Cybersecurity in 2026 demands more than isolated tools and reactive workflows. Organizations are facing larger cybersecurity threats (89% increase due to AI enablement), rising telemetry volumes, and increased pressure to improve response without expanding headcount or tool spend. Despite the growing volume of threats, over 97% of organizations hit by security threats were found to be operating without proper access controls, highlighting a critical failure in modern identity architecture.
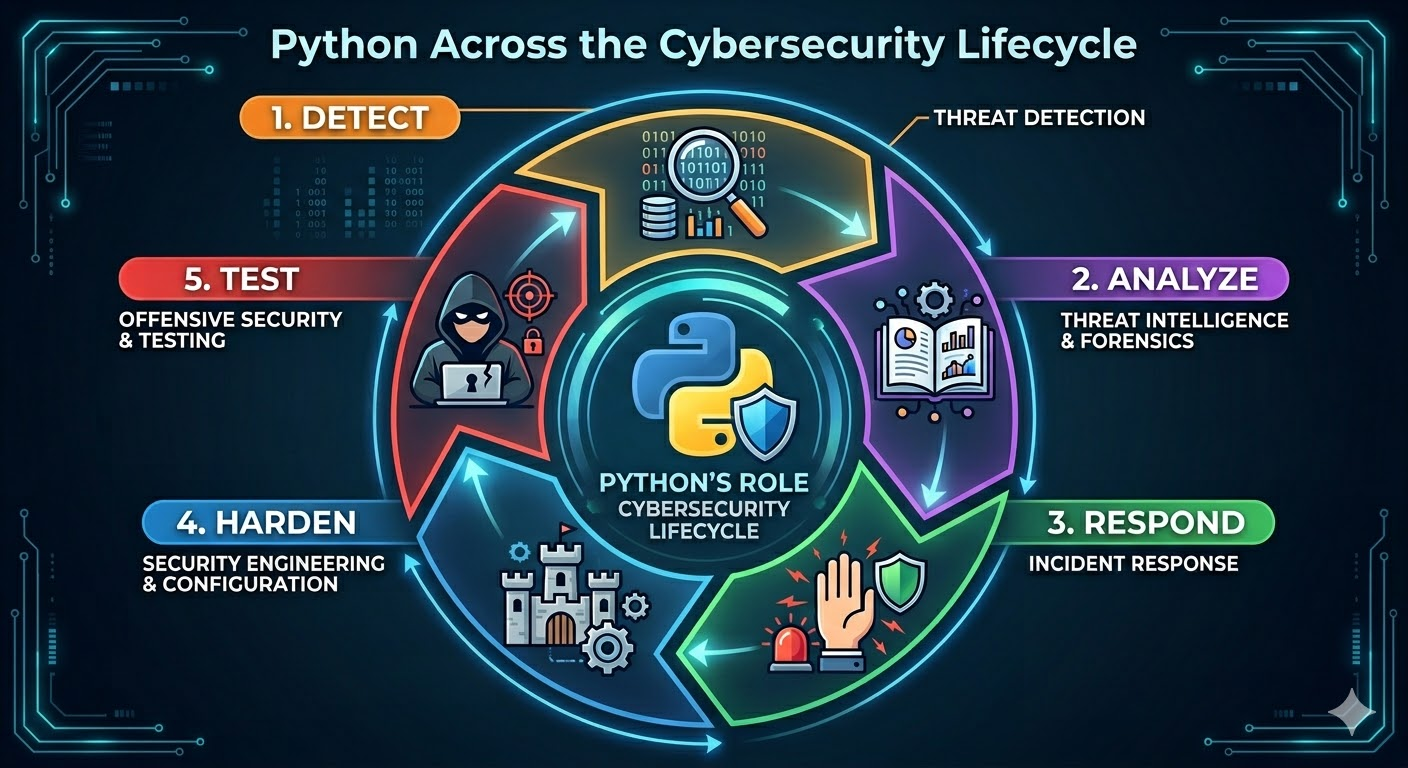
In that environment, Python stands out as a practical engineering language for building security systems that are automatable and easier to integrate across modern environments. Its value is not limited to one area of security. Python supports automation, data handling, API orchestration, machine learning, forensic workflows, and offensive security testing, making it useful across the entire cybersecurity lifecycle.
But the choice of language alone is not an advantage. The real value comes from how effectively it is applied to security operations. That is why choosing the right Python developer matters just as much as choosing the right security architecture.
Why Choose Python for Cybersecurity Solutions in 2026?
We have listed all the high-impact reasons that make Python a preferred choice for cybersecurity experts in 2026.
Python Security Automation
In 2026, manual triage is being rapidly displaced, as the window of opportunity to contain an attack has shrunk from hours to seconds, as AI-driven exploits now execute at machine speed. Python scripting for security allows cybersecurity teams to build robust automation pipelines that handle high-volume tasks. By codifying log normalization, firewall rule audits, and scan orchestration, teams can eliminate the human bottleneck, allowing analysts to focus on high-context threat reasoning. This approach transforms the SOC (Security Operations Center) operations from a linear cost center into a scalable, automated engine.
Key Python libraries for cybersecurity are:
- Paramiko and Netmiko: For seamless SSH automation and multi-vendor network device management.
- Scapy: The industry standard for low-level packet manipulation and custom protocol analysis.
- Celery: A powerful task queue used to distribute and schedule resource-intensive security workflows.
- Requests/Httpx: To interface with various security tool APIs for automated data enrichment.
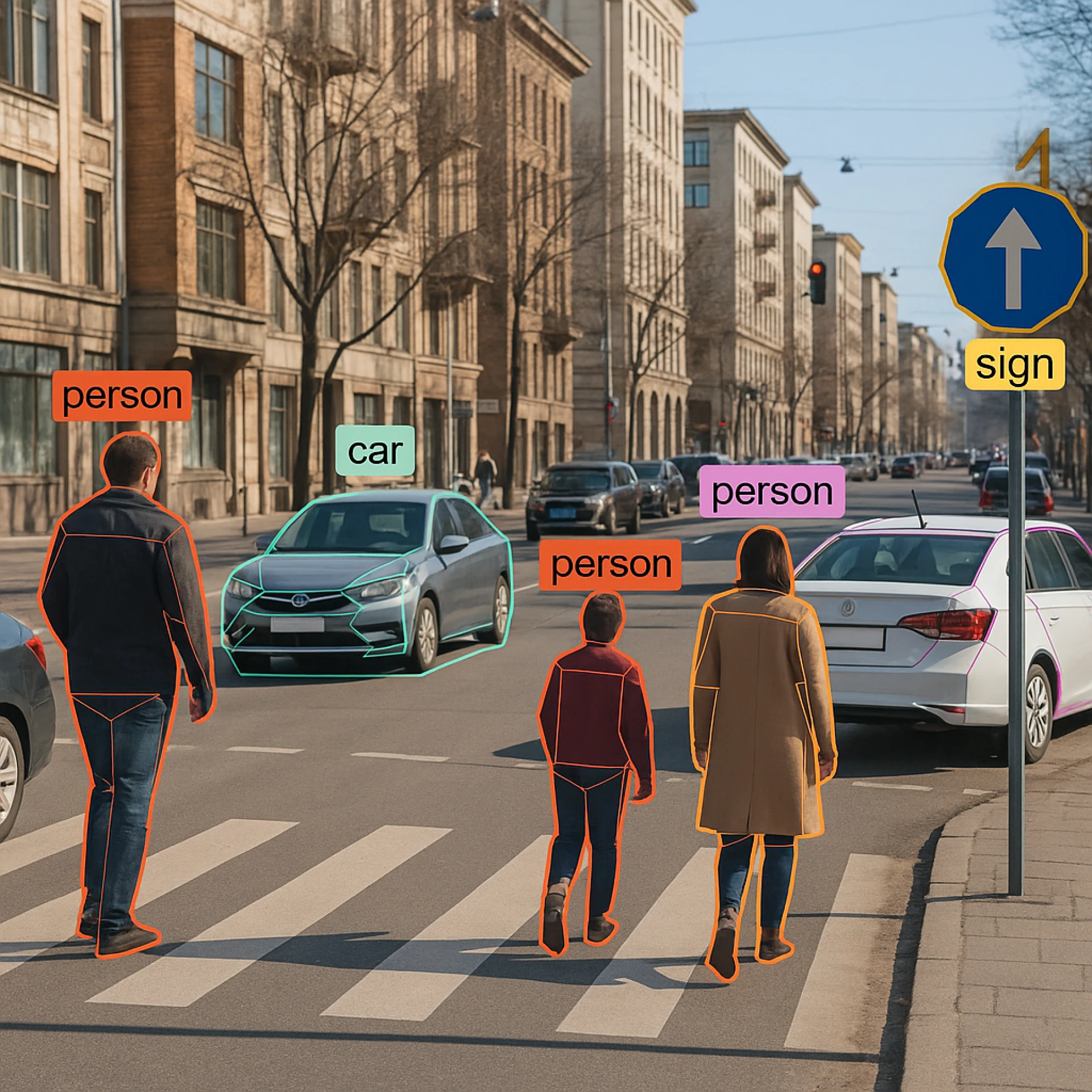
AI/ML-Powered Threat Detection
Python is the de facto language of applied machine learning, enabling teams to move beyond black-box vendor logic. Organizations use Python to develop proprietary models that analyze internal traffic patterns, identify stealthy lateral movement, and classify malware. These models are trained on behavioral telemetry such as network flow anomalies, process tree deviations, and authentication patterns, rather than static signatures, reducing the window of exposure during Zero-Day outbreaks. These models can adapt to new threats independently of a vendor's patch or release cycle.
A growing area within this space is Explainable AI (XAI) for security. Tools like SHAP (SHapley Additive exPlanations) and LIME (Local Interpretable Model-agnostic Explanations) are being adopted to make complex AI-driven security decisions more interpretable for human analysts and compliance teams. When a model flags an alert or blocks a request, XAI enables teams to understand the why, under emerging regulatory frameworks that demand auditability of automated decisions.
Key Python tools for AI/LM threat detection:
- PyTorch and TensorFlow: For building and training deep learning models for malware and anomaly detection.
- Scikit-learn: For implementing classical machine learning algorithms like random forests for phishing detection.
- LangChain or LangGraph: For building Agentic workflows where AI agents reason through security alerts.
- Hugging Face Transformers: To leverage and fine-tune LLMs for log summarization and incident context.
Zero-Trust Architecture Implementation
2026 is widely being called the year of zero-trust security, a model where nothing inside or outside the network perimeter is trusted by default, and every access request must be continuously verified regardless of origin. Python is increasingly used to implement zero-trust enforcement logic, including token validation, mutual TLS (mTLS) handshakes, continuous session verification, and policy-as-code frameworks that enforce least-privilege access dynamically.
Its ability to interface directly with identity providers, certificate authorities, and cloud IAM systems makes it well-suited for building the middleware that enforces zero-trust principles across hybrid and multi-cloud environments.
Key Python tools for zero-trust implementation:
- PyJWT: For validating and issuing JSON Web Tokens in token-based access control flows.
- Cryptography.io: For implementing mTLS certificate generation, validation, and rotation pipelines.
- Authlib: A comprehensive OAuth 2.0 and OIDC library for building standards-compliant authorization and verification flows.
- FastAPI + middleware: To enforce policy-as-code and build APIs based on standard Python type hints at the API gateway layer, dynamically validating identity claims on every request.
Reduced Vendor Dependency and Total Cost of Ownership (TCO)
Commercial platforms often charge based on volume, which penalizes growth as your telemetry scales. Python can reduce this vendor dependency in specific layers of the security stack by enabling organizations to build internal enrichment services, telemetry pipelines, integrations, and response tooling tailored to their environment.
This results in lower costs in some workflows and reduces lock-in, but it does not eliminate the need for commercial controls such as EDR (Endpoint Detection and Response), SIEM (Security Information and Event Management), IAM (Identity and Access Management), or managed security services. In practice, there is a tradeoff between license spend and internal engineering overhead.
Some of the key tools are:
- Motor (for MongoDB): An asynchronous Python driver for handling high-volume security event storage without blocking execution.
- aiokafka: Asynchronous Python client library for building high-throughput, distributed messaging pipelines to route telemetry between tools.
- FastAPI: To create high-performance internal security microservices and API gateways.
Threat Intelligence and Data Analysis
The volume of telemetry is a liability unless it is processed with an engineered approach. Python, in that case, provides the foundation for building end-to-end intelligence pipelines. Cybersecurity teams leverage Python to orchestrate threat intelligence by ingesting structured data from MISP (via the PyMISP library) and across STIX/TAXII ecosystems.
In this architecture, STIX provides the standardized language for describing threat context, while TAXII serves as the secure transport protocol for exchanging that intelligence. This allows Python-driven models to identify Indicators of Compromise (IOCs) through statistical analysis and pattern matching.
Tools and Python libraries by the team for advanced cybersecurity solutions:
- Polars and Pandas: For fast manipulation of massive security datasets.
- NumPy: For numerical computation and vectorizing security telemetry.
- Plotly and Matplotlib: To create interactive dashboards and visualizations.
Reduction in Mean Time to Respond (MTTR)
The speed of cyber attacks has reached a critical velocity with the use of AI in reconnaissance, phishing, scripting, and operational execution. With this machine-like speed, the average breakout time has reduced to just 29 minutes.
To counter this, Python automation for cybersecurity powers modern SOAR (Security Orchestration, Automation, and Response) platforms like Cortex XSOAR and Splunk SOAR, enabling teams to move beyond restrictive out-of-the-box playbooks. By writing custom Python functions and modifying underlying integration code, security engineers can orchestrate multi-vendor workflows that handle unique business logic and edge cases. This programmatic flexibility transforms a standard security stack into an automated ecosystem capable of responding to incidents.
Tools used by experts are:
- Httpx & Aiohttp: For asynchronous API calls to disparate security tools during an incident.
- Boto3 (AWS) / Azure SDK: For programmatic cloud infrastructure control, enabling instant isolation of compromised assets.
- PyMISP: To interact with Threat Intelligence Platforms to pull real-time blocklists.
Digital Forensics and Incident Response (DFIR)
Python serves as the functional backbone for modern DFIR. It allows investigators to automate the ingestion and analysis of digital artifacts across massive environments. By scripting the acquisition of volatile memory and disk images from thousands of endpoints simultaneously, teams can reconstruct unified attack timelines in a significantly lower time.
This approach ensures forensic integrity by minimizing human error during evidence collection and provides the processing speed required to bypass sophisticated anti-forensics techniques.
Key tools are:
- Volatility Framework: For high-speed, automated memory forensics, enabling the detection of rootkits, command history, and injected code in RAM.
- Plaso (log2timeline): An engine used to aggregate and normalize timestamps from disparate logs into a comprehensive "super-timeline" of events.
- PyTSK (The Sleuth Kit): Provides low-level Python bindings for deep-dive file system analysis, allowing programmatic recovery of deleted files and hidden partitions.
- DFTimewolf: Used to orchestrate complex forensic data collection and analysis workflows across multi-cloud environments.
Penetration Testing and Red Team Operations
Python in ethical hacking and authorized penetration testing is widely used because it makes offensive workflows easier to automate. Cybersecurity experts use it to script reconnaissance, interact directly with network protocols, prototype exploit logic, fuzz services, and reproduce attack paths in controlled environments.
This is especially prevalent in Active Directory attack simulations. Techniques such as Golden Ticket attacks, DCSync, and Kerberoasting, which are staples of modern red team engagements, are all implemented or automated through Impacket, a widely used Python-based framework for enterprise security assessments today.
Some other relevant tools and Python libraries used by experts are:
- Impacket: Low-level interaction with network protocols such as SMB and MSRPC, and for building or running Active Directory and Windows-network testing utilities.
- Metasploit External Python Modules: To extend Metasploit with executable Python modules.
- Shodan API: To automate internet-exposed asset discovery and external attack-surface reconnaissance from Shodan’s indexed data.
- pwntools: For rapid exploit prototyping, payload building, process/socket interaction, and debugging during exploit development.
- Boofuzz: To build scripted fuzzers for network protocols and send malformed or mutated inputs.
Cryptography and Data Privacy
As organizations prepare for stronger data protection in 2026, Python is not typically used to invent new encryption methods from scratch. Instead, it is used to automate and apply trusted cryptographic controls inside real security workflows.
Cybersecurity experts also use it to manage certificates, validate tokens, handle encryption and decryption through proven libraries, verify digital signatures, and support secure login flows built on standards such as OIDC and OAuth 2.0. This makes it easier to update security implementations, test new standards, and integrate stronger protections without rebuilding the entire application stack.
Key tools used by experts are:
- Cryptography.io: For high-level symmetric encryption (Fernet) and low-level interfaces to hardware-backed primitives.
- PyCryptodome: For low-level access to fundamental primitives, including AES, RSA, and Elliptic Curve Cryptography (ECC).
- PyNaCl: For digital signatures and authenticated encryption with minimal room for implementation error.
- Hashlib: A native module for secure message auditing and data integrity verification using modern hashing standards like SHA-256, SHA-3, and BLAKE2.
Closing Thoughts
We have understood that Python has become a foundational language in modern cybersecurity. Its value lies in the combination of flexibility and a mature ecosystem that supports everything from workflow automation to protocol-level testing and machine learning-driven security use cases.
But we also need to consider that the advantage is not in the language itself, but in the ability to turn security requirements into maintainable systems that can evolve with the threat landscape. That is where execution becomes the differentiator.
Off-the-shelf tools can cover standard threats and common controls, but they cannot fully address organization-specific risks tied to proprietary applications, such as internal workflows, custom data flows, legacy systems, and business-context attack patterns. So, if you are planning to build security capabilities that work in production, you must leverage specialized Python development services or hire dedicated Python developers to build a secure ecosystem for your organization.
Frequently Asked Questions
How does Python compare to Go or Rust for security tooling?
Many experts are using Python for cybersecurity for security automation, orchestration, analytics, and fast tool development because it reduces build time and offers strong library support. For components where throughput, low-level system access, or memory control are critical, teams typically use Go, Rust, or C/C++ instead, while keeping Python at the workflow and integration layer.
How is Python used in threat detection and incident response?
Python is used to build detection pipelines, enrich alerts, automate investigation steps, correlate evidence, and trigger response workflows across security tools. It is also used in Security Orchestration, Automation, and Response (SOAR) use cases where fast action is needed, such as isolating systems, revoking access, or pushing indicators into threat intelligence platforms.
What are the limitations of using Python in cybersecurity?
The language is highly effective for orchestration, automation, analysis, and rapid development, but it is not always the best choice for every low-level or performance-critical security component. Some use cases may still require tools or services built in lower-level languages. In most environments, Python works best as the layer that connects systems, automates workflows, and operationalizes security logic.
















Sign in to leave a comment.