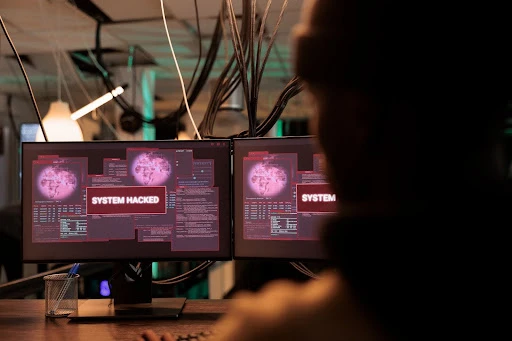
Cyberattacks are growing increasingly sophisticated, putting individuals and businesses alike at greater risk. With every passing day, hackers develop new methods to exploit vulnerabilities, making cybersecurity an essential focus for anyone operating in the digital landscape. A robust cyber security review and proactive defense strategy are critical to safeguarding sensitive data and minimizing the risk of breaches.
This blog offers insights into the top cybersecurity practices you can adopt to strengthen your defenses against modern threats. Whether you're protecting personal information or managing IT infrastructure for a business, these actionable tips will help you reduce vulnerabilities and stay one step ahead of attackers.
Understanding the Modern Cybersecurity Landscape
To build a strong cybersecurity defense, it’s important to understand the types of threats out there. Here are some of the most common cyberattacks that organizations and individuals face in today’s environment:
- Phishing: Deceptive emails designed to trick recipients into revealing sensitive information or downloading malware.
- Ransomware: Malicious software that encrypts a victim's data and demands payment for decryption.
- Social Engineering: Exploiting human psychology to gain unauthorized access to systems.
- Zero-Day Exploits: Cyberattacks that occur before a developer has patched a software vulnerability.
- Distributed Denial-of-Service (DDoS) Attacks: Overwhelming a system to render it unavailable to users.
The cybersecurity landscape is dynamic and rapidly evolving. New vulnerabilities and attack methods are discovered regularly, which underscores the importance of staying informed and updated on emerging threats.
Essential Cybersecurity Practices to Protect Against Threats
1. Conduct Regular Cybersecurity Reviews
A thorough cyber security review is like a health check-up for your systems—essential for identifying vulnerabilities and areas that need improvement. Here's how to do it right:
- Audit Your Software and Hardware: List all devices, applications, and programs your organization or personal setup relies on. Ensure all of these are updated to their latest versions to close known security gaps.
- Assess User Permissions: Review who has access to critical systems and data. Restrict permissions to the bare minimum necessary for job functions.
- Evaluate Risky Behavior: Understand how your team uses digital tools. Are there shadow IT practices (e.g., unauthorized apps) that could pose risks?
- Simulate Attacks: Use penetration testing to simulate a cyberattack and identify any vulnerabilities before an attacker does.
Cybersecurity reviews should be conducted regularly, preferably every six months or after significant changes in your systems.
2. Use Strong Authentication Measures
Passwords alone are no longer sufficient protection. Strengthen user authentication with these strategies:
- Implement Multi-Factor Authentication (MFA): Adding an extra layer of protection, such as fingerprint scans or one-time verification codes, makes it much harder for malicious actors to gain unauthorized access.
- Enforce Strong Passwords: Require passwords that use combinations of uppercase letters, lowercase letters, numbers, and special characters, and consider implementing a password manager to encourage their use.
3. Educate Employees About Cybersecurity
People often serve as the first line of defense—or the weakest link—in cybersecurity. Educating yourself or your team can make a massive difference:
- Provide Ongoing Training: Cybersecurity awareness sessions can help everyone identify phishing attempts, use strong passwords, and follow best practices.
- Phishing Simulations: Run simulated phishing attacks to help employees hone their ability to detect and avoid real scams.
- Encourage Open Communication: Employees should feel comfortable reporting suspicious activity without fear of blame. Early reporting can prevent incidents from escalating into full-blown cyberattacks.
4. Keep Software and Operating Systems Updated
Outdated software creates opportunities for hackers to exploit unpatched vulnerabilities. Follow these steps to stay secure:
- Enable Automatic Updates: This ensures you receive security patches as soon as they’re available.
- Standardize Update Schedules: If auto-updates aren’t an option, set regular reminders to update your software manually.
By enabling timely updates, you protect against threats like zero-day exploits, which take advantage of unpatched vulnerabilities.
5. Back Up Your Data Regularly
Ransomware attacks are one of the most damaging and costly threats businesses face. A strong data backup strategy can minimize their impact:
- Use the 3-2-1 Rule: Keep at least three copies of your data, stored on two different types of media, with one copy stored offsite.
- Automate Backups: Schedule automatic backups to save time and ensure consistency.
- Test Backup Integrity: Conduct trial restorations to ensure your data can be recovered smoothly in case of an emergency.
6. Install and Configure Firewalls and Antivirus Software
Firewalls and antivirus software act as essential barriers against malicious activity. Here’s how to make the most of them:
- Use Enterprise-Grade Firewalls for businesses to filter and inspect network traffic. Home users should also set up high-quality routers with built-in firewall capabilities.
- Choose Reputable Antivirus Software to detect and remove malware and other malicious files that may target your system.
- Enable Real-Time Protection to ensure that threats are identified and addressed as quickly as possible.
7. Limit Third-Party Access
Third-party vendors and partners often have access to your systems, and their vulnerabilities can become your vulnerabilities. To mitigate this risk:
- Vet Vendors Carefully: Ensure they follow stringent cybersecurity practices and policies.
- Limit Access: Only grant third parties access to the systems or data they require for their role.
- Monitor Their Activity: Regularly audit access logs to ensure compliance with your security standards.
8. Adopt a Proactive Threat Detection System
While preventative measures are invaluable, proactive systems for identifying threats as they arise can save your organization from significant damage:
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) monitor network traffic for malicious activity.
- AI-Powered Solutions can analyze patterns and detect anomalies in real-time, alerting you to potential cyberattacks.
What Happens When Cyber Threats Are Neglected?
Failing to implement strong cybersecurity measures can lead to severe consequences, including:
- Financial losses due to stolen data, ransomware breach, or system downtime.
- Reputational damage that affects customer trust and loyalty.
- Legal repercussions from non-compliance with data protection regulations, such as GDPR or CCPA.
A single breach can result in long-term damage to your reputation and bottom line. Prioritizing cybersecurity is no longer an option—it’s a necessity.
Be Proactive, Not Reactive
Cybersecurity is not a one-time task but an ongoing commitment. Staying ahead of cyberthreats means conducting regular cyber security reviews, educating users, and investing in tools that not only protect but also proactively detect potential risks. Implementing these best practices will help keep your data safe and ensure your digital operations run smoothly.





















Sign in to leave a comment.