Introduction
In today's digital environment, distributed denial of service (DDoS) assaults remain a persistent and changing danger. These assaults may render internet services unusable, interfere with corporate activities, and result in losses of money.
We may, however, get important insights for surviving and lessening the effects of DDoS attacks by examining real-life scenarios and learning from the mistakes of the past.
In this blog article, we will examine prominent DDoS assault examples and draw conclusions that can strengthen defenses against such occurrences.
Case Study: Memcached Reflection Attack
Memcached reflection was used in one of the biggest DDoS assaults in recent years. Attackers increased traffic on target websites by abusing weak Memcached servers.
The incident made clear how crucial adequate network monitoring, incident response procedures, and cooperation with DDoS mitigation providers are.
Organizations can successfully fight against such volumetric attacks by quickly recognizing the attack, comprehending the attack vector, and collaborating with mitigation experts.
Lessons Learned from IoT Botnet Attacks
IoT botnets have grown to be a key danger vector for mounting widespread DDoS attacks in recent years. Insecure IoT devices are compromised by attackers, who then use the combined power of those devices to saturate targets with traffic.
This emphasizes how crucial it is to protect IoT devices with strong passwords, consistent firmware updates, and network segmentation.
In order to effectively detect and neutralize IoT botnet-based attacks, organizations need also deploy rate restriction, traffic filtering, and anomaly detection tools.
Preventing Attacks at the Application Layer
Attacks at the application layer are designed to deplete server resources, making it harder for authorized users to use a service. These attacks frequently take advantage of holes in APIs or web applications.
Organizations should put a high priority on secure coding practices, routinely patch vulnerabilities, and use Web Application Firewalls (WAFs) to block malicious traffic in order to fight against application layer assaults.
Plans for handling incidents should include methods for quickly identifying and thwarting such attacks as well as keeping in constant contact with the impacted people.
Design of DDoS-resistant infrastructure
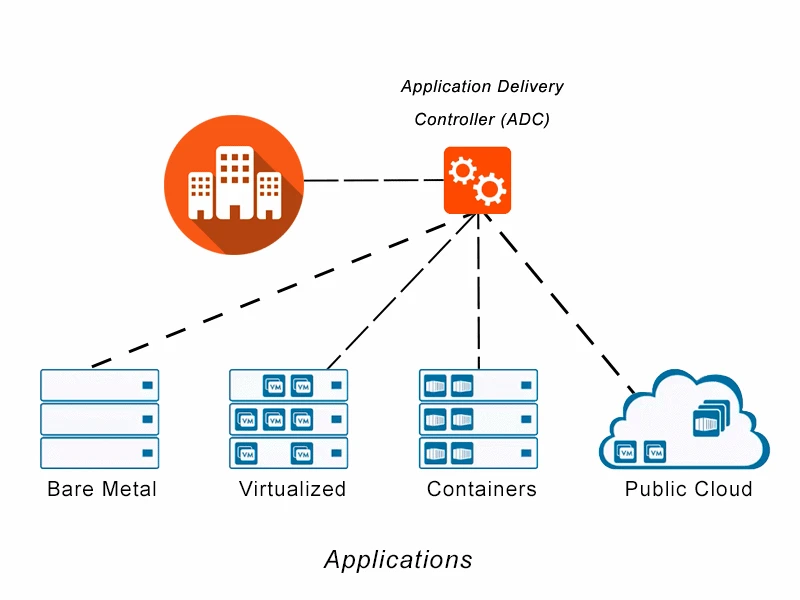
It's essential to have a DDoS-resistant architecture if you want to withstand significant attacks. The use of distributed, scalable architectures by businesses that can cope with traffic spikes should be prioritized.
By distributing traffic among several servers, Content Delivery Networks (CDNs) and load balancing techniques can lessen the impact of volumetric attacks.
Differentiating between legitimate traffic and fraudulent requests can be made easier by putting rate restriction techniques, behavioral analytics, and traffic analysis technologies into use.
Organizations can better survive DDoS attacks by including redundancy and diversification into their infrastructure.
Active DDoS Defense Strategies
To enhance DDoS defense, one should adopt proactive measures like:
a) DDoS Preparedness: Be prepared for DDoS attacks by creating thorough incident response plans that involve working with DDoS mitigation companies and establishing communication channels. Regularly run simulations and tabletop exercises to evaluate the viability of these initiatives.
b) Network Monitoring: Ongoing network traffic monitoring allows for the early identification and mitigation of DDoS attacks. To detect and stop harmful traffic patterns, implement Intrusion Detection and Prevention Systems (IDPS).
c) Collaborative Defense: To stay informed about new threats, take part in industry information-sharing platforms and work with DDoS mitigation specialists. By exchanging threat intelligence, organizations can spot possible threats and put preventative measures in place.
d) Employee Education: Hold frequent training sessions to inform staff members about DDoS assaults, their effects, and the best ways to respond to them. Inform personnel about the value of following security best practices, such as staying away from dubious sites and maintaining excellent password hygiene.
Conclusion
It takes a combination of preventative measures and knowledge gained from actual situations to survive a DDoS attack. Businesses may improve their defenses and lessen the impact of such threats by knowing the attack routes and tactics used by organizations who successfully mitigated DDoS attacks.
It is essential to keep a proactive attitude, make significant security investments, and keep up with developing DDoS attack methodologies. Organizations can improve the security of their online presence, guarantee continuous service delivery, and efficiently respond to future DDoS attacks by taking the proactive steps advised.
















Sign in to leave a comment.