Enterprise data storage relies heavily on network-attached storage infrastructure to maintain availability, scalability, and performance. For decades, administrators have depended on Redundant Array of Independent Disks (RAID) configurations to protect their data against physical drive failures. RAID provides necessary hardware-level redundancy, ensuring that a single disk failure does not result in catastrophic data loss.
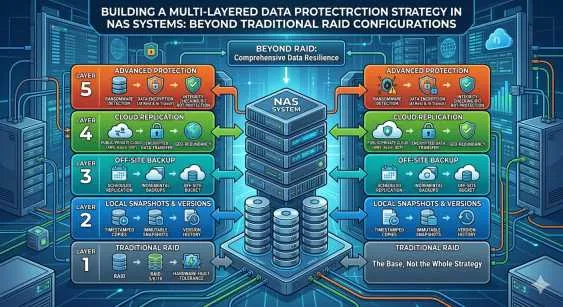
However, relying solely on RAID is no longer sufficient to secure critical enterprise data. Modern threats have evolved beyond simple hardware degradation. Ransomware, accidental deletions, insider threats, and site-wide disasters expose significant vulnerabilities in traditional storage architectures. A comprehensive data protection strategy requires multiple layers of defense integrated directly into the storage environment.
Building a robust defense mechanism means shifting focus from mere hardware redundancy to comprehensive data resilience. Administrators must construct a multi-layered strategy that secures the data at the file, volume, and network levels. This guide details how to implement advanced security measures to protect your critical infrastructure.
Re-evaluating the Modern NAS System
A contemporary Nas System functions as much more than a simple file server. It acts as the central repository for unstructured data, virtual machine backups, and database archives. Because this infrastructure holds high-value assets, it frequently becomes the primary target for malicious actors. When ransomware encrypts a file share, a standard RAID configuration simply replicates the encrypted data across the array, rendering the redundancy useless against logical corruption.
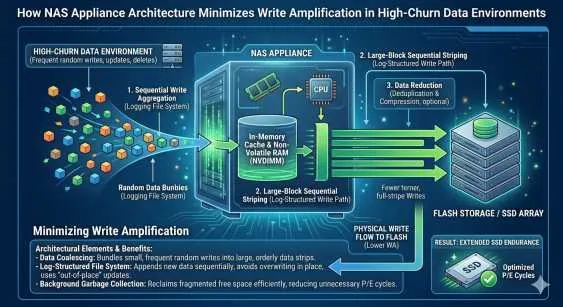
To build a resilient architecture, organizations must deploy a hardened NAS Appliance designed with advanced software-defined security features. A modern NAS Appliance integrates file-system level protections that operate independently of the underlying hardware disk arrays. By decoupling data protection from physical drive management, IT teams can establish discrete layers of defense that mitigate specific threat vectors.
Layer One: Advanced Access Controls and Network Segmentation
The first layer of defense in any Nas System involves strictly controlling who and what can access the storage environment. Administrators must enforce the principle of least privilege across all directories and volumes.
Implement Role-Based Access Control (RBAC) integrated with centralized directory services like Active Directory or LDAP. This ensures that users only have access to the specific file shares required for their functional roles. Furthermore, network segmentation isolates the NAS Appliance from public-facing networks and vulnerable endpoint segments.
Utilize Virtual Local Area Networks (VLANs) and strict firewall rules to ensure that only authorized application servers and management interfaces can communicate with the storage infrastructure. Disabling legacy protocols such as SMBv1 and enforcing SMB encryption prevents unauthorized packet sniffing and lateral movement by threat actors within the network.
Layer Two: Immutable Snapshots for NAS
Point-in-time recovery mechanisms form the core of logical data protection. Traditional snapshots capture the state of a file system at a specific moment, allowing administrators to roll back changes. However, standard snapshots remain vulnerable to administrative credential compromise; if a threat actor gains high-level access to the Nas System, they can systematically delete all existing snapshots before executing a ransomware payload.
To neutralize this threat, organizations must implement Immutable Snapshots for NAS. Immutability guarantees that once a snapshot is created, it cannot be modified, encrypted, or deleted by any user or process—including system administrators—until a predefined retention period expires.
Deploying Immutable Snapshots for NAS creates a secure, read-only recovery point that survives even the most aggressive ransomware attacks. When building this layer, schedule Immutable Snapshots for NAS to occur at frequent intervals, such as hourly or daily, depending on the organization's Recovery Point Objective (RPO). Because these snapshots track only block-level changes, they consume minimal storage capacity on the NAS Appliance while providing a highly granular recovery timeline.
Layer Three: Air-Gapped Replication and Tiering
While Immutable Snapshots for NAS protect against logical corruption and ransomware, they do not secure the data against physical disasters that destroy the primary data center. A multi-layered strategy must include offsite replication to establish a true disaster recovery protocol.
Configure the primary NAS Appliance to replicate its data asynchronously to a secondary NAS Appliance located in a geographically distinct data center. To further enhance security, maintain a logical air gap between the primary and secondary sites. This means the replication target does not reside on the same active domain and utilizes discrete authentication credentials.
For organizations leveraging hybrid cloud architectures, object storage tiering provides an excellent alternative or supplement to a secondary physical site. Configure the Nas System to automatically push encrypted, immutable backups to a Write Once, Read Many (WORM) compliant cloud storage bucket. This approach satisfies the 3-2-1 backup rule by maintaining three copies of data, on two different media types, with one copy stored securely offsite.
Layer Four: Active Monitoring and Anomaly Detection
Passive defenses must be paired with active monitoring to detect threats before they cause widespread damage. Modern storage platforms utilize machine learning algorithms to establish a baseline of normal file access patterns, read/write speeds, and encryption activities.
When the Nas System detects an anomaly—such as a massive spike in file modification requests or the rapid renaming of file extensions typical of a ransomware execution—the system automatically triggers defensive protocols. These automated responses can instantly sever vulnerable SMB connections, generate an emergency alert to the Security Operations Center (SOC), and automatically trigger a new, out-of-band snapshot to preserve the data state immediately prior to the detected attack.
Securing Your Storage Infrastructure
Relying exclusively on traditional RAID configurations leaves enterprise data highly vulnerable to modern logical and physical threats. Hardware redundancy handles disk failures, but it provides zero defense against malicious encryption, accidental deletion, or site-wide catastrophes.
By transitioning to a multi-layered security model, organizations can safeguard their most critical digital assets. This requires deploying a robust NAS Appliance equipped with advanced access controls, behavioral monitoring, and offsite replication capabilities. Most importantly, integrating Immutable Snapshots for NAS ensures that administrators always retain a pristine, unalterable copy of their data for immediate recovery. Systematically applying these defensive layers transforms your storage infrastructure from a passive repository into a highly resilient fortress capable of withstanding the complexities of the modern threat landscape.


















Sign in to leave a comment.