Everywhere we go, we see RFID implementations from contactless payments to inventory tracking. While it brings a whole lot of convenience to the table, its wireless nature brings unique security hiccups that both individuals and organizations need to grasp. The tech is simple; RFID systems use tags to store data and readers to communicate via radio waves. There are different frequencies, like HF for payment cards and UHF for logistics. So what exactly is the problem? Unlike payment methods that require physical contact, RFID tags can be read remotely, effectively inviting in unauthorized access and data theft, like family members on Diwali.
While a lot of threats have entered and exited, and some have even been exterminated, others have persisted and evolved.
1. Skimming and Electronic Pickpocketing
Attackers are often on the prowl, waiting to use their hidden, portable readers to scan cards in wallets. While a PIN might be required for high-value transactions, the captured data can still be used to make multiple small transactions before the bank smells something off. Also, the stolen card, in combination with other data, can be used for identity fraud. There have been incidents where ATMs and POS terminals have been tampered with to skim magnetic stripe data.
2. Cloning and Replay Attacks
RFID tags, in particular, those with weak or no encryption at all, are vulnerable to cloning. An attacker can duplicate a legitimate tag’s ID for unauthorized access. This is clearly exhibited in India’s FASTag system, where researchers have demonstrated how FASTag IDs can be cloned from parked vehicles to bypass tolls, skilfully shifting the costs to legitimate owners. It stands to reason that an unencrypted tag can lead to a lot more than petty fraud. It can cripple ginormous infrastructures.
3. API Exploits and System Manipulation
To make things even messier, it’s not just the tags that are vulnerable; even backend systems managing RFID data are targets. Insecure mobile apps or web portals can expose user data or allow account manipulation, leading to unauthorized charges or even vehicle tracking.
4. Denial of Service (DoS) Attacks:
Attackers don’t always steal data; they can also disrupt RFID systems by flooding the radio spectrum with interference. This can absolutely cripple operations that are reliant on RFID, like automated inventory in warehouses, ripping holes in the pockets of stakeholders.
Final Thoughts:
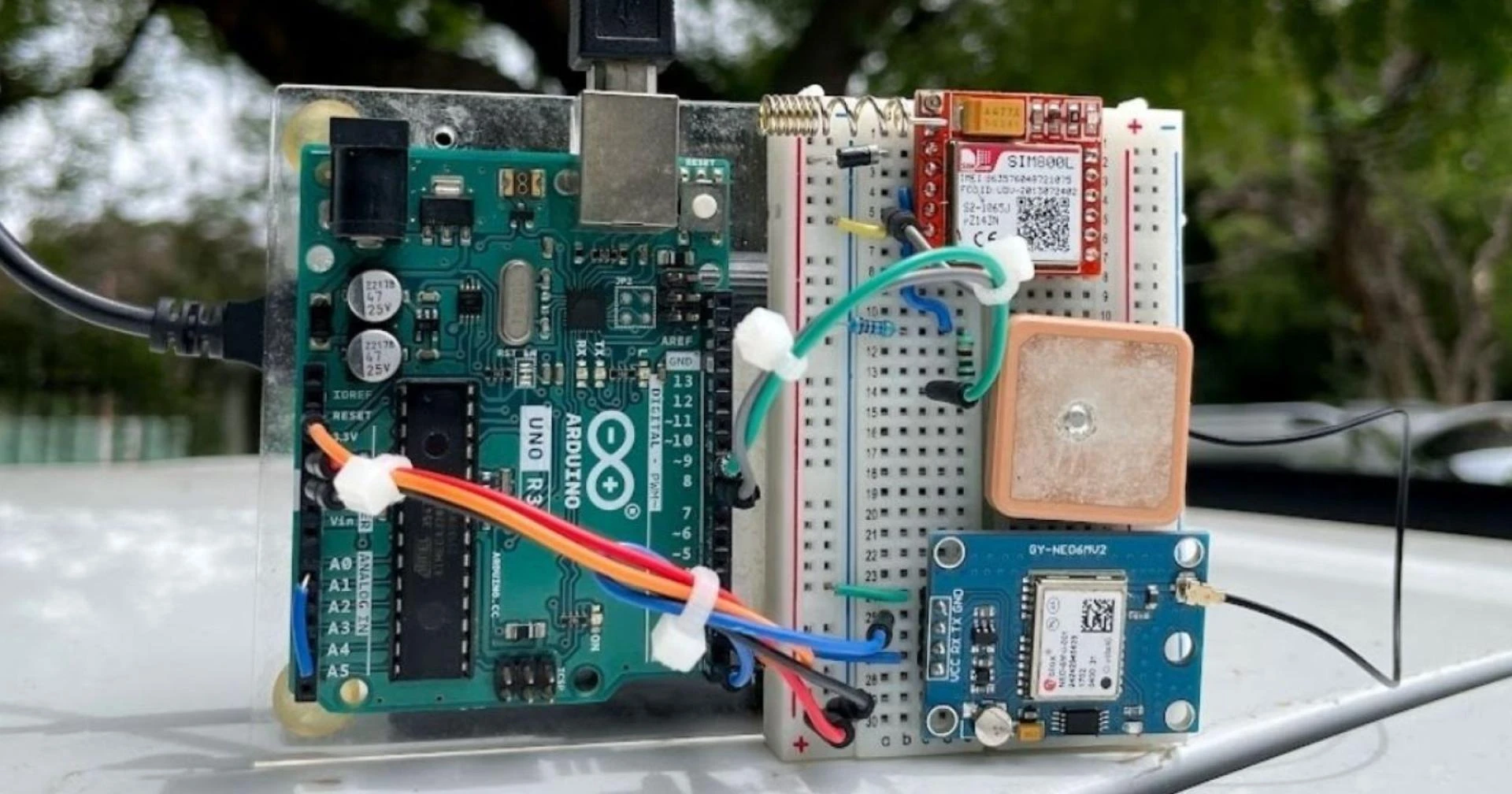
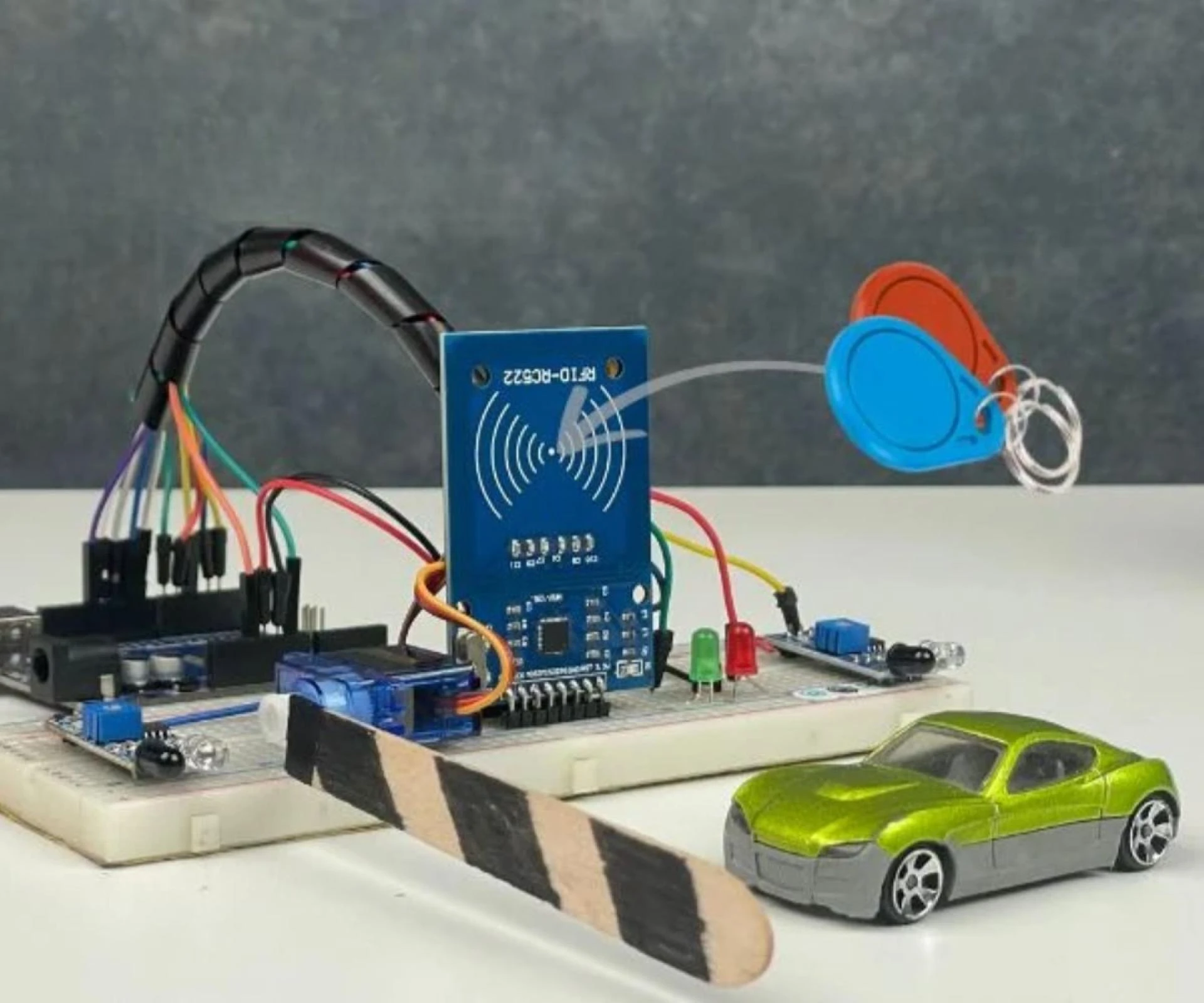
RFID is great tech when it comes to low-risk applications like attendance tracking, which is why it’s a staple in numerous IoT and Arduino projects. This RFID-based attendance system using Arduino is a perfect hands-on example. However when stakes are higher, staying safe with RFID means using simple tools like RFID-blocking wallets, keeping sensitive data off the tags, and making sure that systems use strong encryption and security checks on the regular. As the tech grows with AI and IoT, so do the threats. As the threats grow, so do the defenses. It's about being smart, staying updated, and most of all, exercising common sense every day.













Sign in to leave a comment.