5 Fundamental Functions of the Cybersecurity Framework:
It's time to comprehend the function of these cybersecurity frameworks now that you know why cybersecurity is necessary and how to defend against cyberattacks. Sensitive information must be shielded from harm or theft. Having it to recover and safeguard your PCs, gadgets, and network would be ideal. for a robust firewall. If you not learn Cyber Security Online Training you must keep up with and get ready for any dangers in future.
- Recognize, comprehend, and control cybersecurity threats to assets, systems, and data.
- Protect: Preserve data and systems (e.g., training, access control).
- Detect: Rapidly recognize risks or events related to cybersecurity.
- In order to contain and recover from incidents, you must respond.
- Recover: Following a cybersecurity event, restore systems and operations.
Different Types of Cyber Attacks:
In addition to knowing how to defend themselves against these cyberattacks, organizations must also be aware of the many types of cyberattacks. They won't be able to take the right precautions to protect it the next time until they determine what kind of attack occurred. The list of different cyberattacks is as follows:
Phishing - Phishing is the technique by which cybercriminals deceive victims into divulging private and sensitive information via emails, texts, or social media.
Malware - A computer program created to disrupt, damage, or obtain illegal access to another computer is known as malware.
Ransomware - Ransomware is a type of malware that encrypts another person's files and requests money to unlock them. This type of ransomware is used in most of the Cyber Security Certification in Bangalore portals which can be easily attacks.
Distributed Denial-of-Service and The denial-of-service attack DoS, or DDoS is the term for when a network or website experiences so many requests or traffic that it crashes or becomes unavailable.
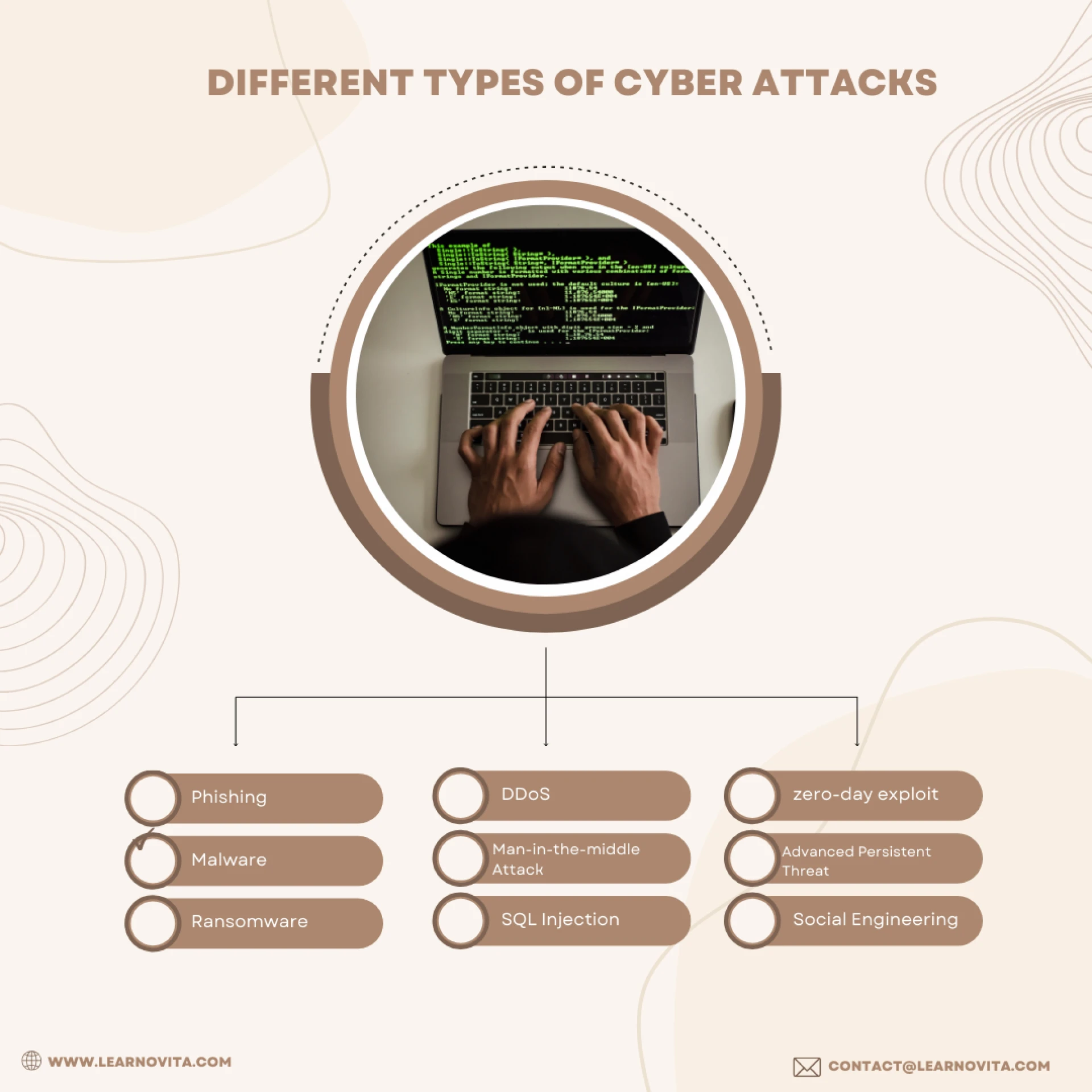
Man-in-the-middle Attack: An attack known as a "man-in-the-middle" (MitM) occurs when a hacker intercepts and modifies communication between two people or parties with the goal of gaining access to a system or stealing data.
SQL Injection: A cyberattack that exploits vulnerabilities in a website's SQL database to get and alter private data.
zero-day exploit - An attack that takes advantage of a software program or application vulnerability that neither the public nor the software developer are aware of is known as a "zero-day exploit.".
Advanced Persistent Threat - The Advanced Persistent Threat, or APT, is a persistent attack that aims to steal data or intellectual property from a designated target. Enhance your cyber security by learning in a well reputed Software Training and Placement Institutes in Chennai. These are primarily observed by organized crime at the state or national level.
Social Engineering - Social engineering is a technique whereby attackers manipulate the victim's emotions to coerce them into divulging private information or taking an action they are not accustomed to taking.
Conclusion:
Maintaining a culture of Cyber Security Online awareness, investing in the latest technologies, and staying vigilant will help your business effectively traverse the digital landscape while preserving the trust and confidence of your clients, partners, and employees.
















Sign in to leave a comment.