Across regulated industries, identity governance programs often evolve under the shadow of audit preparation.
Access certification campaigns are planned months ahead. Managers receive long lists of user permissions to review. Documentation workflows are carefully structured so that every approval, rejection, and exception can be preserved for examination. When auditors arrive, the organization can produce the evidence they expect to see.
On the surface, this looks like governance maturity.
Yet many organizations still struggle to answer a deceptively simple question: what do audit frameworks actually require from identity governance?
The answer is frequently misunderstood. Most regulatory frameworks are far less prescriptive than organizations assume. They expect oversight, accountability, and traceable evidence that governance controls operate consistently. What they do not prescribe is the exact structure of the governance programs built around those expectations.
This distinction matters more than it appears. When governance programs are designed around assumptions rather than actual regulatory intent, they can become overly focused on producing documentation rather than reducing access risk.
How governance programs slowly become audit-shaped
In sectors such as financial services, healthcare, and the public sector, compliance pressure is unavoidable. Supervisory reviews, regulatory reporting, and external audits create strong incentives for organizations to demonstrate control clearly and consistently.
Over time, identity governance programs begin to mirror the rhythms of those oversight processes.
Quarterly certification campaigns align neatly with reporting cycles. Annual review events fit comfortably into compliance calendars. Governance dashboards begin to track completion metrics such as how many managers submitted reviews on time or how quickly attestation campaigns closed.
These indicators are useful for demonstrating oversight. They help organizations show that governance activity exists and that processes are repeatable.
But those metrics reveal very little about the underlying exposure profile.
An access review campaign can achieve excellent completion rates even if privileged access continues to expand slowly across systems. Certification reports can confirm that managers reviewed entitlements while unnecessary permissions remain intact. Documentation can grow more robust even as the number of access pathways increases.
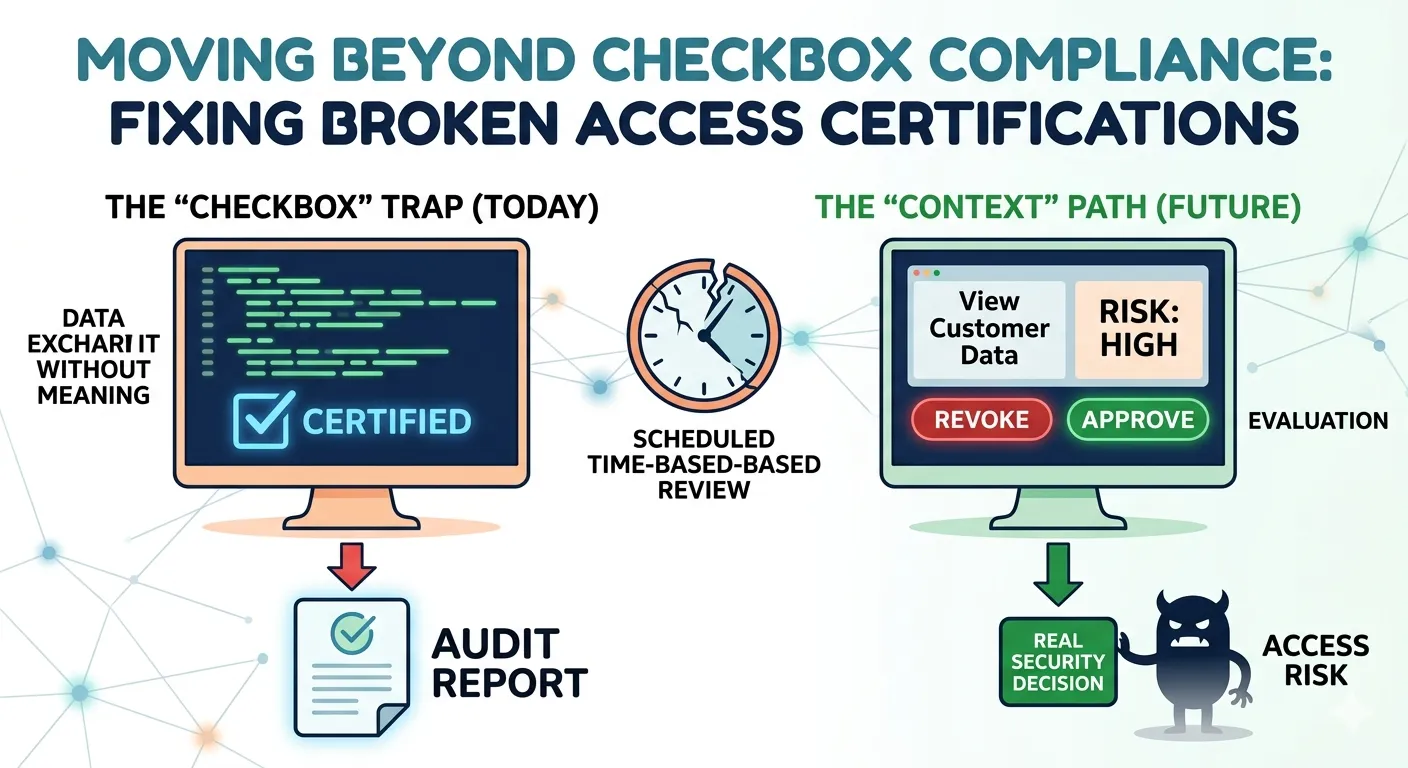
When governance programs are designed primarily to prove that activity occurred, documentation becomes the organizing principle of the system.
This is where audit readiness and governance effectiveness begin to diverge.
What audit frameworks actually evaluate
Contrary to common belief, most audit frameworks do not dictate the operational mechanics of identity governance programs.
Whether the regulatory environment involves SOX, HIPAA, FFIEC guidance, or other supervisory expectations, auditors typically focus on several core principles.
Organizations must demonstrate that access to systems is restricted to authorized individuals. They must ensure that conflicts of interest are prevented through appropriate separation of duties controls. And they must maintain defensible evidence showing that access decisions are subject to oversight and periodic validation.
These expectations define the outcomes regulators want to see.
They do not define the exact operational structures organizations must build to achieve those outcomes.
In other words, audit frameworks require governance to exist and function. They do not require large-scale certification campaigns covering every entitlement in the environment. Nor do they prescribe rigid review cadences as the only acceptable governance model.
Auditors care about whether access oversight is defensible and whether the organization can explain how governance controls operate.
How that oversight is operationalized remains flexible.
Where organizations misinterpret audit expectations
Despite the flexibility built into most regulatory frameworks, many governance programs are designed around assumptions about what auditors require.
These assumptions often take the form of unwritten rules.
Organizations convince themselves that quarterly access reviews are mandatory. They believe every entitlement must be certified regardless of risk level. They assume certification campaigns must cover every system and every permission. Some even treat the sheer volume of evidence produced as proof of governance maturity.
In reality, these habits are rarely dictated by regulation. They are usually internal interpretations that have hardened over time.
As those assumptions become embedded in governance processes, certification campaigns expand. Review volumes increase. Evidence archives grow. Governance teams spend more time coordinating review cycles and collecting documentation.
Meanwhile, the fundamental question remains unanswered: is access risk actually declining?
The difference between oversight and exposure reduction
Audit validation and exposure reduction measure two different things.
Audit validation confirms that governance controls exist and that those controls operate in a way that can be demonstrated during examination. It focuses on oversight and accountability.
Exposure reduction focuses on whether excessive or inappropriate access is actually removed.
The two outcomes are related, but they are not identical.
A governance program can produce excellent documentation showing that reviews occurred while leaving entitlement patterns largely unchanged. Certification campaigns can close successfully even if remediation actions are delayed or inconsistently enforced.
This is how identity governance programs pass audits while failing to reduce risk.
The oversight process is functioning. The exposure profile remains stable.
Recognizing this difference is central to evaluating identity governance effectiveness versus compliance.
The structural misalignment at the center of the problem
When governance programs prioritize documentation production, success metrics naturally revolve around activity indicators.
Completion rates become a measure of effectiveness. Certification statistics rise. Evidence archives expand.
These metrics demonstrate that governance activity occurred. They do not necessarily show that access exposure declined.
This does not indicate operational negligence. In many organizations, governance teams execute certification campaigns diligently and produce high-quality documentation.
The issue lies in how success is defined.
If governance programs measure success primarily through audit readiness indicators, they may consistently satisfy compliance expectations while leaving underlying exposure patterns largely unchanged.
Passing audits confirms that oversight exists.
It does not automatically confirm that governance is reducing risk.
Why the distinction matters for regulated enterprises
For regulated organizations, audit performance often becomes shorthand for governance maturity. Clean audit reports signal that internal controls exist and that oversight mechanisms operate consistently.
From a compliance standpoint, that validation is essential.
However, organizations increasingly recognize that audit success alone does not provide a complete picture of security posture. Boards and executive leadership are beginning to ask a different question: not only whether governance programs pass audits, but whether they are actually reducing exposure.
Understanding what audit frameworks truly require allows organizations to evaluate governance programs more realistically.
Regulators expect defensible oversight and consistent control execution. They do not mandate governance architectures that prioritize documentation volume over measurable exposure reduction.
When governance design reflects that understanding, compliance and security outcomes become aligned rather than competing priorities.
Rethinking governance beyond audit assumptions
Audit readiness will always remain a critical objective for regulated enterprises. Governance programs must produce evidence showing that oversight exists and that access decisions are subject to accountability.
But audit validation should not be mistaken for the ultimate measure of governance effectiveness.
Identity governance becomes significantly more effective when programs are designed to reduce exposure while still producing defensible oversight evidence.
Understanding that audit frameworks require outcomes rather than specific operational mechanics is the first step toward that alignment.
For a deeper exploration of how governance programs evolve beyond audit-driven assumptions and what effective identity governance looks like in practice, see Audit-Driven Identity Governance Doesn’t Reduce Risk.
















Sign in to leave a comment.