

Treating all user permissions the same creates "reviewer fatigue" and hides high-risk access. Learn why effective identity governance requires risk-based prioritization over uniform coverage.

Are your Identity Governance programs designed to pass audits or reduce risk? Discover why focusing solely on compliance documentation is a widespread mistake and what regulatory frameworks actually require for effective oversight.

Many enterprises mistakenly believe that their Identity and Access Management (IAM) systems can govern access as effectively as they enforce it. However, this assumption leads to governance programs that may appear functional at first glance but ultimately fail under scrutiny. Discover the critical differences between enforcement and oversight that can expose significant governance gaps in your organization.
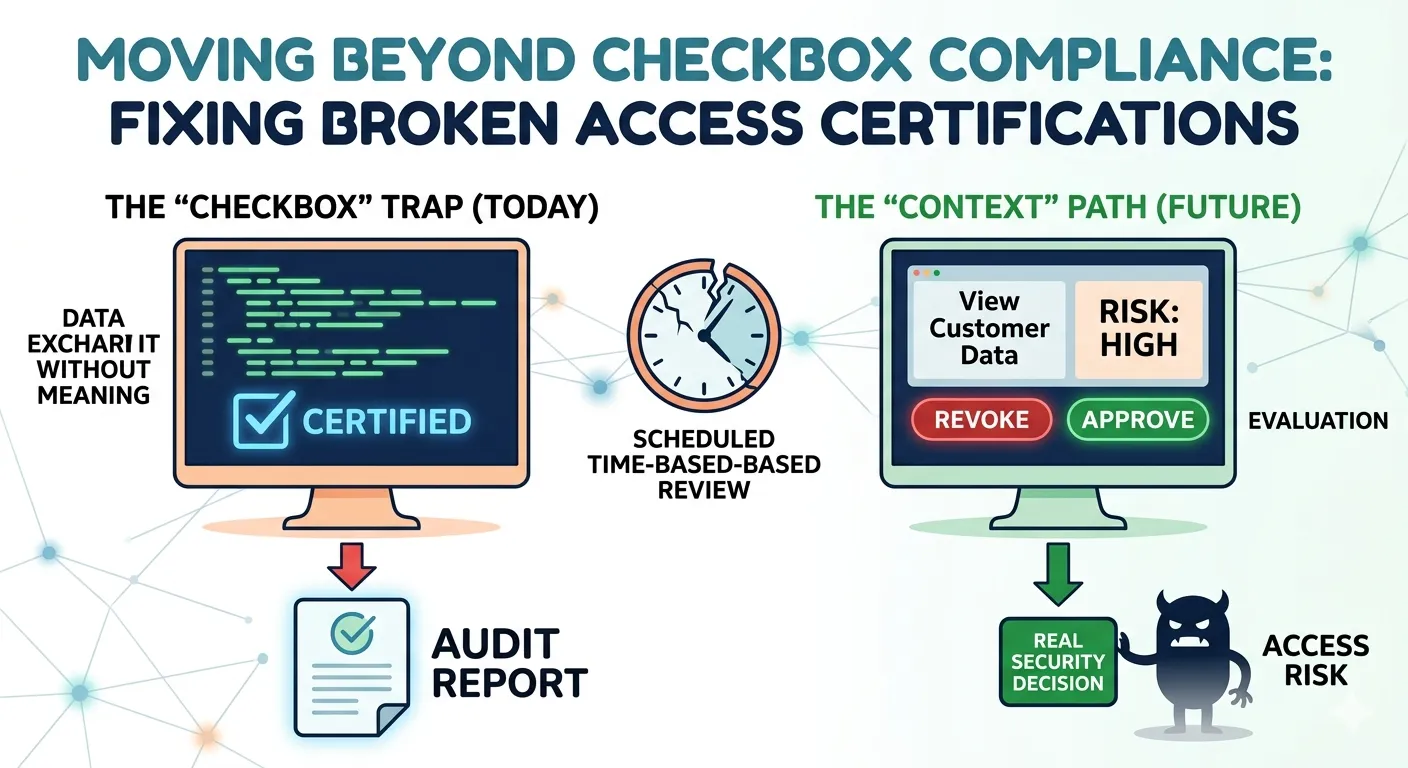
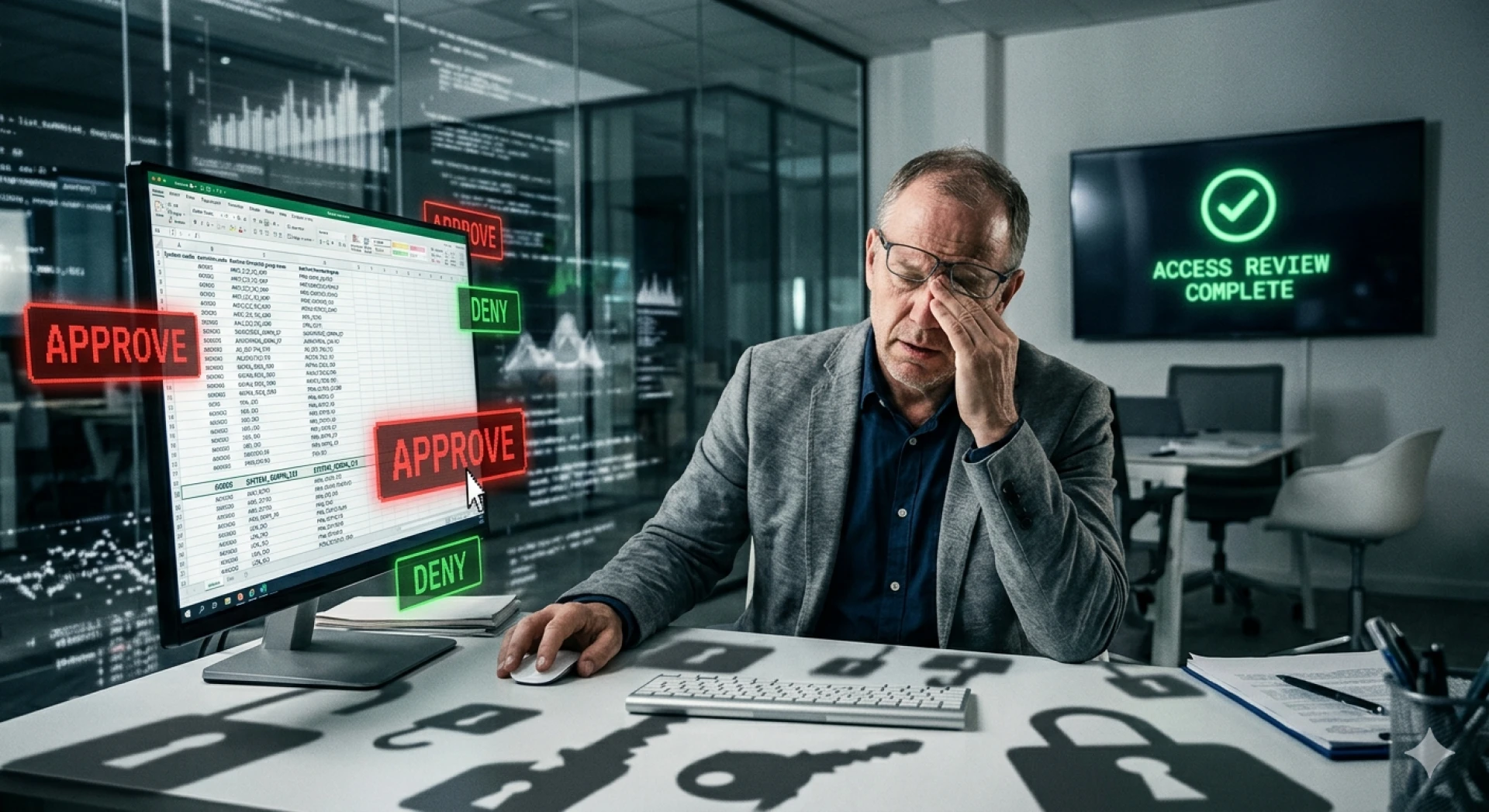
Despite timely reviews and clean reports, many organizations still struggle with risky access issues. The core problem isn't process failure but rather a lack of informed decision-making during access reviews. Discover the hidden flaws in IGA program designs that prevent effective governance and learn how to transform access reviews into meaningful evaluations.
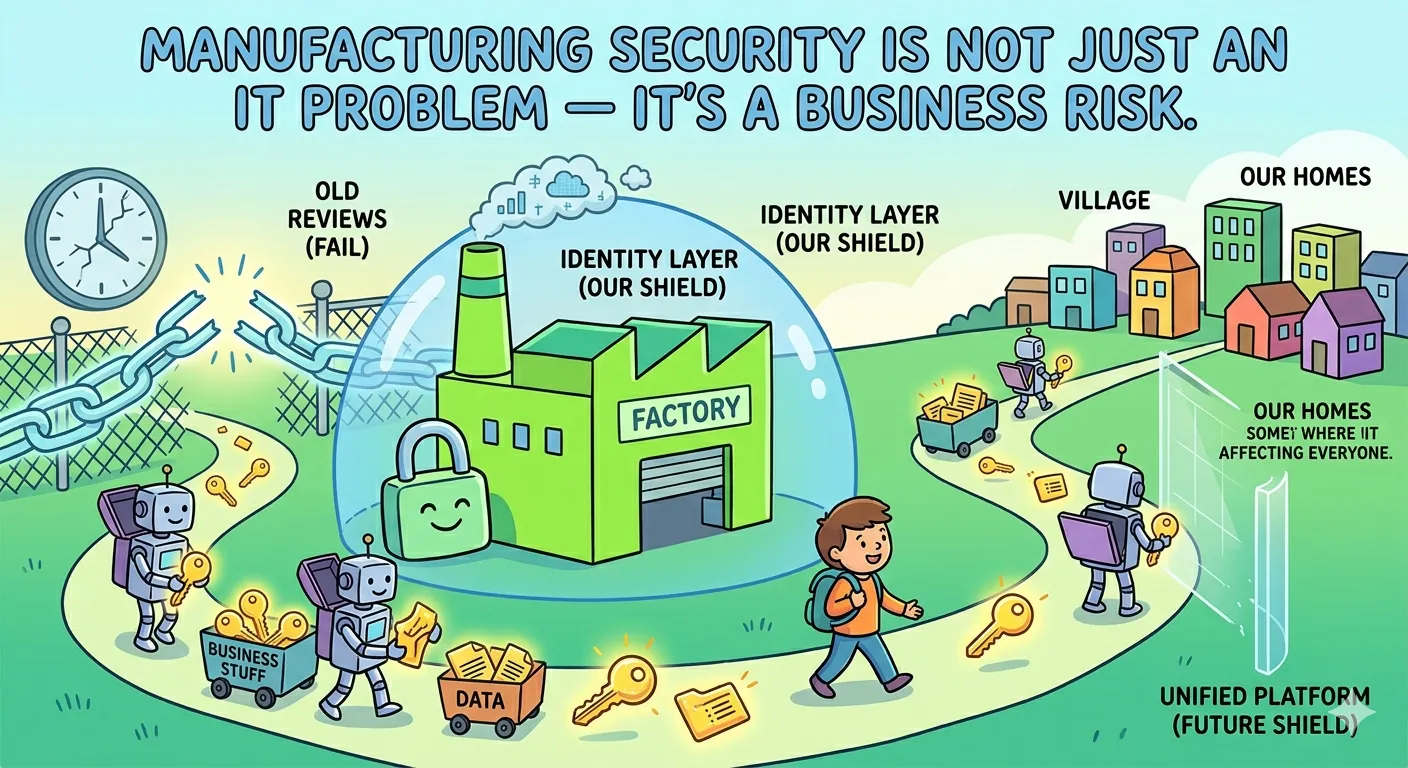
Infographic mapping a complex manufacturing ecosystem, highlighting vulnerability points created by unmanaged, accumulated digital access keys of suppliers and contractors.
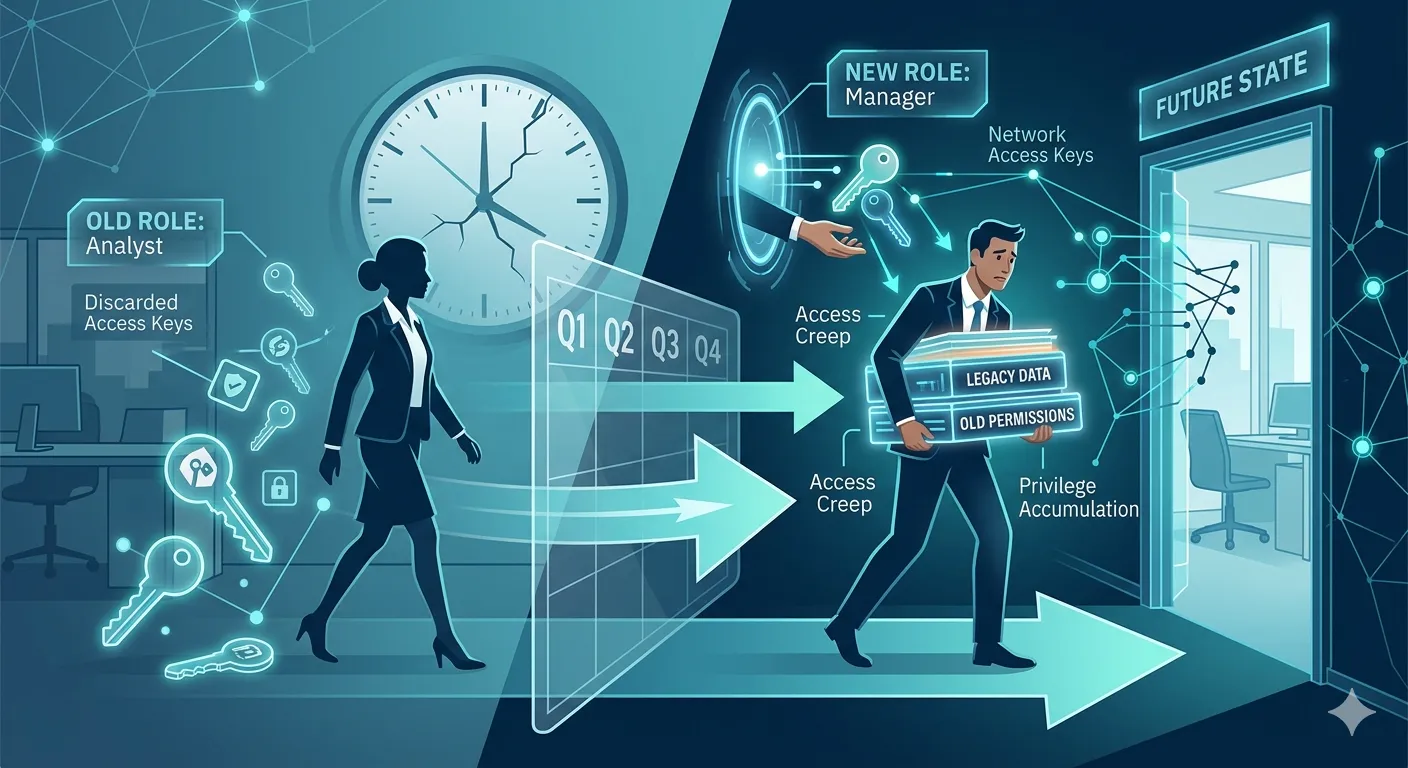
Infographic illustrating access drift and the accumulation of legacy permissions during employee role changes.
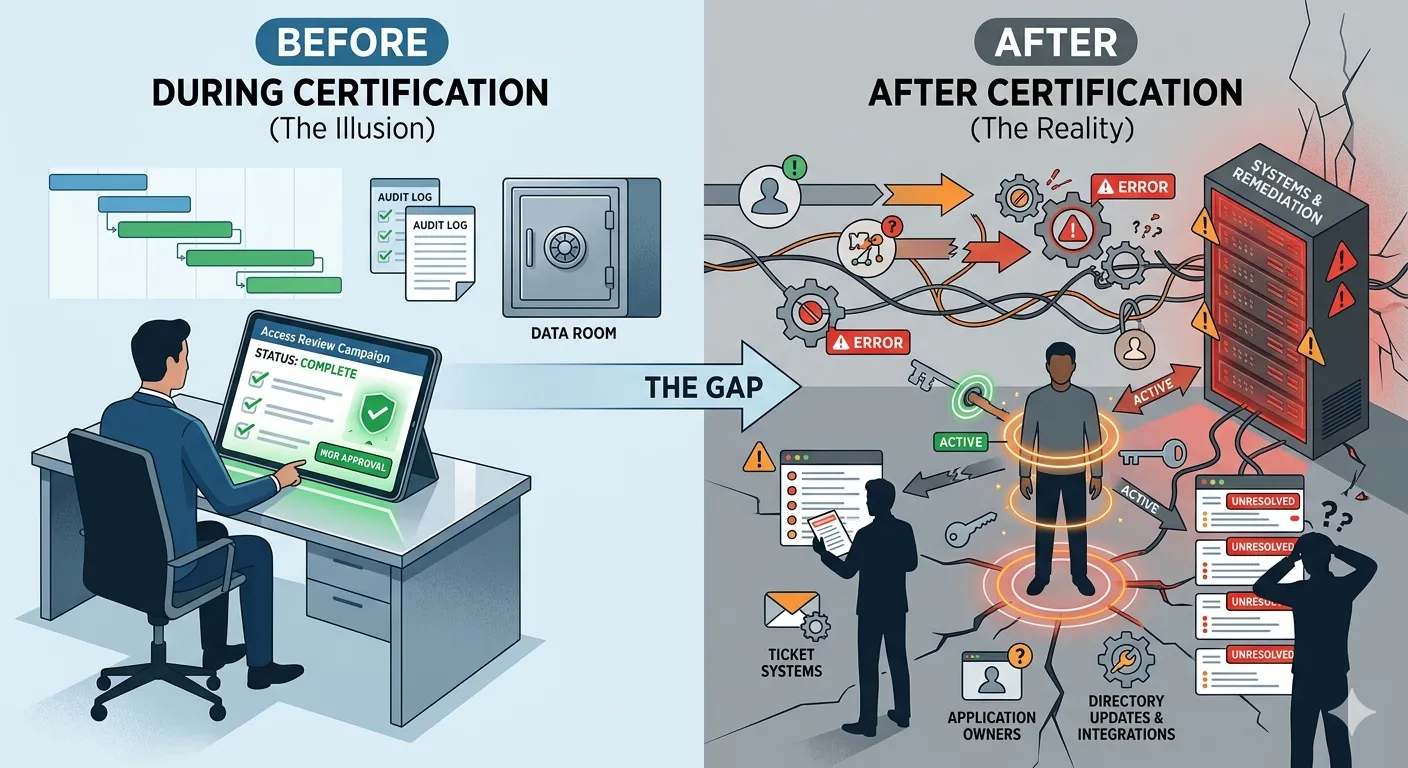
A split-screen illustration titled 'Before vs After Certification.' The left side shows a clean 'Complete' status on an audit dashboard (The Illusion). The right side shows a chaotic web of broken gears, ticket systems, and active user permissions labeled 'The Reality' of failed remediation.
Why Your Access Review Is Lying to You (& How SaaS Made It Worse)

Improving Identity Governance Controls Without Platform Modernization

Why Access Review Completion Rates Don't Equal Risk Reduction: Solving the Fatigue Problem
Is your IGA program reducing risk or just passing audits? Discover why identity governance often becomes a "compliance ritual" and how to shift from binary checkpoints to longitudinal risk reduction.
In financial services, healthcare systems, and government agencies, identity governance often begins with a familiar objective: Pass the audit.&n
Access reviews are a foundational control in enterprise security and compliance programs. They are designed to ensure that users have only the access
Access reviews are a required control in regulated organizations, but they are also one of the least trusted. In hybrid environments, reviews often be

Manual access reviews, Audit risk, Identity governance.

Identity governance has become a critical security and compliance topic for enterprises, yet it remains widely misunderstood. Often reduced to access

Keycloak is powerful. It gives developers an open source platform for authentication, federation, social login, and single sign-on. But open sou

Workday has become the backbone of workforce operations for modern enterprises. It tracks who is hired, promoted, transferred, or exits the organizati

Most modern enterprises have grown into two distinct ecosystems. One is built in the cloud, Microsoft 365, SaaS platforms, and apps protected by Micro