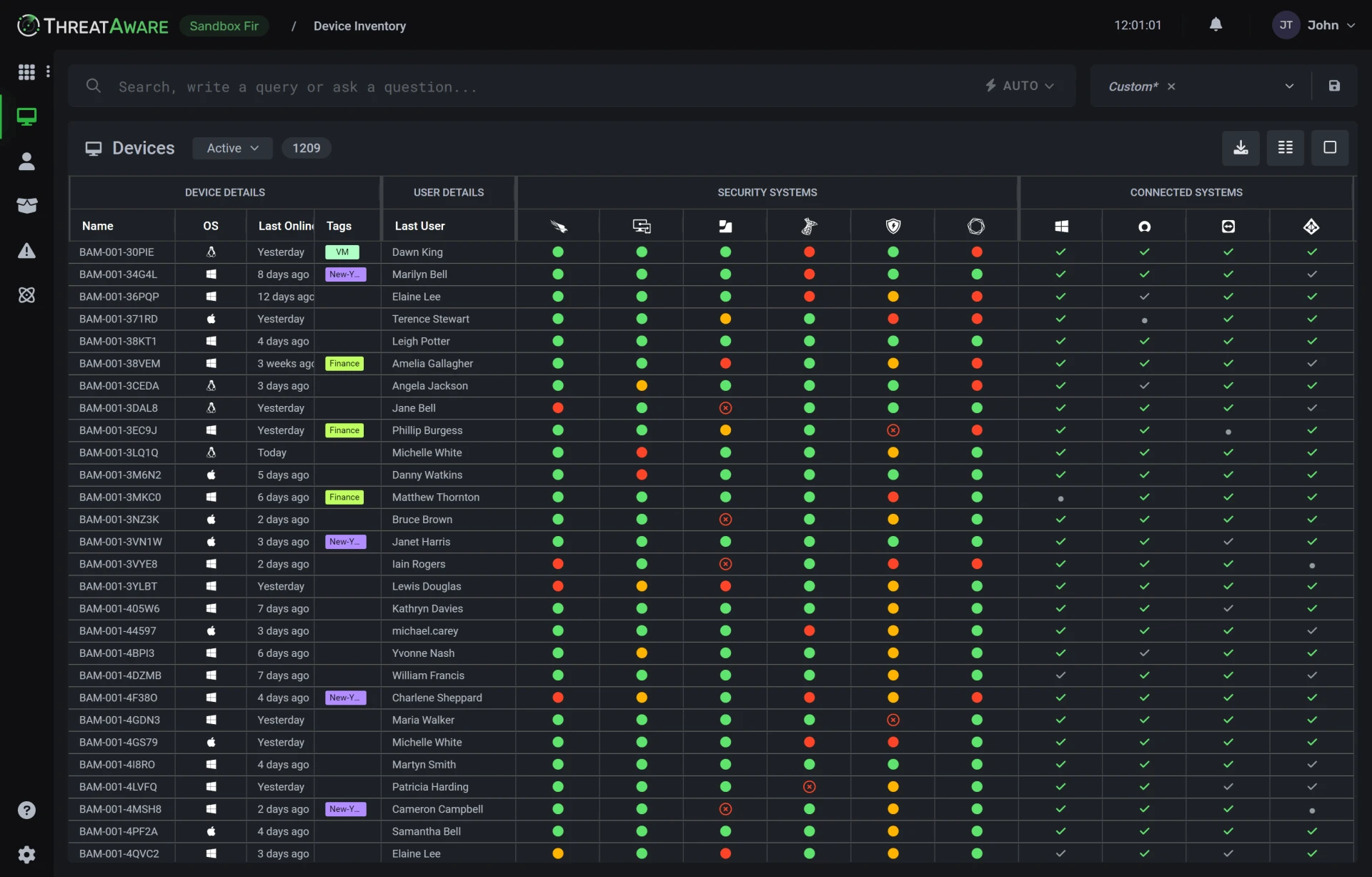
Understanding what needs protection is the first step. Organizations should identify critical assets, assess vulnerabilities, and prioritize risks. A centralized platform like ThreatAware helps businesses gain full visibility into their IT environment.
2. Continuous Monitoring and Threat Detection
Real-time monitoring enables early detection of suspicious activities. Advanced tools can analyze patterns and alert teams before threats escalate into serious incidents.
3. Incident Response Planning
A well-defined response plan ensures quick action during a cyber incident. Teams should be trained regularly to handle breaches efficiently and minimize damage.
4. Data Backup and Recovery
Reliable backup systems are essential for restoring operations after an attack. Regular testing of recovery processes ensures data integrity and availability.
5. Employee Awareness and Training
Human error remains one of the leading causes of cyber incidents. Regular training programs help employees recognize threats such as phishing and social engineering attacks.
How Centralized Platforms Improve Icyber Resilience
Managing cybersecurity across multiple systems can be challenging. Centralized platforms simplify this process by providing a unified view of assets, risks, and vulnerabilities. With automated alerts and streamlined workflows, businesses can respond faster and more effectively.
Solutions like ThreatAware allow organizations to monitor their entire IT infrastructure from a single dashboard. This improves decision-making, enhances visibility, and strengthens overall resilience.
Best Practices for Strengthening Icyber Resilience
To maximize the effectiveness of your strategy, consider the following best practices:
- Regularly update and patch software systems
- Implement multi-factor authentication (MFA)
- Conduct frequent security audits and penetration testing
- Develop a business continuity plan
- Use encryption to protect sensitive data
Consistency and continuous improvement are key to maintaining strong icyber resilience.
Conclusion
Icyber resilience is essential for businesses aiming to thrive in a digital-first world. By adopting a proactive approach that combines prevention, detection, and recovery, organizations can safeguard their operations and maintain customer trust. Leveraging advanced tools and platforms like ThreatAware further enhances visibility and control, making it easier to manage complex IT environments. Investing in icyber resilience today ensures a secure and sustainable future for your business.

















Sign in to leave a comment.