We all love that moment when a new AWS service just ‘works’, you click a button, and SageMaker or Glue spins up with default settings. But here’s what rarely gets talked about: those default IAM roles often ship with dangerously broad permissions, AmazonS3FullAccess, for one, and that’s a silent risk waiting to be exploited.
The Problem Hiding in Plain Sight
In May 2025, researchers uncovered that these AWS default roles, like AmazonS3FullAccess, granted sweeping access across S3 buckets and other AWS resources. These aren’t rare edge cases. They’re part of the out-of-the-box experience.
When attackers get hold of credentials tied to such roles, the impact can be catastrophic:
- Privilege escalation: A single compromised role can be leveraged to jump across services or environments.
- Lateral movement: Malicious actors can navigate through internal pipelines or spin up resources undetected.
- Complete account compromise: In worst-case scenarios, attackers gain control of everything from compute to storage.
It’s not speculation. This is how many of today’s cloud breaches begin, not with zero-day exploits, but with poorly governed access.
Where AWS IAM Stops Short
Let’s be clear: AWS IAM is a powerful tool for managing access within the AWS ecosystem. But when you look at today’s enterprise reality, hybrid cloud, third-party SaaS, legacy systems, its limitations start to show:
- No support for customer identity and access management (CIAM) use cases
- Manual or scripted provisioning that lacks scalability
- Fragmented access policies across multi-cloud and on-prem environments
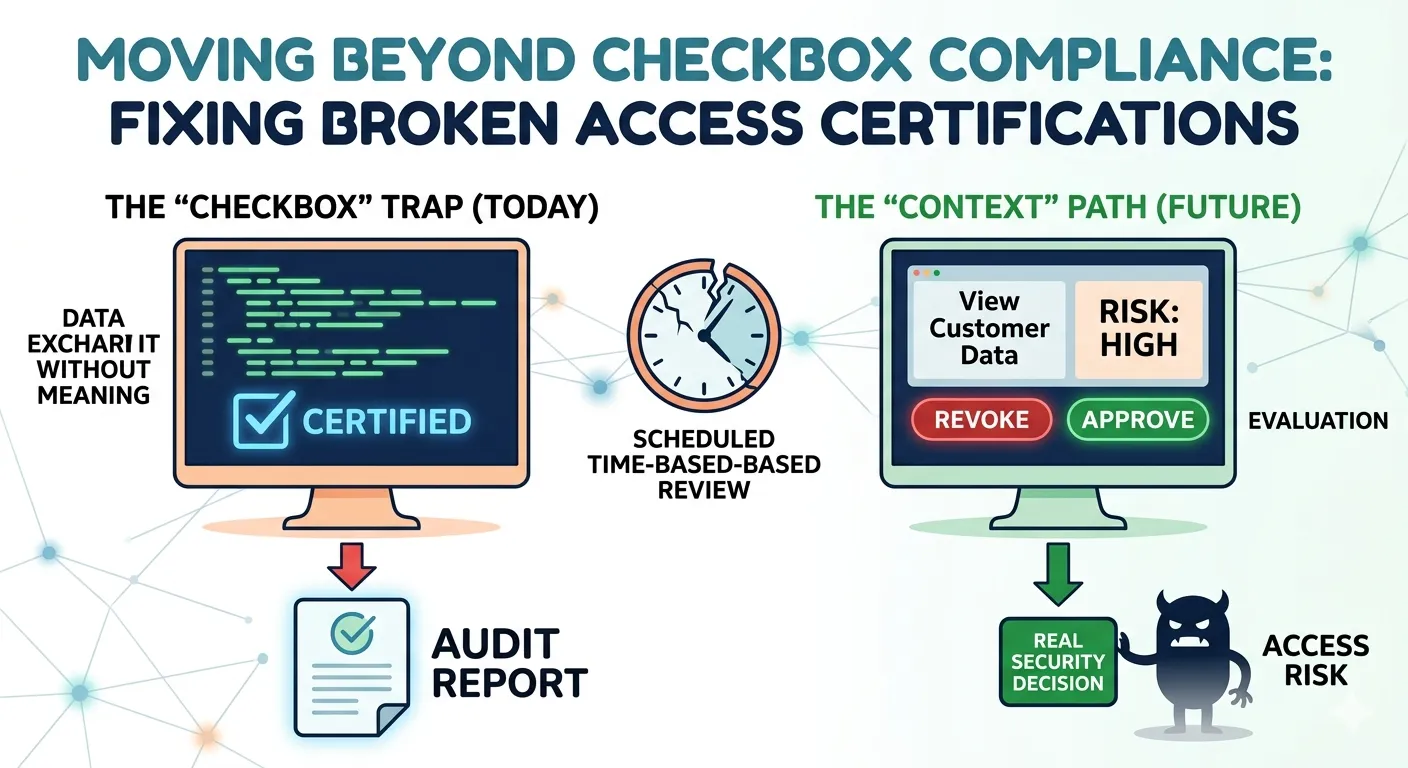
- No native support for centralized access certification or entitlement review
These gaps become more dangerous as companies grow. IBM’s 2023 Cost of a Data Breach Report found that 16% of cloud breaches are tied to misconfigured IAM roles, many of them default.
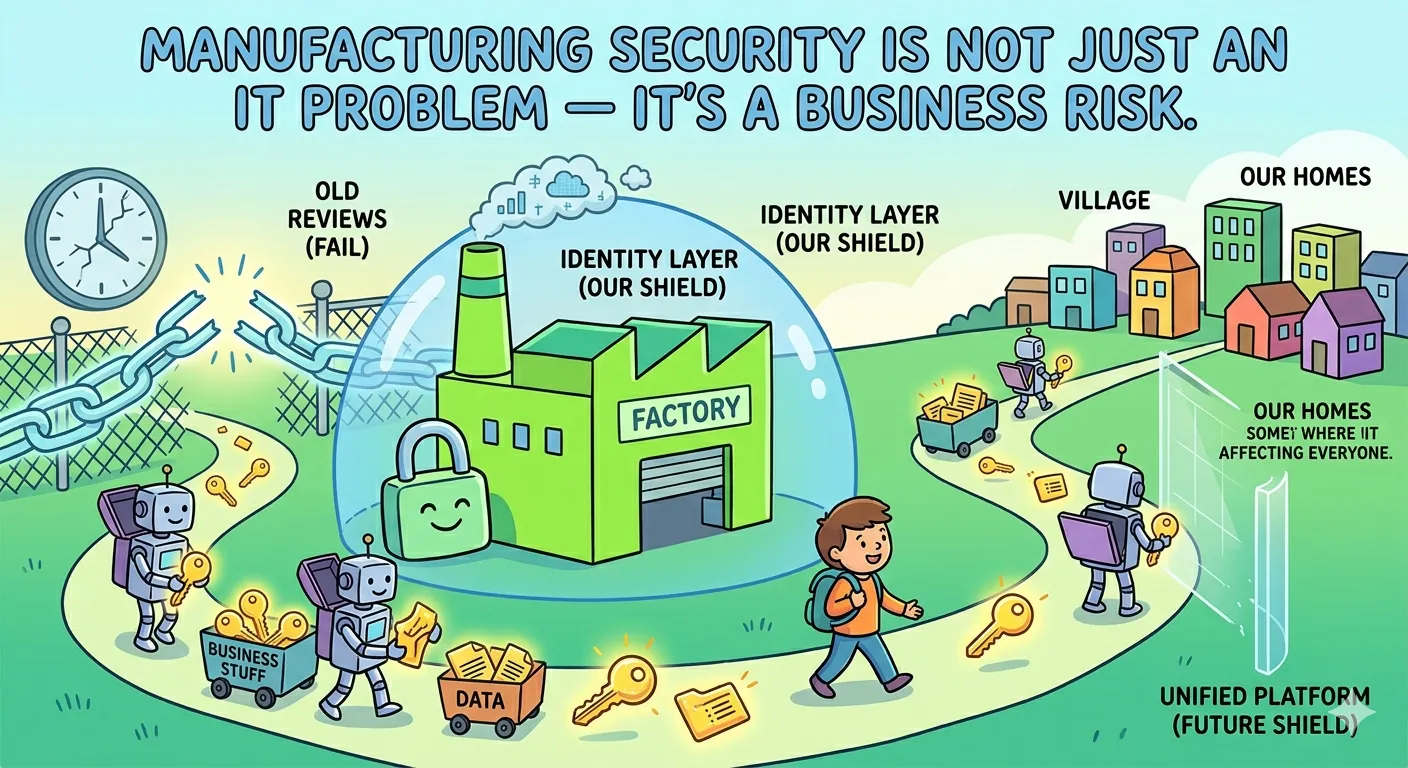
It’s Not Just About AWS, It’s About Identity Strategy
Cloud platforms are evolving fast, but identity management isn’t keeping up. Enterprises need to govern access across environments, applications, and user types, whether that’s a sales rep using Salesforce, a developer accessing GitHub, or a customer logging into your mobile app.
This is where OpenIAM changes the game.
OpenIAM: Because IAM Can’t Be an Afterthought
OpenIAM offers a unified platform for managing identities and access across cloud, on-prem, and hybrid environments. But beyond ticking technical boxes, it’s about empowering IT and security teams to enforce policies proactively, without slowing down innovation.
Here’s how OpenIAM fills the critical gaps left by AWS IAM:
1. Role Management that’s Intentional, Not Inherited
Default roles are built for convenience, not security. OpenIAM helps you define roles based on actual business needs, not vendor-generated templates. You can dynamically assign permissions based on department, job title, or location, enforcing least-privilege from day one.
2. Lifecycle Automation Built on Real Events
With OpenIAM, user provisioning and deprovisioning are automatically triggered by HR or IT events. A resignation in Workday? Access is revoked instantly. A role change? Permissions are updated without delay. No more stale accounts lurking in your cloud.
3. Context-Aware Access Controls
OpenIAM adds layers of context, such as location, device type, or behavior, to every access decision. It’s the kind of granularity AWS IAM can’t offer on its own, especially in a multi-cloud setup.
4. Unified Compliance and Audit Readiness
When an audit comes knocking, do you know who accessed what, and when? OpenIAM maintains detailed audit trails and generates compliance-ready reports across all connected systems. No spreadsheets. No blind spots.
5. CIAM Support Out of the Box
Need to manage millions of customer identities as securely as your internal workforce? OpenIAM’s CIAM capabilities help you do just that, with seamless self-service features and built-in security layers.
The Real Cost of Doing Nothing
The threat of IAM role exploitation isn’t theoretical. It’s real, rising, and alarmingly overlooked. According to Gartner, 75% of cloud security failures by 2025 will stem from IAM misconfigurations, not vulnerabilities in cloud platforms themselves.
Relying on default roles or manual governance is no longer tenable. Attackers know what to look for. And in today’s hyper-connected environments, one compromised identity can have ripple effects across your business.
A New Identity Strategy Starts Here
Here’s the truth: AWS may be your cloud provider, but it shouldn’t be your IAM strategy.
With OpenIAM, you get a platform that:
- Automates identity lifecycle across all systems
- Consolidates governance in one place
- Eliminates over-privileged access before it’s exploited
- Makes compliance a built-in outcome, not a fire drill
- Supports both workforce and customer identity use cases
Security shouldn’t depend on luck, or defaults.
Let OpenIAM help you build an identity foundation that’s secure, scalable, and future-ready.

















Sign in to leave a comment.