In today\'s digitally driven world, where data breaches and cyber threats loom large, ensuring the security and integrity of sensitive information is paramount for organizations of all sizes. Among the numerous strategies employed to safeguard data, user access review stands out as a fundamental practice. This comprehensive guide aims to delve into the intricacies of user access review, its importance, implementation strategies, best practices, and its role in enhancing security and compliance within organizations.
Understanding User Access Review
User access review, also known as entitlement review or access certification, is the process of regularly evaluating and validating the access rights of users within an organization\'s systems, applications, and resources. The primary goal is to ensure that users have the appropriate level of access required to perform their job functions effectively while mitigating the risk of unauthorized access.
Importance of User Access Review
Security Enhancement: By regularly reviewing user access rights, organizations can identify and revoke unnecessary privileges, reducing the potential attack surface for malicious actors.
Compliance Adherence: User access review plays a crucial role in meeting regulatory requirements such as GDPR, HIPAA, SOX, and PCI DSS, which mandate the protection of sensitive data and the implementation of access controls.
Risk Mitigation: Proactively reviewing and managing user access helps mitigate the risk of insider threats, data breaches, and unauthorized access to critical systems and information.
Implementation Strategies
Establish Clear Policies and Procedures: Develop documented policies and procedures outlining the user access review process, including roles and responsibilities, frequency of reviews, and criteria for access evaluation.
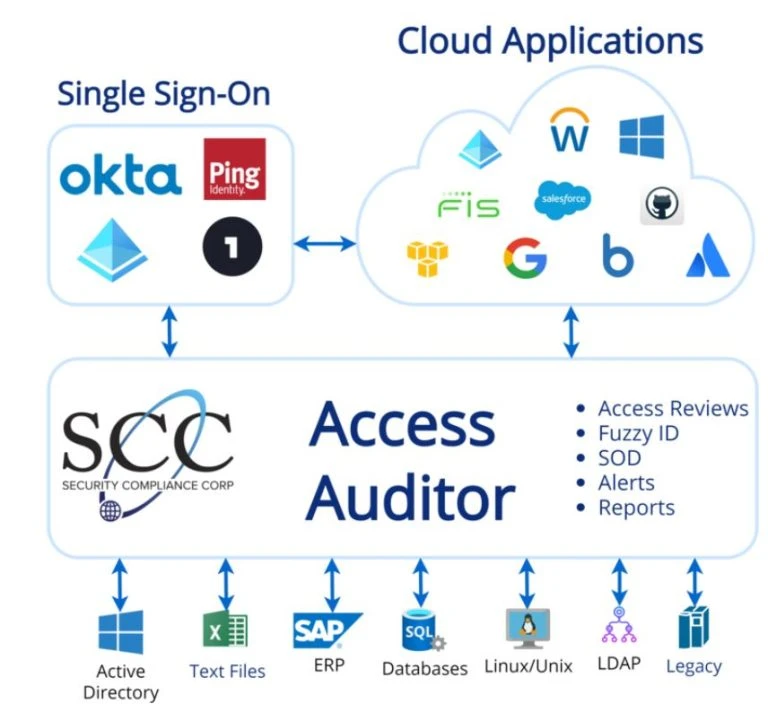
Automate Where Possible: Leverage automated identity and access management (IAM) solutions to streamline the user access review process, minimize manual effort, and ensure consistency and accuracy.
Define Access Roles and Permissions: Classify users into roles based on their job functions and assign appropriate access permissions accordingly. Regularly review and update role definitions to align with organizational changes.
Regular Auditing and Reporting: Conduct periodic audits to assess the effectiveness of the user access review process. Generate comprehensive reports detailing access rights, review activities, and any discrepancies or violations discovered.
Best Practices for User Access Review
Regular Reviews: Establish a consistent schedule for user access reviews, whether quarterly, semi-annually, or annually, to ensure timely identification and resolution of access issues.
Segregation of Duties (SoD): Implement segregation of duties policies to prevent conflicts of interest and enforce checks and balances within the organization.
Multi-Factor Authentication (MFA): Enhance access security by implementing MFA for critical systems and applications, adding an extra layer of authentication beyond passwords.
Employee Training and Awareness: Educate employees on the importance of access control, data privacy, and security best practices to foster a culture of cybersecurity awareness within the organization.
Continuous Monitoring: Implement continuous monitoring solutions to detect and respond to unauthorized access attempts or suspicious behavior in real-time.
Role in Security and Compliance
User access review serves as a linchpin in an organization\'s security and compliance framework by:
Ensuring Least Privilege: Limiting user access to only the necessary resources and data required to perform their job functions reduces the risk of privilege misuse or abuse.
Facilitating Compliance Audits: By maintaining accurate records of access reviews and permissions, organizations can demonstrate compliance with regulatory requirements during audits and assessments.
Detecting Anomalies and Suspicious Activity: Regularly reviewing user access enables organizations to identify anomalous behavior or unauthorized access attempts promptly, allowing for timely investigation and response.
Conclusion
In conclusion, user access review is a critical component of any robust cybersecurity strategy, playing a pivotal role in enhancing security posture, mitigating risks, and ensuring compliance with regulatory mandates. By implementing effective user access review processes, organizations can proactively manage access permissions, safeguard sensitive data, and fortify their defenses against evolving cyber threats. Embracing automation, establishing clear policies, and fostering a culture of security awareness are key to achieving success in user access management and maintaining the trust of stakeholders in an increasingly interconnected digital landscape.














Sign in to leave a comment.