Introduction: The Imperative of Security in High-Stakes DApps
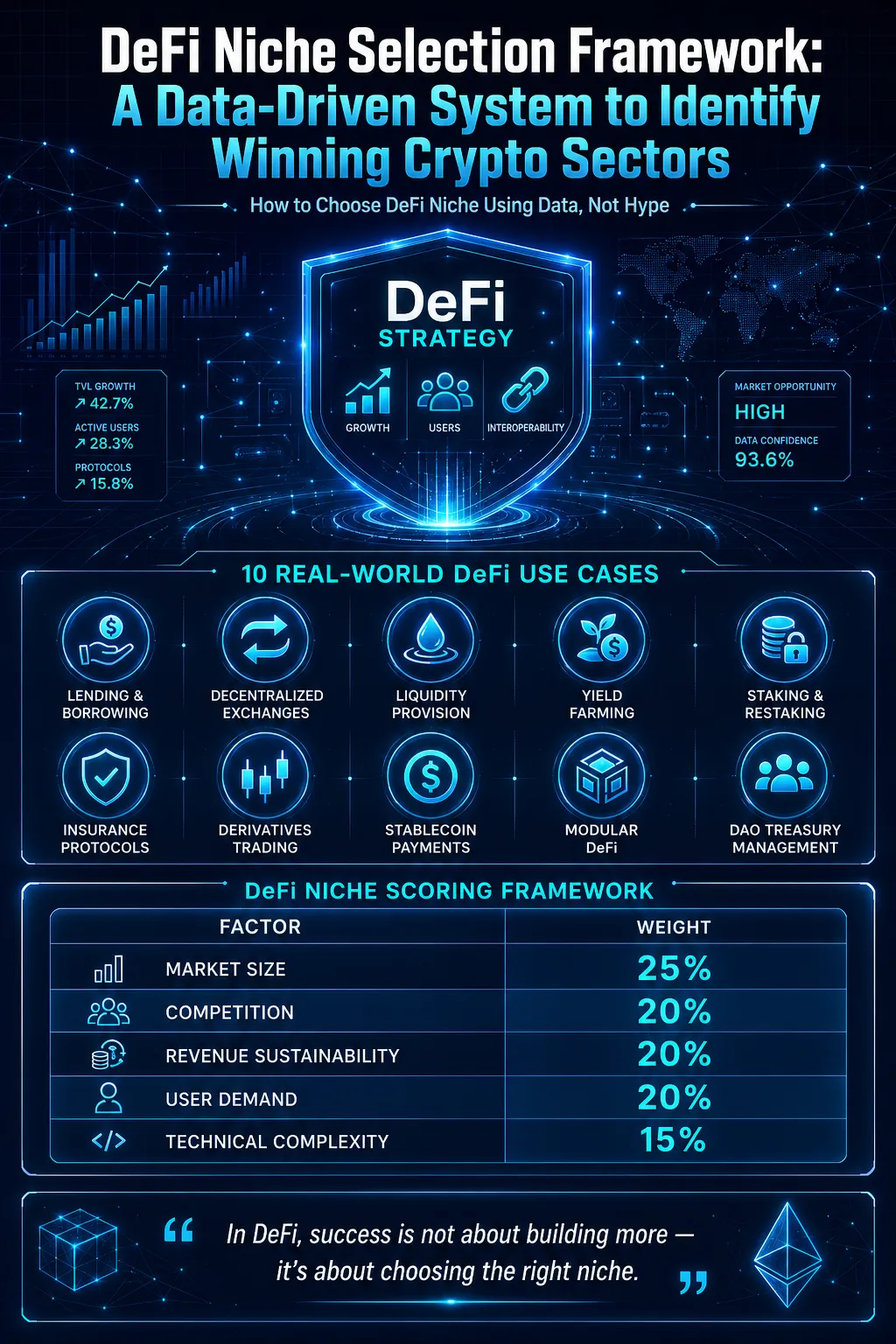
As decentralized applications (DApps) evolve into platforms that manage significant financial assets, sensitive data, and critical business operations, security becomes a paramount concern. High-stakes DApps, including decentralized finance (DeFi) protocols, NFT marketplaces, and enterprise blockchain solutions, face an increasing threat landscape, ranging from smart contract vulnerabilities to sophisticated cyberattacks.
The adoption of advanced security protocols ensures that these platforms operate reliably, maintain user trust, and protect digital assets. Professional dapp development company provide specialized dapp development services focused on designing secure, resilient, and compliant systems that mitigate potential risks while supporting scalability and performance.
The Anatomy of Security Risks in High-Stakes DApps
High-stakes DApps face multiple layers of security challenges. Smart contract vulnerabilities, such as reentrancy attacks, logic flaws, and overflow/underflow errors, can result in significant financial losses. Additionally, external threats from hackers targeting private keys, decentralized oracles, or cross-chain bridges pose risks to the integrity of the platform.
Network-level threats, including denial-of-service (DoS) attacks and 51% attacks, also threaten operational continuity. Moreover, as DApps increasingly integrate with off-chain systems and enterprise applications, securing API connections, data feeds, and interoperability points becomes crucial.
A professional dapp development company ensures that dapp development services include threat modeling, penetration testing, and continuous monitoring to address both on-chain and off-chain vulnerabilities.
Core Security Protocols for High-Stakes DApps
1. Smart Contract Audits and Formal Verification
Smart contracts are immutable once deployed, making pre-deployment audits critical. Comprehensive audits include code review, static analysis, and testing under multiple scenarios. Formal verification uses mathematical proofs to ensure that smart contracts behave exactly as intended, minimizing the risk of exploitation.
2. Multi-Signature Wallets and Threshold Signatures
Multi-signature wallets require multiple approvals for executing sensitive transactions, reducing the likelihood of unauthorized access. Threshold signature schemes extend this by enabling flexible combinations of approvals while maintaining cryptographic security, making them essential for high-value operations.
3. Decentralized Oracle Security
Oracles provide off-chain data to on-chain smart contracts, and their compromise can undermine the entire DApp. Utilizing decentralized oracle networks, data aggregation techniques, and validation layers ensures the integrity, availability, and accuracy of external information.
4. Layered Access Control
Implementing role-based and attribute-based access control ensures that users, administrators, and automated systems only have the necessary permissions. This minimizes the attack surface and ensures that critical operations are not accessible to unauthorized entities.
5. Continuous Monitoring and Incident Response
Real-time monitoring systems track unusual activities, failed transactions, or attempted intrusions. Automated alert mechanisms combined with pre-defined incident response protocols enable rapid containment and mitigation of security events.
Advanced Security Techniques
1. Zero-Knowledge Proofs (ZKPs)
Zero-knowledge proofs enable the verification of transaction validity or user credentials without revealing sensitive information. High-stakes DApps benefit from ZKPs by enhancing privacy while maintaining compliance and transparency.
2. Encrypted Off-Chain Computation
Certain complex operations are better handled off-chain to reduce costs and improve speed. Using secure multi-party computation (MPC) and homomorphic encryption ensures that off-chain data processing maintains confidentiality and integrity.
3. Cross-Chain Security Protocols
As high-stakes DApps increasingly interact with multiple blockchains, securing cross-chain bridges becomes essential. Techniques such as atomic swaps, fraud proofs, and relayer authentication help maintain security across heterogeneous networks.
4. AI-Powered Threat Detection
Machine learning algorithms can analyze transaction patterns, user behavior, and network activity to detect anomalies and potential attacks in real-time. AI-powered solutions complement traditional security protocols, providing proactive protection.
Case Studies: Security in High-Stakes DApps
1. DeFi Lending Platforms
DeFi lending platforms manage billions of dollars in liquidity. Implementing multi-signature governance, regular smart contract audits, and oracle validation protocols has been crucial in preventing exploits and maintaining user confidence.
2. NFT Marketplaces
High-value NFT transactions require robust access control and fraud detection. Event-driven monitoring, transaction anomaly detection, and encrypted storage of metadata enhance the security of both assets and users.
3. Enterprise Blockchain Solutions
Enterprise DApps handling supply chain data or financial settlements employ hybrid on-chain and off-chain security models, integrating zero-knowledge proofs, encrypted computation, and access control frameworks to ensure compliance and operational integrity.
A professional dapp development company integrates these approaches into dapp development services, providing tailor-made security solutions that align with each platform’s operational requirements.
Best Practices for Developers
- Adopt a security-first mindset from architecture design to deployment.
- Use automated testing tools alongside manual code reviews.
- Regularly update smart contracts and security protocols to mitigate evolving threats.
- Integrate decentralized identity and authentication mechanisms for enhanced user verification.
- Maintain transparency through open security audits to build trust with users and stakeholders.
Future of Security in High-Stakes DApps
The future of high-stakes DApp security will be shaped by innovations in AI, cryptography, and decentralized infrastructure. Predictive analytics will anticipate potential attack vectors, while composable security modules will allow developers to deploy reusable, standardized protocols. Integration of cross-chain security frameworks will enable seamless interoperability without compromising safety.
Professional dapp development services will increasingly incorporate automated compliance checks, privacy-preserving computations, and AI-driven monitoring to ensure that DApps remain resilient against the evolving threat landscape.
Conclusion
High-stakes DApps demand next-level security protocols to safeguard digital assets, ensure operational continuity, and maintain user trust. From comprehensive smart contract audits to multi-signature governance, zero-knowledge proofs, AI-powered threat detection, and cross-chain security, advanced strategies are essential for robust and reliable DApps.
Partnering with a professional dapp development company ensures that end-to-end dapp development services address all security aspects, delivering secure, scalable, and efficient decentralized applications capable of operating in high-stakes environments.
FAQs
1. Why are high-stakes DApps more vulnerable?
High-stakes DApps handle significant value and sensitive data, making them prime targets for attacks. Advanced security protocols are necessary to mitigate these risks.
2. What role does a dapp development company play in security?
A dapp development company provides comprehensive dapp development services including audits, oracle integration, smart contract design, and real-time monitoring to secure applications.
3. How do multi-signature wallets enhance security?
They require multiple approvals for transactions, reducing the risk of unauthorized access and increasing accountability.
4. What are zero-knowledge proofs, and why are they important?
Zero-knowledge proofs allow verification of actions without exposing sensitive data, ensuring privacy and compliance in high-stakes operations.
5. How can AI improve DApp security?
AI analyzes patterns and detects anomalies in real-time, providing proactive threat detection and automated responses to potential attacks.















Sign in to leave a comment.